Think of NIST Special Publication 800-53 less like a rigid rulebook and more like an encyclopaedia of security best practices. It’s a massive catalogue of security and privacy controls developed for all U.S. federal information systems, excluding those tangled up in national security. For everyone else, it provides a foundational framework for managing risk and building genuinely secure products.
A practical example is a medical device manufacturer. Instead of guessing what “secure” means, they can use NIST 800-53’s control SI-7 (Software, Firmware, and Information Integrity) as a blueprint for creating a secure update mechanism, ensuring that only authenticated software patches can be installed on their devices.
The Role of NIST 800 53 in Modern Product Security
At its heart, NIST 800-53 gives you a structured but surprisingly flexible roadmap for wrangling risk throughout a product’s entire lifecycle. While it was born out of the needs of U.S. federal agencies, its thorough and practical nature has made it the global gold standard for anyone who needs to prove they’ve done their security homework.
This framework cuts through the usual vague security principles, offering specific, actionable controls that engineering and security teams can actually implement. These controls are neatly organised into families, covering everything from basic access control all the way to complex supply chain security. It’s this systematic approach that makes it so valuable for manufacturers trying to build security in from the ground up, not bolt it on as an afterthought.
Building a Foundation for Compliance
For any company with an eye on the European market, getting to grips with this framework is more important than ever. Upcoming regulations, especially the EU’s Cyber Resilience Act (CRA), are setting a very high bar for security assurance. The good news is that NIST 800-53 provides a ready-made structure to help meet these tough new demands.
The framework’s influence is ballooning, particularly as new European regulations take shape. In the EU’s drive towards stricter cybersecurity rules like the CRA, NIST SP 800-53 has become a key benchmark for manufacturers and IoT vendors in the ES region. Revision 5, which landed on 23 September 2020, expanded the framework to 20 control families with over 1,000 individual controls. Crucially, it added new controls addressing modern threats like supply chain risks that map directly to the CRA’s Annex II requirements.
Recent analysis shows the global NIST 800-53 compliance sector for data centres has already hit USD 2.91 billion, and European adoption is surging by roughly 25% year-over-year in industries impacted by these new ES rules.
The real power of NIST 800-53 lies in its adaptability. It isn’t just a checklist; it’s a risk management tool that helps you create a defensible security posture tailored to your specific product and its operating environment.
By implementing its controls, you’re doing far more than just ticking boxes. You’re building a resilient security architecture—one that can stand up to regulatory scrutiny and, more importantly, earn the trust of your customers. For example, implementing AC-4 (Information Flow Enforcement) isn’t just a technical task; it’s a way to prove to regulators that your smart camera only sends data to trusted servers, protecting user privacy.
Navigating the NIST 800-53 Control Families
Think of the NIST 800-53 framework as a detailed building code for your digital product. Just as a builder consults architectural plans with specific sections for electrical, plumbing, and structural integrity, your security teams can turn to this framework for clear guidance. It organises its massive catalogue of safeguards into logical groups called control families.
Each family addresses a distinct area of security, from personnel screening to system maintenance. Within each family are the individual controls—the specific security and privacy measures your organisation can implement. Many controls also have enhancements, which are extra specifications that dial up the strength of a control, allowing you to make precise adjustments based on risk. For example, control AC-11 (Session Lock) has an enhancement (AC-11(1)) that requires the session lock to be pattern-hiding, a useful feature for mobile devices.
This hierarchical structure is exactly what makes the framework so practical. You don’t have to tackle all 1,000+ controls at once. Instead, you can focus on the families most relevant to your product and the specific risks it faces.
Core Control Families For Product Manufacturers
For software and IoT vendors preparing for regulations like the EU’s Cyber Resilience Act (CRA), a few control families stand out as particularly important. Getting these right provides a solid foundation for building a defensible security posture.
- Access Control (AC): This family is all about making sure only authorised users can access your product and its data. It governs who can do what. For an IoT device, this might mean implementing strong password policies (AC-7) or ensuring the device locks after a period of inactivity (AC-11).
- System and Information Integrity (SI): This one focuses on protecting your product from unauthorised modification or destruction. A critical control here is SI-7 (Software, Firmware, and Information Integrity), which ensures that updates come from a trusted source and haven’t been tampered with—a core requirement of the CRA. A practical example is using digital signatures to verify every firmware update before it is installed.
- Supply Chain Risk Management (SR): A newer addition in Revision 5, this family addresses risks from third-party suppliers and components. It’s absolutely vital for modern products, which almost always rely on open-source libraries or third-party hardware. An example is SR-4 (Acquisition Strategies, Tools, and Methods), which requires you to vet the security practices of your suppliers, perhaps by reviewing their SOC 2 reports or security questionnaires before integrating their code.
The table below shows how these NIST control families can be directly mapped to the security requirements found in the EU Cyber Resilience Act, offering a practical pathway to compliance.
Key NIST 800 53 Control Families for CRA Compliance
| NIST Control Family | Description | Example Control (ID) | Relevance to CRA Requirements |
|---|---|---|---|
| Access Control (AC) | Manages who can access systems and data, ensuring least privilege and secure authentication. | AC-2 (Account Management) | Aligns with CRA's secure-by-default principles, preventing unauthorised access through robust user account lifecycle management. |
| System and Information Integrity (SI) | Protects against unauthorised modification or destruction of information and systems. | SI-7 (Software, Firmware, and Information Integrity) | Directly supports CRA's requirement for secure and authenticated software/firmware updates, preventing tampering. |
| Supply Chain Risk Management (SR) | Addresses risks from suppliers, components, and third-party services. | SR-3 (Supply Chain Controls and Processes) | Essential for meeting CRA's SBOM and third-party component transparency obligations. |
| Configuration Management (CM) | Establishes and maintains consistent configurations of hardware, software, and firmware. | CM-6 (Configuration Settings) | Maps to CRA's secure configuration requirements, ensuring products are shipped with hardened, secure defaults. |
By focusing on these core areas, manufacturers can build a strong, evidence-based case for their product's security posture, satisfying both regulators and customers.
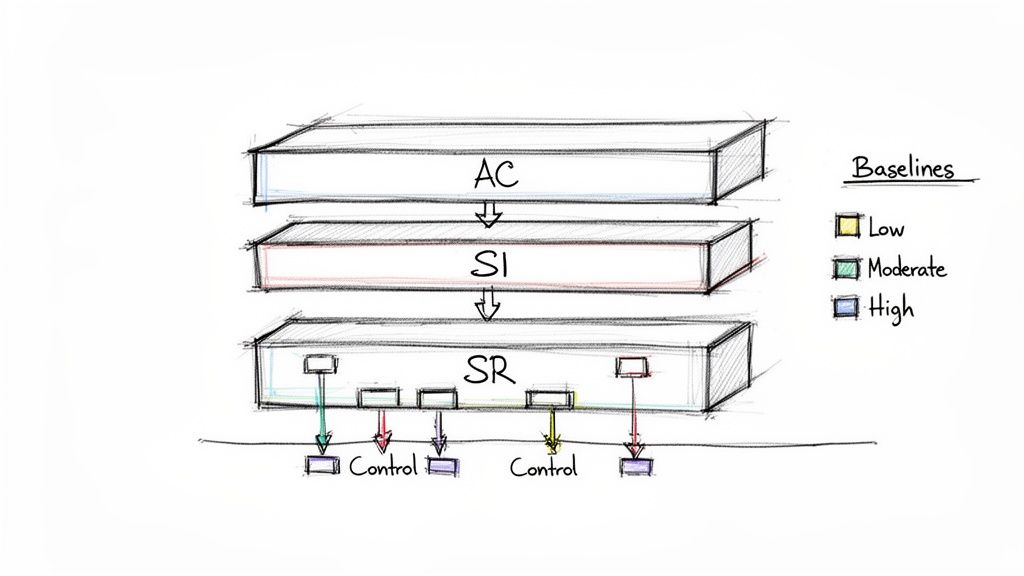
Understanding Security Baselines
To stop organisations from getting overwhelmed, NIST provides three predefined starting points, or baselines, for selecting controls: Low, Moderate, and High. Each baseline is a pre-selected set of controls designed to protect a system based on the potential impact if it were compromised.
Think of baselines as starter templates. A low-impact system, like a simple marketing website, has a much smaller set of required controls than a high-impact system, such as an industrial controller for critical infrastructure.
These baselines correspond directly to the risk classifications found in regulations like the CRA. By determining your product's potential impact, you can select the appropriate baseline. This gives you an initial set of relevant controls that you can then tailor to your specific product, which we’ll cover in the next section. As you navigate the NIST 800-53 control families, understanding what a vulnerability assessment entails is a key aspect of continuous monitoring and risk management.
How to Tailor NIST 800-53 Controls for Your Product
The real power of NIST 800-53 isn’t in its size, but in its flexibility. It's not a rigid, one-size-fits-all checklist you follow blindly. Think of it as a comprehensive security catalogue that you must carefully adapt—or tailor—to fit the specific context of your product, its operating environment, and the actual risks it faces.
Tailoring is the formal process of modifying a security control baseline to create a customised and, crucially, defensible set of safeguards. It involves scoping your system, selecting a starting baseline, and then systematically adding, removing, or tweaking controls to match your product's real-world security needs. This is an absolutely critical step for meeting regulations like the CRA without wasting time and money on irrelevant measures.
Done right, tailoring empowers your teams to move from a daunting list of over 1,000 potential controls to a focused, relevant, and manageable set that directly addresses your product’s risk profile. It’s all about being deliberate and documenting why certain controls are essential, why others don’t apply, and how you’ll compensate for any gaps.
The Tailoring Process Explained
The tailoring process isn't random; it follows a logical sequence designed to make sure every decision is risk-based and justifiable. You’re not just picking and choosing the controls you like. You're building a coherent security plan grounded in your product’s unique characteristics.
The main steps look like this:
- Identifying Common Controls: First, figure out which security controls you inherit from other systems or shared infrastructure. A practical example is leveraging your cloud provider's (like AWS or Azure) physical security controls. You don't need to implement your own data centre security because they've already done it for you.
- Applying Scoping Considerations: Next, decide which controls or specific control enhancements are simply not applicable to your product or its environment. For a smart thermostat that doesn't have a screen or keyboard, controls related to user session termination at the console (AC-12) could be scoped out.
- Selecting Compensating Controls: If a required control can't be implemented exactly as written, you can select an alternative measure that provides equivalent protection. For instance, if a legacy device cannot support multifactor authentication (IA-2), you might use network segmentation as a compensating control to isolate it.
- Assigning Organisation-Defined Parameters: Many NIST 800-53 controls include parameters that your organisation has to define. A clear example is control AU-4 (Audit Log Capacity), which requires you to define how long audit logs are kept before being overwritten. Your team might set this parameter to "90 days".
By working through these steps methodically, you create a tailored control set that is both effective and efficient. This becomes a cornerstone of your secure development practices. You can learn more about integrating these practices in our detailed guide on the secure software development life cycle.
Practical Example: IoT Smart Lock
Let's make this real with a common product: a smart home lock sold in the EU market. The manufacturer needs to comply with the CRA and decides to use the NIST 800-53 moderate baseline as its starting point.
Tailoring is where theory meets practice. It transforms the comprehensive NIST 800-53 library into a practical, actionable security plan that directly supports your product’s compliance journey.
During the tailoring process, the engineering team gets to the Physical and Environmental Protection (PE) family of controls.
-
PE-2 (Physical Access Authorisations): This control is about managing physical access to a facility. For a consumer smart lock, the manufacturer's own development centre is in scope, but the end-user's home is not. The team documents that controls related to facility access apply to their offices but are not applicable to the deployed product itself.
-
PE-3 (Physical Access Control): This control involves monitoring physical access points like doors and gates. Again, this is irrelevant for the product in a user's home. However, the team might implement a compensating control. For instance, they could beef up SI-7 (Software, Firmware, and Information Integrity) with strong anti-tampering alerts that notify the user if the lock's physical casing is opened.
-
PE-4 (Access Control for Transmission Medium): This control is about protecting physical wiring. The team scopes this out as not applicable since the device uses wireless protocols like Bluetooth and Wi-Fi, not physical cables.
This practical tailoring exercise results in a focused, relevant security plan. It ensures the manufacturer meets its CRA obligations by concentrating resources on what actually matters—like tamper resistance and secure updates—rather than on irrelevant controls designed for a data centre.
Mapping NIST 800-53 to EU Regulations Like CRA and GDPR
Adopting NIST 800-53 isn't just about bolstering your security posture; it's a strategic move that creates massive efficiencies when tackling tough EU regulations. Instead of treating each regulation as a separate, siloed project, you can use the framework as a powerful Rosetta Stone, translating one set of security efforts into evidence for multiple legal requirements.
This approach saves an incredible amount of time and resources. Rather than spinning up distinct compliance programmes for the Cyber Resilience Act (CRA) and the General Data Protection Regulation (GDPR), a NIST-aligned programme lets you establish a single, unified evidence base. You implement a control once, gather the proof, and then map that evidence back to the relevant articles in each regulation.
Creating a Unified Evidence Base
The secret lies in recognising the huge overlap between the goals of NIST 800-53 and EU digital policy. At their core, both aim to protect systems and data through robust risk management. NIST provides the detailed "how-to" instructions that directly support the high-level legal obligations set forth by the EU.
For example, Spanish manufacturers preparing for the EU's Cyber Resilience Act (CRA) are increasingly turning to NIST SP 800-53 as a foundational framework. This is because its mandatory roots in U.S. federal standards resonate with the ES region's regulatory harmonisation efforts. NIST 800-53 underpins regulations like FISMA and FedRAMP, which 100% of U.S. federal agencies must follow, and its controls are cross-mapped to ISO 27001—a certifiable standard embraced by over 70% of Spanish cybersecurity-compliant firms. The framework's prescriptive yet adaptable nature, updated in Rev. 5 to include supply chain risk management, positions ES businesses to confidently place products on the market.
Practical Mapping Examples
Let's look at how this works with specific controls. The connections are clear and direct, showing how a technical implementation directly satisfies a legal mandate.
-
Audit Logging for CRA and GDPR: The NIST control AU-2 (Audit Events) requires systems to generate audit records for security-relevant events. For a smart doorbell, this means logging every failed login attempt. For the CRA, these logs support post-market surveillance and vulnerability analysis. For GDPR, the same logs are essential for investigating and reporting a data breach within the required 72-hour window. One control, two compliance requirements met.
-
Secure Updates for the CRA: The control SI-7 (Software, Firmware, and Information Integrity) mandates mechanisms to verify the integrity and authenticity of software updates. This maps directly to the CRA's explicit requirement that manufacturers provide secure update mechanisms to address vulnerabilities. Your evidence for SI-7—such as documentation of your code signing process—becomes your proof of compliance for this part of the CRA.
By thinking in terms of control mapping, you shift from a reactive, regulation-by-regulation scramble to a proactive, build-once-use-many-times strategy. It’s the most efficient path to market access in the EU.
This unified approach streamlines audits and assessments in a big way. When a regulator or auditor asks for proof of compliance with a specific CRA or GDPR article, you can point directly to your implementation of the corresponding NIST 800-53 controls and the evidence you've already collected.
Aligning Privacy and Security Controls
The synergy extends deeply into privacy. The GDPR is fundamentally about protecting personal data, a goal that Revision 5 of NIST 800-53 explicitly supports with an integrated set of privacy controls. When mapping NIST 800-53 to EU regulations like GDPR, it's essential to understand practical applications; for an example of our commitment to data protection, you can review our Privacy Policy.
Controls within the System and Communications Protection (SC) family, like those for encryption (SC-8), and the Access Control (AC) family, which enforces data access rules, are foundational for GDPR. Implementing these doesn't just improve your product's security; it provides the technical safeguards required to protect EU citizens' data, fulfilling a core tenet of the regulation. A practical example is using encryption (SC-8) for all video streams from a smart camera to protect a user's privacy. This makes your journey to compliance more coherent and manageable. To dive deeper into the specifics, check out our guide on CRA vulnerability handling requirements.
NIST 800 53 Compared to Other Security Frameworks
While NIST 800-53 offers a comprehensive catalogue of controls, it's just one of several frameworks that organisations use. Understanding how it compares to others like ISO 27001 and SOC 2 is key to choosing the right approach for your products and your market.
| Aspect | NIST SP 800-53 | ISO/IEC 27001 | SOC 2 |
|---|---|---|---|
| Primary Focus | Security and privacy controls for U.S. federal information systems; widely adopted by private sector. | An Information Security Management System (ISMS); focuses on establishing, implementing, and maintaining security processes. | Trust Services Criteria (Security, Availability, Processing Integrity, Confidentiality, Privacy); focuses on service organisation controls. |
| Structure | A prescriptive catalogue of security and privacy controls organised into 20 families. | A risk-based framework with 114 controls in Annex A, but implementation is based on the organisation's risk assessment. | A set of principles-based criteria; the organisation defines its own controls to meet the criteria. |
| Applicability | Mandatory for U.S. federal agencies; popular for critical infrastructure and product manufacturers seeking high assurance. | Internationally recognised and certifiable; suitable for any organisation looking to demonstrate a mature ISMS. | Primarily used by service providers (SaaS, cloud) to provide assurance to customers about their systems. |
| Approach | Control-centric: start with a baseline of controls and tailor them based on risk. | Process-centric: start with risk assessment and build an ISMS to manage those risks. | Assurance-centric: provides a third-party audit report (Type I or Type II) on the effectiveness of controls over time. |
Each framework has its strengths. NIST 800-53 excels with its detailed, actionable controls perfect for product security engineering, while ISO 27001 is the gold standard for management systems, and SOC 2 is essential for building trust in the service economy. Many organisations find value in mapping controls between them to satisfy multiple stakeholder requirements at once.
A Practical Roadmap for Implementing NIST 800-53
Alright, let's move from theory to action. For any engineering or product team, a framework as comprehensive as NIST 800-53 can look like a mountain to climb. But it's not. The key is to break the process down into logical, repeatable phases.
Think of it as building a house. You don't just start throwing up walls. You start with a foundation, then frame it out, and then add the details. This phased approach turns an intimidating task into a structured and achievable project, integrating security right into your product development lifecycle. It’s about being deliberate, not scrambling at the last minute.
Step 1: System Categorisation
First things first: you need to understand what you're protecting and what could happen if it breaks. This is system categorisation. It’s about figuring out the real-world impact if your product’s confidentiality, integrity, or availability were compromised.
You have to consider the potential harm to your own organisation, your customers, other organisations, and even the nation. NIST keeps it simple with three impact levels: Low, Moderate, and High. For most software and IoT vendors, the conversation will centre on Low or Moderate.
- Low Impact: A breach would cause limited trouble. Think of a smart toaster. If it gets hacked, it might cause some minor disruption or user annoyance, but it's unlikely to cause significant harm.
- Moderate Impact: A compromise could have serious consequences. A smart home security system is a great example. A breach here could create genuine physical security risks for the user, like an intruder gaining access to the home.
Getting this right is foundational. Your decision here directly determines which security baseline you’ll use as your starting point.
Step 2: Control Selection and Tailoring
Once you've categorised your system, you grab the corresponding baseline of controls—Low, Moderate, or High. This gives you your initial security recipe. But remember, NIST 800-53 isn't a rigid, one-size-fits-all checklist.
This brings us to the most important part: tailoring. This is where you thoughtfully refine that baseline to fit your product's specific architecture, technology stack, and how it’s used in the real world. You’ll document which controls apply, which don’t, and where you might need a compensating control to achieve the same security goal.
This tailoring process is where you build your defensible security story. It’s not about doing less security; it’s about doing the right security for your product, backed by a clear and logical rationale.
For instance, if you're an IoT vendor making a connected thermostat, controls from the PE (Physical and Environmental Protection) family about protecting large physical facilities are probably irrelevant. Scoping them out as "not applicable" is a perfectly valid tailoring decision, as long as you document why.
Step 3: Control Implementation
Now we get to the hands-on part. This is where your engineering teams turn those tailored controls from words on a page into actual technical features and secure development practices. Implementation means weaving security into every single stage of your software development lifecycle (SDLC).
It’s a stage that demands tight collaboration. Compliance, security, and engineering teams have to be in sync to make sure the requirements are understood and built correctly.
Practical Example: Implementing SA-11
Let's take a common control, SA-11 (Developer Testing and Evaluation). This control is all about making sure developers test their code to find weaknesses before they become problems. Here’s how a software vendor might implement it:
- Integrate Static Application Security Testing (SAST) tools directly into the CI/CD pipeline. This automatically scans code for common flaws like SQL injection every time a developer tries to merge changes.
- Use Dynamic Application Security Testing (DAST) tools in staging environments. This tests the running application to find vulnerabilities that only appear when the code is live, such as cross-site scripting (XSS).
- Perform manual code reviews for the most critical components—think authentication logic or encryption modules. Automated tools are great, but a human expert can spot logic flaws they might miss.
These activities don't just make your product more secure; they become the hard evidence that you're meeting the SA-11 control. You can find a complete guide for managing these types of tasks in our Cyber Resilience Act compliance roadmap.
The diagram below shows how a solid framework like NIST becomes your bridge to meeting complex EU regulations.
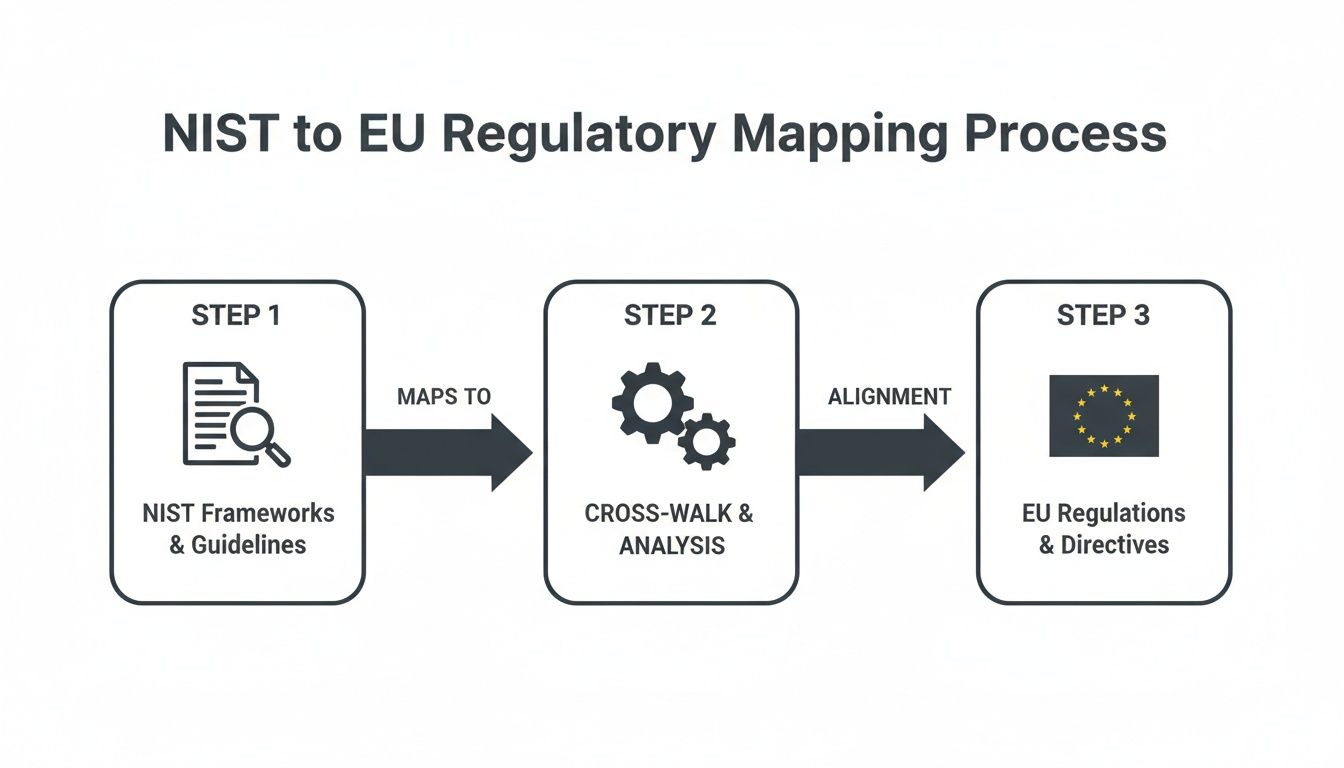
It’s a simple but powerful idea: start with a structured framework, map its controls to what the regulators want, and you’ve got a clear path to compliance.
Step 4: Control Assessment and Monitoring
Just building the controls isn't enough. You have to prove they work. The next step is to assess them to confirm they're implemented correctly, operating as intended, and actually achieving the security outcome you want. This means testing, reviewing documentation, and gathering evidence.
For our SA-11 example, your assessment evidence would include things like:
- The actual reports generated by your SAST and DAST tools showing zero critical vulnerabilities.
- Pull request comments and sign-offs from senior engineers showing that manual code reviews happened.
- Documentation of your process for handling and fixing any vulnerabilities that were found, such as tickets in your project management system (e.g., Jira).
Finally, remember that security is never "done." Continuous monitoring is what ensures your security posture stays strong over time. This means ongoing scanning, regular assessments, and updating controls as new threats pop up or your product changes. This ongoing vigilance is absolutely critical for maintaining compliance with regulations like the CRA.
Common Questions About Using NIST 800-53 for CRA
As manufacturers start digging into NIST 800-53 to meet the EU's Cyber Resilience Act (CRA), a lot of practical questions pop up. It’s a huge framework, and figuring out how to apply it to a new regulation can feel like a maze. This section tackles the most common queries we hear from teams on the ground, with clear, direct answers.
The idea is to cut through the noise and give you the confidence to move forward. We’ll cover the biggest points of confusion, from how the framework differs from formal certifications to where a smaller company should even begin. Think of it as a practical FAQ for your CRA journey.
Is NIST 800-53 a Certification Like ISO 27001?
This is a critical distinction and a very common question. The short answer is no. NIST 800-53 is a security framework, not a certification.
Unlike ISO 27001, where your organisation can go through a formal audit and get an official certificate, there’s no such thing for NIST 800-53. Instead, you "comply" by implementing the controls and documenting your work. The goal for CRA readiness isn't to get a certificate; it's to use the framework's detailed controls to build a strong, defensible security programme for your product.
The output of your NIST 800-53 effort is not a piece of paper. It's the collection of evidence—technical documentation, test results, and process records—that proves your product meets the CRA's essential security requirements.
This body of proof demonstrates due diligence and shows you’ve systematically tackled risks across the product lifecycle. That’s what will satisfy regulators, not a formal certificate.
Where Should a Small IoT Company Start with NIST 800-53?
For a smaller company, the sheer scale of the framework can be intimidating. The key is to avoid trying to boil the ocean. The best place to start is to formally categorise your product's security impact level, which will almost certainly be Low or Moderate.
This first step is crucial. It lets you select a baseline of controls, immediately narrowing your focus from over 1,000 possibilities to a much more manageable set. This stops your team from getting bogged down in controls that aren’t relevant to your product's actual risk profile.
Once you have that baseline, prioritise the foundational control families that map directly to the CRA's core principles. These include:
- Access Control (AC): For a smart plug, this means requiring a password to add it to a Wi-Fi network.
- System and Information Integrity (SI): This means having a secure, signed firmware update process to patch vulnerabilities.
- Supply Chain Risk Management (SR): This means generating a Software Bill of Materials (SBOM) to track open-source components.
By starting here, you address the highest-priority CRA requirements first and build a solid security foundation you can expand on later.
How Does NIST 800-53 Address Vulnerability Management for the CRA?
It tackles it head-on and in great detail, which makes it an excellent tool for meeting the CRA's strict vulnerability handling rules. Several control families work together to build a complete vulnerability management programme.
The control RA-5 (Vulnerability Monitoring and Scanning) gives you the mechanism for actively looking for weaknesses. A practical example is running a weekly vulnerability scan against your product's public-facing cloud services.
Next, SI-2 (Flaw Remediation) lays out the process for fixing what you find. This control requires you to install security updates and patches, mapping perfectly to the CRA’s requirement to provide security support for a product's expected life. For instance, this control would guide your policy to release a patch within 30 days of discovering a high-severity flaw.
Finally, the Supply Chain Risk Management (SR) family helps you manage vulnerabilities that come from third-party components, like open-source libraries—a major focus of the CRA. Implementing these controls gives you a structured, documented process for finding and fixing flaws, which is exactly what regulators want to see.
Can We Use NIST 800-53 if Our Product Handles GDPR Data?
Absolutely. In fact, using NIST 800-53 is an efficient way to build the technical foundation for GDPR compliance right alongside your CRA work. Revision 5 of the framework was specifically updated to better mesh privacy controls with security controls.
When you implement controls that govern access, auditing, and data protection, you are establishing the very safeguards that GDPR demands for protecting personal data.
For example, controls from the System and Communications Protection (SC) family, like SC-8 (Transmission Confidentiality and Integrity), which covers encryption, are fundamental to protecting data in transit. A practical application of this would be enforcing TLS 1.2 or higher for all data transmitted from a health-tracking wearable to its companion mobile app. This lets you build a unified compliance programme that addresses both cybersecurity (CRA) and data protection (GDPR) with a single set of technical measures, saving you a huge amount of time and effort.
Navigating the complexities of the Cyber Resilience Act requires a clear strategy and the right tools. Regulus provides a unified platform to assess CRA applicability, map requirements, and generate the tailored documentation you need to confidently place products on the EU market. Streamline your compliance journey and turn regulatory challenges into a competitive advantage. Discover how Regulus can simplify your path to CRA compliance.