The scope of the Cyber Resilience Act (CRA) determines which products, components, and organizations must comply with the EU’s new cybersecurity requirements. Because the CRA applies broadly to products with digital elements, understanding CRA scope is the essential first step for manufacturers, IoT vendors, embedded systems teams, importers, and distributors preparing for the 2025–2027 compliance deadlines.
In this extensive guide, we break down the full Cyber Resilience Act scope, explain which products are in scope, clarify what is out of scope, and show you how to perform an accurate CRA scope assessment using practical criteria and real examples.
For reference, you may also consult official guidance from the European Commission and cybersecurity recommendations from ENISA, both of which provide foundational context for understanding how the regulation applies to modern digital products.
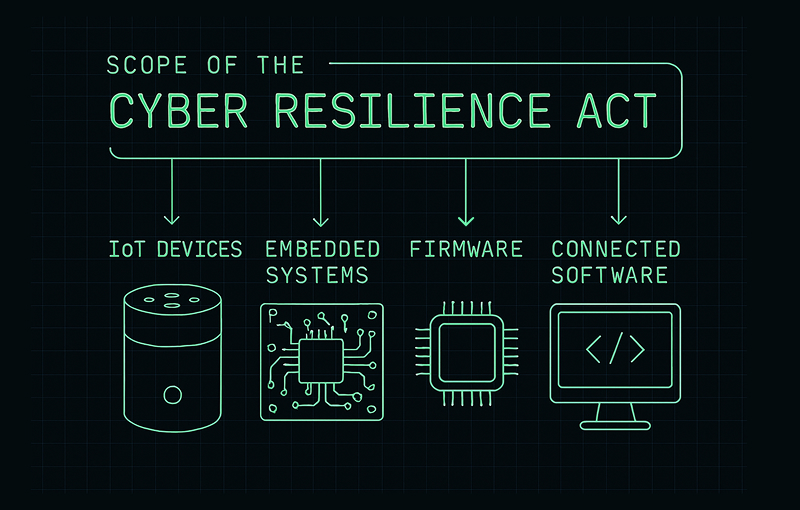
What the CRA Scope Covers
The scope of the CRA is intentionally broad. The regulation applies to any product with digital elements (PDE) placed on the EU market. A product with digital elements is defined as any hardware or software that includes programmable components or has connectivity capabilities. In practice, this means that the CRA covers most digital products sold today, from consumer IoT devices to industrial embedded systems.
The CRA scope also includes remote components that interact with the product during its lifecycle. This means update servers, configuration tools, companion applications, and cloud-connected elements may all be included as part of the same product system.
Products That Fall In Scope of the CRA
The following categories represent the core in-scope groups under the Cyber Resilience Act. When evaluating your own product, these categories provide a strong initial indicator that CRA obligations may apply.
1. IoT Devices and Connected Consumer Products (In Scope Under CRA)
Any device that connects to a network—either directly or indirectly—falls under Cyber Resilience Act scope. This includes:
- Smart home devices and hubs
- Sensors and connected monitoring equipment
- Wearables, trackers, and personal electronics
- Smart furniture and connected appliances
The EU has highlighted IoT as a major area of cybersecurity concern. In a 2022 ENISA report, over 60% of IoT products evaluated had basic security vulnerabilities. This explains why IoT is explicitly targeted in CRA scope.
2. Industrial IoT and Operational Technology (OT) Components
Industrial systems that include digital control, embedded firmware, or network communication are also included in scope. Examples:
- Industrial sensors and diagnostics units
- Robotics and automation components
- Connectivity modules for industrial equipment
- Gateway devices used in factories or energy systems
The CRA scope overlaps strongly with industrial cybersecurity guidance from NIST (National Institute of Standards and Technology), which also emphasizes lifecycle security requirements for industrial products.
3. Firmware and Embedded Systems (Always In Scope if Connected)
Firmware-driven products often represent the highest-risk categories. The CRA considers firmware a core digital element, meaning:
- Any programmable device
- Microcontroller-based systems
- Smart sensors or modules
- IoT chipsets and embedded platforms
…are all in Cyber Resilience Act scope if they connect or interface with networks.
4. Software With Connectivity Capabilities (In Scope Even Without Hardware)
Software is considered a product with digital elements if it connects to a network or communicates with other systems. This includes:
- Desktop software with online activation
- Cloud-connected configuration tools
- Mobile apps controlling hardware devices
- Developer tools that transmit telemetry
Even a simple update mechanism may be enough to bring software into CRA scope.
5. Cybersecurity Tools and Network Components (Explicitly In Scope)
The CRA explicitly covers products such as:
- Network firewalls
- VPN clients
- Identity and access management tools
Cybersecurity tools are regulated because vulnerabilities in these components have downstream impacts across entire ecosystems.
High-level overview of the core product categories included in the CRA scope.
Products That Are Out of Scope of the Cyber Resilience Act
Although broad, the CRA scope excludes products already covered by specialized regulations. These include:
1. Medical Devices (Covered by MDR/IVDR)
If a product is already regulated under EU Medical Device Regulation (MDR) or In-Vitro Diagnostic Regulation (IVDR), it is out of CRA scope.
2. Automotive Systems (Regulation 2019/2144)
Automotive components covered by type approval cybersecurity rules are excluded.
3. Aviation, Air Traffic Control and Aeronautics
Aviation systems fall under EASA frameworks, not the CRA.
4. National-Security Cryptography
Cryptographic products used exclusively for state security purposes are exempt from CRA requirements.
5. Pure SaaS Without Installable Components (Typically Out of Scope)
SaaS is generally considered a service, not a product. Therefore, SaaS-only platforms with no installed components are typically out of CRA scope. However, SaaS becomes in scope if it:
- Distributes firmware or installable agents
- Controls an in-scope hardware product
- Provides updates to a PDE
How to Perform a Proper CRA Scope Assessment
To determine whether your product falls under the Cyber Resilience Act scope, you must evaluate a series of criteria related to digital functionality, connectivity, and market placement. Below is a structured approach to performing a reliable CRA scope assessment.
1. Does the Product Contain Digital Elements?
If it includes software, firmware, embedded logic, or programmable components, it likely qualifies as a PDE.
2. Does It Connect to a Network (Directly or Indirectly)?
Many products qualify for CRA scope solely because they exchange data with other devices or servers.
3. Does It Process, Store or Transmit Data?
Any digital processing aligns with CRA scope unless the product is specifically regulated elsewhere.
4. Is It Placed on the EU Market?
CRA scope applies regardless of manufacturing location. If you sell, import, distribute, or integrate the product in the EU, CRA applies.
CRA Scope vs CRA Applicability
CRA scope determines whether your product is a product with digital elements. CRA applicability determines your obligations based on:
- Supply-chain role (manufacturer, importer, distributor)
- Product class (Default Class vs Critical Class)
- Function, risk level and use context
To understand the next step—determining applicability—read our full guide:
Cyber Resilience Act Applicability: Does the CRA Apply to Your Product?
Practical Examples of CRA Scope Classification
Examples of Products In Scope
- Smart thermostats and building automation devices
- Industrial monitoring sensors
- Connected lighting and HVAC controllers
- Desktop applications with auto-update functions
Examples of Products Out of Scope
- Medical imaging devices regulated under MDR
- Autonomous driving control units (vehicle regulation)
- Air traffic control platforms
- SaaS platforms with no installable components
Conclusion
The Cyber Resilience Act scope covers the vast majority of modern digital products, making Cyber Resilience Act scope assessment one of the most critical steps for manufacturers, software teams, and IoT vendors preparing for 2025–2027. Understanding whether your product is in scope helps determine classification, required documentation, vulnerability handling obligations, and the compliance roadmap necessary for market access.