The Cyber Resilience Act (CRA) introduces mandatory cybersecurity requirements for products with digital elements placed on the EU market. One of the most important questions companies face in 2025–2027 is: does the CRA apply to our product?
This guide provides a deep, expert-level analysis of CRA applicability, including how “products with digital elements” are defined, what exclusions exist, which edge cases matter, and how Default vs Critical Class classification is determined.
If you need a quick evaluation, start with our CRA Applicability Checker.
What Counts as a “Product With Digital Elements” Under the CRA?
The CRA applies to any Product with Digital Elements (PDE). This is a foundational definition and includes:
- Software (local, installable, on-device, or distributed binaries)
- Firmware (for hardware modules, chips, controllers, sensors)
- Connected hardware (consumer or industrial)
- IoT devices (smart home, industrial IoT, wearables, mobility devices)
- Embedded systems (MCUs, PLCs, automotive subsystems not regulated elsewhere)
- Hardware modules that interact with networks or run software
The test is straightforward: If the product runs software or firmware and can be updated or connected — it is almost always in scope.
Source: European Commission
Real-World Examples of Products In Scope
Software (installable packages)
- Desktop applications (Windows, macOS, Linux)
- Installable agents and clients for cloud services
- Security software, VPN clients, development tools
IoT Devices
- Smart home devices
- Connected industrial sensors
- Wearables, trackers, consumer electronics
Embedded systems and firmware-driven hardware
- Gateways, hubs, routers
- Microcontroller-driven devices
- Automated machinery components
Physical hardware with digital functions
- Robotics components
- Medical-device-adjacent equipment (if not regulated separately)
- Smart appliances
Products Not Covered by the CRA
Some categories are explicitly excluded:
- Pure SaaS without installables or on-device components
- Products regulated under sector-specific legislation (e.g., MDR, automotive UNECE)
- Open-source software developed outside commercial activity
- Products exclusively for national security, military or intelligence use
To understand whether your software counts as SaaS-only or “software with distributed components”, follow our guide: CRA Readiness Checklist.
CRA Applicability Decision Model
A simplified high-level model:
Is your product placed on the EU market?
|
+-- No → CRA does not apply
|
+-- Yes →
Is it a product with digital elements?
|
+-- No → CRA does not apply
|
+-- Yes →
Does it fit a sector-specific exclusion?
|
+-- Yes → CRA does not apply
|
+-- No → CRA applies
Once confirmed as in scope, classification becomes the next step.
Default vs Critical Class: Applicability of Classification
All CRA products fall into one of two categories:
- Default Class — standard digital product risk
- Critical Class — heightened risk based on impact on essential services or infrastructure
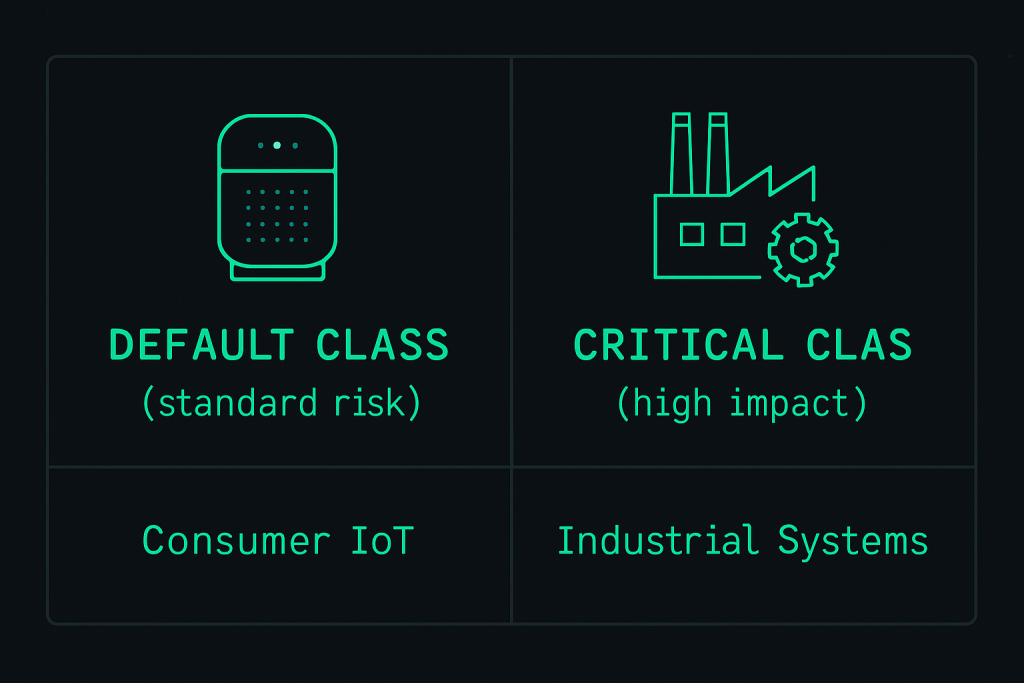
Default Class
Most products fall here. Typical examples:
- Consumer IoT devices
- Developer tools and software
- Productivity applications
- Embedded consumer devices
Critical Class
Criteria include:
- Products that perform core security functions
- Industrial systems where compromise could disrupt essential services
- Connectivity components such as routers, gateways, or control-plane modules
- Software critical to industrial automation or ICS environments
See the full mapping here: CRA Applicability & Classification.
Economic Operator Applicability
The CRA applies to all economic operators:
Manufacturers
They carry primary responsibility for compliance, documentation, vulnerability management, and secure development.
Importers
Must verify CRA conformity before placing the product on the EU market.
Distributors
Must confirm documentation and compliance before making the product available.
Operators are defined according to the New Legislative Framework (NLF).
Special Applicability Cases (Important)
Does the CRA apply to libraries and SDKs?
Yes — if they are distributed commercially or embedded into products placed on the EU market.
Does the CRA apply to developer tools?
Yes, unless exclusively used internally and never placed on the market.
Does the CRA apply to cloud-connected devices?
Yes. Even if the cloud is SaaS, the device and its firmware are PDEs and therefore regulated.
Does the CRA apply to mobile apps?
Yes, because they are software placed on the EU market and receive updates.
Does the CRA apply to web apps?
Only if they include installable components, local agents, drivers or distributed executables.
Checklist: How to Evaluate Whether the CRA Applies
You can use the following checklist to self-assess:
- Does your product run software or firmware?
- Does it connect to a network?
- Does it receive updates?
- Is it offered to customers in the EU?
- Is it part of a supply chain (OEM, ODM, integration)?
- Does it perform a function relevant to security or connectivity?
- Is it deployed in or adjacent to critical infrastructure?
If the answer to most of these is “yes”, the CRA applies.
How to Evaluate CRA Applicability Automatically

To simplify classification and applicability analysis, you can use our automated tool:
➡ Try the CRA Applicability Checker
It helps identify:
- Product category
- Default vs Critical Class
- Manufacturer / importer / distributor role
- Documentation implications
- Next steps for compliance
External Resources
- European Commission – CRA announcement
- ENISA – EU Cybersecurity Agency
- NIST Secure Software Development Framework
Conclusion
The Cyber Resilience Act marks a major shift in cybersecurity regulation for digital products. Understanding whether the CRA applies to your product is the first and most critical step in building a compliance strategy for the 2025–2027 transition period.
To continue your preparation, explore: Cyber Resilience Act Resources.
Starting early is the easiest way to reduce risk and cost.
Once CRA applicability is clear, the next step is to plan implementation. Our Cyber Resilience Act compliance roadmap explains how to move from analysis to execution.