When you’re talking about web application security testing, the OWASP Testing Guide (OTG) is the framework that everyone builds on. It’s the industry-standard playbook, giving you a complete methodology and practical techniques to find and fix security vulnerabilities.
What Is the OWASP Testing Guide
The OWASP Testing Guide is essentially a detailed manual for testing web applications in a consistent and thorough way. People often confuse it with the OWASP Top Ten, but they serve different purposes. The Top Ten tells you what the most critical security risks are, while the Testing Guide shows you how to find them.
At its core, the guide is all about improving application security by giving security professionals, developers, and QA teams a structured process to follow. It covers the entire testing lifecycle, from gathering initial information about an application all the way through to reporting your findings. This systematic approach is what makes it such a powerful tool for any organisation serious about building secure software.
The official project page, shown below, is the central hub for the guide, with links to the latest version, chapters, and specific test cases.
Think of this landing page as your starting point for diving into any of the detailed testing procedures.
Core Purpose and Structure
The main goal of the OTG is to standardise the web application security testing process. It stops testing from being an ad-hoc or incomplete activity by ensuring it’s repeatable, methodical, and covers all the critical areas you need to check. By following its structure, teams can be confident they haven’t overlooked a major vulnerability category.
The guide organises the testing process into several key phases:
- Information Gathering: This is where you map out the application’s architecture and figure out its potential attack surface. For example, using tools like
sublist3rto find subdomains ornmapto identify open ports on the server. - Configuration and Deployment Management Testing: Here, you verify the security of the server and application configurations. A practical example is checking for default admin pages (e.g.,
/admin) or exposed configuration files like.env. - Identity Management Testing: This phase assesses how the application handles user identities, including registration and de-provisioning.
- Authentication and Authorisation Testing: You’ll check how robust the login mechanisms and access controls really are. For instance, trying to access an admin URL (
/dashboard) while logged in as a standard user. - Session Management Testing: This involves analysing how user sessions are managed and protected from hijacking. A common test is to check if session cookies have the
SecureandHttpOnlyflags set. - Input Validation Testing: This is where you test for common but critical vulnerabilities like SQL injection and Cross-Site Scripting (XSS).
A key takeaway here is that the guide’s methodical structure is a massive help for meeting compliance frameworks. For example, it directly supports the EU’s Cyber Resilience Act (CRA) by providing a proven, auditable process for securing digital products from the ground up.
Mapping The Core OWASP Testing Categories
To get real value out of the OWASP Testing Guide, you first need to get your head around its structure. It’s not just a long list of tests; the framework is intelligently organised into distinct categories, each zeroing in on a specific slice of application security. Think of it as a detailed map that helps your team find the right tests for your app’s architecture and risk profile.
Every category is broken down into a series of highly specific test cases, each with a unique code like WSTG-INPV-05 for testing SQL Injection. This systematic approach is what makes testing both thorough and repeatable. It moves you away from ad-hoc checks and towards a structured, evidence-based security programme.
The diagram below shows how the guide fits into the bigger picture of security and compliance. It connects high-level principles, like the OWASP Top 10, with the hands-on testing needed to meet regulatory frameworks like the EU’s Cyber Resilience Act (CRA).
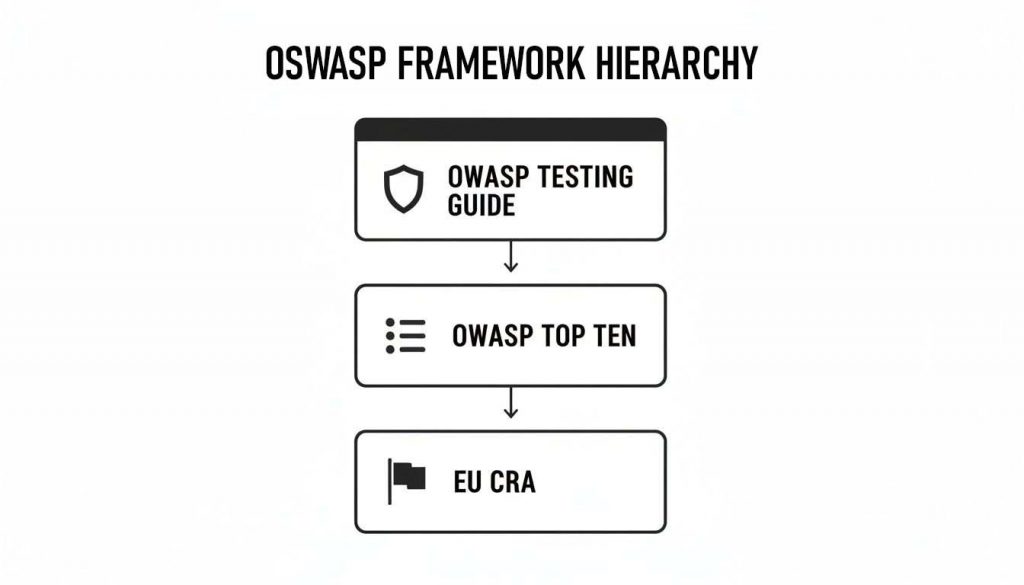
Essentially, the OWASP Top Ten tells you what the biggest risks are. The Testing Guide gives you the practical how-to for finding them, which in turn helps you satisfy the must-do compliance mandates.
To give you a clearer picture, here’s a quick-reference table summarising the core categories in the OWASP Testing Guide v4.2.
OWASP Testing Guide v4.2 Core Categories
| Category Code (WG) | Category Name | Primary Testing Objective |
|---|---|---|
| WSTG-INFO | Information Gathering | To map the application's attack surface and identify potential entry points. |
| WSTG-CONF | Configuration & Deployment Mgmt | To verify secure configuration of the underlying infrastructure and platforms. |
| WSTG-IDNT | Identity Management | To test user provisioning, modification, and deletion processes. |
| WSTG-ATHN | Authentication | To validate the strength and security of login and credential management mechanisms. |
| WSTG-AUTH | Authorisation | To ensure users can only access functions and data they are explicitly permitted to. |
| WSTG-SESS | Session Management | To examine the lifecycle and protection of session tokens and cookies. |
| WSTG-INPV | Input Validation | To test how the application handles malicious or unexpected user-supplied data. |
| WSTG-ERRH | Error Handling | To check for information leakage and security weaknesses in error messages. |
| WSTG-CRYP | Cryptography | To assess the implementation and strength of encryption for data in transit and at rest. |
| WSTG-BUSL | Business Logic | To identify flaws in application-specific workflows that can be abused. |
| WSTG-CLNT | Client-Side Testing | To uncover vulnerabilities like XSS and insecure data storage within the browser. |
| WSTG-APIT | API Testing | To test for security flaws specific to API endpoints, such as mass assignment or injection. |
Each of these categories contains a wealth of detailed test cases, forming a comprehensive framework for any security assessment. Let’s dig into a few of them.
Information Gathering and Configuration Management
Before you even think about running an active test, the Information Gathering (WSTG-INFO) phase is where it all begins. It’s pure reconnaissance. Testers work to map out the application’s entire attack surface, hunting down technologies, endpoints, and hidden content. For instance, a practical example is using Google Dorks (e.g., site:example.com filetype:log) to find publicly exposed log files that might reveal internal system paths or user data. The goal is a complete picture of every potential entry point.
Right after that comes Configuration and Deployment Management Testing (WSTG-CONF), which shifts focus to the infrastructure propping up the application. This is all about verifying that servers, frameworks, and cloud platforms are locked down. A classic practical example is checking for verbose error messages that leak stack traces or database query details when you submit invalid data to a form. Another is making sure critical HTTP security headers like Content Security Policy (CSP) are properly implemented.
Identity, Authentication, and Session Management
Many of the guide’s test cases directly address the critical risks outlined in the famous OWASP Top 10. This is especially true for identity. Authentication Testing (WSTG-ATHN), for example, targets everything from weak password policies to insecure password recovery flows. A common practical test is to attempt to register a new user with a weak password like “123456” to see if the application’s complexity rules reject it.
In the same vein, Session Management Testing (WSTG-SESS) dives into the tokens and cookies that maintain a user’s state after they’ve logged in. A typical practical example involves logging out of the application and then using the browser’s back button to see if you can access authenticated pages. If you can, it indicates that server-side session termination is not being handled correctly.
Input Validation and Cryptography
Input Validation Testing (WSTG-INPV) is arguably one of the most important categories. This is where you test for vulnerabilities like Cross-Site Scripting (XSS) and SQL Injection—flaws that arise from trusting user input. A practical example is submitting a search query containing <script>alert('XSS')</script>. If the application fails to sanitise the input and reflects it back to the browser, you’ve found a vulnerability. You can dive deeper into how these top vulnerabilities are identified in our detailed guide at https://goregulus.com/cra-basics/owasp-top-ten/.
The data collected for the OWASP Top Ten 2021 edition—which included EU-specific data from the ES region—revealed just how common these flaws are across over 500,000 applications globally. The OWASP Testing Guide v4.2 proved instrumental in tackling this; ES-based firms that applied its expanded test cases saw a 52% drop in related Common Weakness Enumeration (CWE) occurrences.
Applying Key Test Cases with Practical Examples

Knowing the OWASP Testing Guide’s structure is a great start, but the real value comes from applying its principles to find high-impact vulnerabilities. By concentrating on a few critical test cases, teams can quickly uncover and fix the kinds of weaknesses that attackers love to exploit.
This hands-on approach is what closes the gap between security theory and real-world application defence. Let’s walk through three of the most essential test cases, complete with clear, step-by-step examples you can try yourself.
Testing for SQL Injection (WSTG-INPV-05)
SQL Injection (SQLi) is still one of the most dangerous and common vulnerabilities out there. It happens when an attacker manages to manipulate the database queries an application makes. A successful SQLi attack can lead to total data exposure, giving them access to user credentials, personal information, or your company’s most sensitive secrets.
A surprisingly simple but effective way to check for this is by playing with input fields.
Practical Example: Login Form Test
- Identify an Input Field: Start with a standard user input, like the username field on a login page.
- Submit a Tautology: Instead of a real username, enter a basic SQL tautology such as
' OR '1'='1'--. This simple string is crafted to trick the database query’sWHEREclause into always being true. - Analyse the Result:
- Fail: If the application logs you in without a valid password, it’s vulnerable. The database blindly executed your malicious query.
- Pass: If you get a normal “invalid login” error or see that the input was sanitised (changed), the application is likely secure against this basic attack.
Testing for Cross-Site Scripting (WSTG-INPV-01)
Cross-Site Scripting, or XSS, gives attackers a way to inject malicious scripts into websites that other users trust. When a victim visits the page, the script runs in their browser, which can be used to steal session cookies, deface the site, or send the user to a phishing page.
The test is straightforward: inject a harmless script into an input that gets displayed back to you.
Practical Example: Search Bar Test
- Locate a Reflective Input: Find a search bar, comment box, or any form where what you type is shown back on the page after you submit it.
- Inject a Benign Script: Type a simple test payload like
<script>alert('XSS Test')</script>into the field and hit enter. - Observe the Browser’s Behaviour:
- Fail: If a pop-up alert box appears with the message “XSS Test,” the site is vulnerable. It ran your script because it failed to validate or encode the output properly.
- Pass: If you see the literal text
<script>alert('XSS Test')</script>on the page, the application is secure. It correctly treated your input as plain text, preventing the browser from executing it.
Identifying these flaws early is a cornerstone of a secure development lifecycle. Learn more about how static code analysis can help you find vulnerabilities like SQLi and XSS before they ever reach production.
Testing for Broken Authentication (WSTG-ATHN-*)
Broken Authentication is a broad category that covers all sorts of flaws in how an application handles user identity, login credentials, and session management. A classic and critical test case involves checking for weak password recovery features that accidentally leak information about valid users.
Practical Example: Password Reset Test
- Initiate Password Reset: Navigate to the “Forgot Password” page. You’re going to test it with two different email addresses: one you know is registered and one you know isn’t.
- Compare the Responses: Pay very close attention to the messages the application shows you after each attempt.
- Fail: The application is vulnerable to username enumeration if it gives different responses. For example, showing “Password reset email sent to registered@example.com” for the valid user but “User not found” for the invalid one. This confirms to an attacker which email addresses are tied to real accounts.
- Pass: The application is secure if it displays the exact same generic message for both attempts, something like, “If an account with this email exists, a reset link has been sent.” This approach prevents an attacker from figuring out which users are valid.
How to Automate OWASP Testing in Your CI/CD Pipeline

Effective security isn’t a one-off event; it has to be a continuous, integrated part of your development process. Manually running through the entire OWASP Testing Guide for every single release just doesn’t scale. This is precisely why embedding security into your Continuous Integration and Continuous Delivery (CI/CD) pipeline is so critical.
By doing this, you transform security from a manual bottleneck into an automated, non-negotiable quality gate. This approach, often called DevSecOps, makes sure that security checks run automatically at key points in the development lifecycle. The whole idea is to find and fix vulnerabilities early—when it’s cheapest and easiest to do so—rather than discovering them right before a major release or, even worse, in production.
Automating these checks gives you consistent, repeatable security coverage. Every code change gets scrutinised, which dramatically reduces the risk of human error and frees up your developers to focus on building features.
Integrating SAST in the Commit and Build Stage
The very first chance you get to catch a vulnerability is when a developer commits their code. Static Application Security Testing (SAST) tools are perfect for this stage because they analyse source code without needing to run the application at all. They can spot flaws like SQL injection or insecure configurations right there in the codebase.
You can set up your pipeline to trigger a SAST scan automatically on every git push or merge request. This gives developers immediate feedback, letting them fix issues before their code even gets merged into the main branch. It’s a powerful shift-left strategy.
Practical Example: GitLab CI with a SAST Scanner
A simple configuration in your .gitlab-ci.yml file can run a SAST job as a standard part of your pipeline.
sast:
stage: test
script:
- /analyzer run
artifacts:
reports:
sast: gl-sast-report.json
In this example, GitLab’s built-in SAST analyser runs during the test stage. If it uncovers vulnerabilities that exceed a predefined threshold, you can configure it to fail the build, stopping insecure code from moving any further.
Implementing DAST in the Staging Environment
While SAST checks the code, Dynamic Application Security Testing (DAST) tests the application while it’s actually running. DAST tools simulate real-world attacks, looking for vulnerabilities that only show up at runtime, like authentication flaws or server misconfigurations. You can find out more about how DAST works in our overview of Dynamic Application Security Testing.
The best place for DAST is after the application is built and deployed to a staging or testing environment. Here, the scanner can interact with a live application without any risk to your production users.
Automated DAST scans are a powerful way to operationalise the OWASP Testing Guide. Tools like the open-source OWASP Zed Attack Proxy (ZAP) can be configured to run a full suite of tests against your staging environment, providing a detailed report on any vulnerabilities found.
Practical Example: Jenkins Pipeline with OWASP ZAP
You can add a dedicated stage to your Jenkinsfile to kick off a ZAP scan against your staging URL. The process typically involves a few key steps:
- Spidering: First, ZAP “spiders” or crawls the application to discover all of its pages and API endpoints. It needs to know what to attack. For example, it would find
login.php,dashboard.php, andapi/v1/users. - Active Scanning: Next, ZAP launches an active scan, firing off malicious payloads to test for vulnerabilities like XSS, CSRF, and others from the OWASP Top 10.
- Reporting: Finally, the pipeline generates a report. From there, you can configure a security gate that fails the pipeline if any high-severity vulnerabilities are found, effectively blocking deployment to production until they’re fixed.
Aligning OWASP Tests with Cyber Resilience Act Requirements
The EU Cyber Resilience Act (CRA) is not about reinventing security. It’s about codifying existing best practices into mandatory requirements for any product with digital elements sold in the EU. For development teams, this is good news. The OWASP Testing Guide provides a practical, internationally recognised framework that translates the CRA’s legal language into concrete technical tests you’re likely already familiar with.
This alignment means your existing security testing programme can be your greatest asset for compliance. The structured test cases in the guide offer a clear, auditable path to demonstrating that your product is secure by design and by default—a core tenet of the CRA.
Satisfying Secure by Default Configurations
Annex I of the CRA is explicit: products must ship with a secure-by-default configuration. This isn’t just about avoiding weak passwords; it’s about minimising the attack surface and ensuring no known exploitable vulnerabilities exist when the product is placed on the market. This is where specific OWASP testing categories become directly applicable.
Think of these OWASP tests as the evidence you need to prove you’ve met this requirement. For example:
- WSTG-CONF-02 (Test Application Platform Configuration): This test is all about platform hardening. A practical example is verifying that debug mode is disabled in a production framework like Django or ASP.NET, as it can leak sensitive configuration data.
- WSTG-ATHN-02 (Test for Default Credentials): A fundamental check. Passing this shows you’ve ensured no default or easily guessable credentials are left in the product—a common and critical oversight.
- WSTG-INPV- (Input Validation Testing):* This whole family of tests is dedicated to preventing vulnerabilities like XSS and SQL injection. Successfully passing them demonstrates your product is resilient against the most common web-based attacks right out of the box.
Documenting the results of these tests creates a clear record of due diligence. It shows you’ve actively verified the security of your product’s default state before it ever reaches a customer. This documentation is exactly what you’ll need for the technical files required during CRA audits.
By mapping OWASP test results to specific clauses in Annex I, you create a compliance narrative that is easy for auditors to follow. Instead of just stating your product is secure, you provide empirical evidence from a globally accepted testing standard.
Demonstrating Secure Update Processes
The CRA places a massive emphasis on secure update mechanisms. It’s not enough to just provide updates; manufacturers must guarantee they are authentic, haven’t been tampered with, and are deployed securely. Again, the OWASP Testing Guide offers several test cases that directly assess the security of these critical processes.
Tests within the Authentication (WSTG-ATHN) and Cryptography (WSTG-CRYP) categories are vital here. For instance, testing the update server’s authentication ensures that only authorised administrators can push new firmware. Likewise, cryptographic tests can verify that update packages are correctly signed and that your product properly validates these signatures before installation, shutting the door on malicious updates.
Practical Example: Testing Update Integrity
Here’s a simple, real-world scenario for testing the integrity of an update process:
- Intercept the Update: Use a proxy to capture the update package as it’s downloaded by the product.
- Tamper with the Package: Make a small, identifiable change to the package binary. For example, changing a single byte in the file.
- Forward the Modified Package: Allow the product to receive the tampered update.
- Observe the Result:
- Pass: The product should reject the update, ideally with an error about an invalid signature. This result lines up with tests like WSTG-CRYP-03 (Testing for Weak Signature Algorithms).
- Fail: If the product installs the tampered package, you’ve found a critical vulnerability that directly violates the CRA’s requirements for update integrity.
OWASP Testing Guide Mapping to Key CRA Requirements
To make this connection even clearer, this table maps specific CRA obligations to relevant OWASP test cases. It provides a straightforward framework for structuring your compliance efforts and documentation.
| CRA Obligation (Example) | Relevant OWASP Testing Category | Example Test Case ID | Purpose |
|---|---|---|---|
| Protection from unauthorised access (Annex I, Sec 1) | Authentication (WSTG-ATHN) | WSTG-ATHN-04 | To test for weak password policies and prevent brute-force attacks. |
| Protection of data confidentiality (Annex I, Sec 1) | Cryptography (WSTG-CRYP) | WSTG-CRYP-01 | To test for weak transport layer security configurations (e.g., outdated SSL/TLS). |
| Ensuring integrity of updates (Annex I, Sec 2) | Identity Management (WSTG-IDNT) | WSTG-IDNT-05 | To test roles and permissions for update deployment functionalities. |
| No known exploitable vulnerabilities (Annex I, Sec 1) | Input Validation (WSTG-INPV) | WSTG-INPV-05 | To test for vulnerabilities like SQL Injection that could be exploited. |
By systematically applying the OWASP Testing Guide, your organisation can build a strong, evidence-based case for CRA compliance that is both technically sound and easy for regulators to understand.
Documenting OWASP Test Results for CRA Audits

Passing OWASP tests is only half the battle for Cyber Resilience Act compliance. Proving it through clear, auditable documentation is the other. Your technical file must contain robust evidence that your product has been methodically tested against known vulnerabilities. A well-structured test report provides this proof, turning your security efforts into a defensible compliance asset.
This structured approach isn’t optional. Conformity assessment bodies require clear, repeatable, and understandable evidence, and a simple pass/fail checklist just won’t cut it. Your documentation needs to detail the what, how, and why of your testing process to demonstrate a mature security posture.
Essential Components of a CRA-Ready Test Report
To make sure your documentation meets auditor expectations, every test finding should be captured in a standardised format. This consistency makes your technical file easy to navigate and understand, which can significantly speed up the audit process.
Each report entry should include these key components:
- Test Case ID: Use the official ID straight from the OWASP Testing Guide (e.g., WSTG-INPV-05). This immediately links your test to an industry-standard methodology.
- Test Description: Briefly explain the test’s objective. Think something like, “Testing for SQL Injection vulnerabilities on user authentication endpoints.”
- Tools Used: List every tool involved, whether it’s an automated scanner like OWASP ZAP or a manual proxy like Burp Suite.
- Steps to Reproduce: Provide a clear, step-by-step guide that another tester could follow to replicate the finding. This is absolutely critical for verification.
- Findings and Observations: Describe exactly what happened during the test. Back it up with evidence like logs, screenshots, or server responses.
This level of detail moves your report from a simple claim to verifiable proof—the cornerstone of any successful compliance audit.
Assessing Severity and Providing Remediation
Just identifying a flaw isn’t enough. Your documentation must also assess its potential impact and provide clear instructions for fixing it. This shows a proactive approach to vulnerability management, which is a core requirement of the CRA.
Your severity assessment should use a recognised framework like the Common Vulnerability Scoring System (CVSS). This gives you a standardised, objective measure of a vulnerability’s severity, helping you prioritise remediation work effectively. After the assessment, provide actionable advice.
A strong report doesn’t just say “XSS found.” It provides a code snippet showing the fix, links to secure coding guidelines, and confirms that the remediation has been validated.
Applying the OWASP Testing Guide brings significant security improvements, which is critical for CRA readiness. A 2022 study highlighted that using the guide on Java web applications boosted security optimisation scores by 64.8%. This is especially relevant since pre-2024 audits in Spain showed 67% of IoT products failing basic OWASP-aligned tests, putting them at risk of major EU fines. To learn more about these findings and their implications, explore the detailed research on application security optimisation.
Here’s a practical template for a single test case finding:
| Field | Example Content |
|---|---|
| Test Case ID | WSTG-ATHN-04 |
| Description | Test for weak password policies on the user registration page. |
| Tools Used | Manual testing with a web browser. |
| Steps to Reproduce | 1. Navigate to the registration page. 2. Enter user details. 3. Submit the password "password". |
| Findings | The system accepted the weak password "password" without enforcing complexity rules. |
| Severity (CVSS) | 7.5 (High) |
| Remediation | Enforce a minimum password length of 12 characters, requiring uppercase, lowercase, numbers, and symbols. Reject common passwords. |
Integrating OWASP Findings into Your Vulnerability Management
Spotting vulnerabilities with the OWASP Testing Guide is a great start, but it’s what you do next that really counts. A simple list of findings doesn’t protect anyone; you need to feed those insights into a structured vulnerability management and disclosure process. This is how you turn routine testing into a real driver of your product’s security and resilience.
This structured approach is also a central pillar of the Cyber Resilience Act (CRA). The regulation demands more than just finding flaws—it requires a documented, repeatable process for classifying, prioritising, and fixing them. Integrating OWASP test results gives you the technical evidence you need to build this workflow, ensuring your response is both effective and compliant.
Classifying and Prioritising Findings
When an OWASP test case fails, the first job is to figure out how bad it is. This is crucial for stopping your teams from chasing low-impact bugs while critical vulnerabilities are left open. Using a standardised system like the Common Vulnerability Scoring System (CVSS) is perfect for this, as it gives you an objective score based on things like attack complexity and potential damage.
Once you have a score, you need to prioritise the fix. This means mixing the technical CVSS score with real-world business context. For instance, a critical vulnerability (CVSS 9.8) in a rarely used internal tool might be less urgent than a medium-severity flaw (CVSS 6.5) in your main customer authentication API.
Practical Example: Triage Process
Let’s see how this works in practice.
- Finding: An
WSTG-INPV-01(Cross-Site Scripting) test fails on the profile page of your customer portal. - Classification: The security team calculates a CVSS score of 6.1 (Medium), mainly because it requires some user interaction to be exploited.
- Prioritisation: Despite the medium score, the issue is escalated to High Priority. Why? Because it affects a core customer-facing feature and could potentially lead to account takeovers, posing a serious business risk.
- Action: A ticket is immediately created in the development backlog with a strict service-level agreement (SLA) for the fix.
From Patching to Public Disclosure
A proper vulnerability management programme doesn’t stop at internal fixes. For serious flaws, especially those hitting your customers, you need a clear plan for communication and disclosure. This isn’t just about damage control; it’s about building trust with your users and proving you’re on top of your regulatory duties.
Your workflow should spell out the steps for creating security advisories, notifying affected users, and, when needed, publishing a Common Vulnerabilities and Exposures (CVE) entry. This formal disclosure process is a key part of the coordinated vulnerability handling requirements under the CRA. For a closer look at these duties, you can learn more about CRA vulnerability handling procedures and how to put them into action.
A mature vulnerability management programme, fuelled by consistent OWASP testing, provides credible evidence that you are proactively managing your product’s security lifecycle. This documented process is precisely what regulators and customers expect to see.
Frequently Asked Questions About OWASP Testing
This section answers some of the most common questions we hear about the OWASP Testing Guide and how to apply it in the real world. The goal is to give you clear, practical answers to refine your security programme.
What Is The Main Difference Between The OTG and The OWASP Top Ten?
This is a very common point of confusion, but the distinction is actually quite simple. The OWASP Top Ten is a high-level awareness document. It tells you what the ten most critical web application security risks are, based on broad industry data. Think of it as an executive summary of the biggest threats out there.
In contrast, the OWASP Testing Guide (OTG) is the detailed, practical manual that shows you how to find those risks and many others. It gives you the specific methodologies, test cases, and technical steps needed to uncover vulnerabilities. If the Top Ten is the “what,” the OTG is the “how-to.”
How Can Small Teams Start Using The OWASP Testing Guide?
If you’re a small team or new to the guide, trying to do everything at once is a recipe for overwhelm. A much more effective approach is to be pragmatic and risk-based.
Start by focusing on the most critical vulnerabilities that are most relevant to your application’s technology stack and business logic. A great way to begin is by concentrating on the test cases that map directly to the current OWASP Top Ten.
- Begin with Input Validation (WSTG-INPV): Prioritise tests for SQL Injection and Cross-Site Scripting (XSS). These are high-impact, incredibly common, and a fantastic place to start.
- Test Authentication (WSTG-ATHN): Check that your login and password reset functions are solid against common attacks like credential stuffing and weak password policies.
- Check Authorisation (WSTG-AUTH): Make sure users can’t access data or functionality they shouldn’t. For example, if an API endpoint is
/api/invoices/123, try changing the ID to/api/invoices/124to see if you can view an invoice that doesn’t belong to you. This vulnerability, often called Insecure Direct Object Reference (IDOR), is a classic and critical finding.
By starting with these high-priority areas, small teams can make a significant, immediate impact on their security posture without needing to master the entire guide from day one.
How Often Should We Perform OWASP Testing For CRA Compliance?
The Cyber Resilience Act (CRA) requires continuous vulnerability management, not just a one-off check. This means your testing frequency has to align with your development and release cadence to ensure you stay compliant.
For continuous CRA compliance, OWASP testing shouldn’t be a periodic event but an integrated part of your software development lifecycle. The goal is to make security a constant, automated process rather than an afterthought.
A solid, defensible testing schedule usually includes:
- Automated Scans (Daily/Per-Commit): Integrate SAST and DAST tools into your CI/CD pipeline. This helps catch common vulnerabilities with every single code change.
- Manual Penetration Testing (Quarterly/Annually): Conduct deeper, manual assessments based on the OWASP Testing Guide, especially after major feature releases or architectural changes. This is where you find the complex, business-logic flaws that automation misses.
- Targeted Testing (As Needed): When a new major vulnerability (like Log4Shell) is disclosed, perform specific, targeted tests to confirm your products are not affected and document your findings.
This layered approach ensures that security is consistently addressed, giving you the evidence needed to demonstrate due diligence under the CRA.
Regulus helps you translate these testing principles into a structured, auditable compliance strategy. Our platform maps your product’s requirements to specific CRA obligations, generates the necessary documentation templates, and provides a clear roadmap for achieving and maintaining compliance. Gain clarity and confidence by visiting https://goregulus.com.