For product manufacturers and IoT vendors, the ground has shifted. The old approach of a single, annual security check just doesn’t cut it anymore. Regulations like the EU’s Cyber Resilience Act (CRA) now demand continuous vigilance, forcing a move to more modern, agile security practices.
This is where Penetration Testing as a Service (PTaaS) comes in, emerging as a critical tool for meeting ongoing compliance and security demands.
The New Reality of Security for Product Manufacturers

Traditional, one-off penetration testing works like a photograph—it gives you a snapshot of your product’s security on a single day. While valuable, that picture is static. It quickly becomes obsolete in a world of continuous development cycles, frequent firmware updates, and a constant stream of newly discovered vulnerabilities.
For example, a traditional pen test performed in January on a smart camera’s firmware would not account for a critical open-source vulnerability discovered in March. The product would remain exposed until the next annual test.
This periodic model simply isn’t sustainable when you’re up against strict new regulatory frameworks. These regulations are pushing manufacturers to take full ownership of their product’s security, from the first line of code through its entire supported lifecycle.
The Challenge of Continuous Development
Think about a company that makes smart home devices. They push out firmware updates every quarter to add features and patch bugs. A traditional pen test done in January is already out of date by April. That leaves a massive window of risk where new, undiscovered flaws could be lurking.
As a practical example, a new feature allowing cloud-based video storage might inadvertently open a port that attackers could exploit. Without continuous testing, this flaw could go unnoticed for months, putting customer data at risk.
That gap creates a real problem. A vulnerability introduced in a routine update could be exploited, leading to compliance failures, serious reputational damage, and even a loss of market access. The old model can’t keep up with the speed of modern product development—or the persistence of attackers.
Penetration Testing as a Service (PTaaS) bridges this gap. It transforms security testing from an isolated event into a continuous, integrated process. This aligns security validation with the agile way you already build products, giving you a strategic advantage in managing vulnerabilities effectively.
A Strategic Move for Market Access
Adopting a continuous security model isn’t just a technical upgrade; it’s a strategic necessity. For any company selling products in the European Union, proving you have robust, ongoing security practices is non-negotiable. If you want to dig into the details, it’s worth understanding how the EU CRA revamp targets high-risk vendors and what that means for your business.
Penetration Testing as a Service delivers the consistent validation required to thrive in this new environment. It provides the concrete evidence you need for technical files, supports your post-market surveillance duties, and helps ensure your products stay secure and compliant from day one. It’s a proactive stance, and it’s essential for navigating the CRA and securing your place in the EU market.
What Is Penetration Testing as a Service

To understand Penetration Testing as a Service (PTaaS), it helps to start with what it replaces. Traditional, one-off penetration testing is like an annual doctor’s appointment—valuable, but it only gives you a snapshot of your product’s security on a single day.
PTaaS, in contrast, is more like wearing a continuous health monitor that feeds data to a team of specialists who are always on call. It shifts security testing from a periodic event into a continuous, integrated process, delivering a constant stream of insight into your product’s security posture.
Instead of waiting months for a static PDF report, the PTaaS model delivers findings through a live platform. It’s a modern approach built around combining the speed of automated tools with the irreplaceable nuance of human expertise.
The ‘As-a-Service’ Model Explained
The “as-a-service” element is the key differentiator. It means security testing is delivered on a subscription basis through a dedicated software platform, which becomes the central hub for all testing, reporting, and remediation activities.
For instance, a developer team can log into the PTaaS platform at any time and see a real-time dashboard of vulnerabilities across all their products, rather than searching through old emails and PDF files.
This model moves your security programme away from stressful, periodic audits and toward a state of constant readiness. For a deeper dive into how this approach provides a distinct cybersecurity advantage, other resources on Pen Testing as a Service (PTaaS) offer valuable context.
At its core, PTaaS is a hybrid model. It blends the efficiency of automated tools for broad coverage with the deep, contextual analysis that only skilled human pentesters can provide. This combination finds more vulnerabilities and provides more meaningful, actionable results.
This hybrid approach is what makes PTaaS so effective. An automated scanner might flag a potential low-risk issue, but a human analyst can validate it, determine its true business impact, and even chain it with other minor flaws to uncover a critical risk pathway. For example, a scanner might find an information-leakage bug. A human tester could then use that leaked information to bypass authentication on another part of the system, turning a low-risk finding into a critical one.
Practical Example: The Smart Thermostat
Imagine a company producing smart thermostats. A traditional pentest might find a low-risk vulnerability in the web dashboard, but the report arrives three months after development on that feature has already wrapped up. The finding lands in an inbox, and fixing it means disrupting current projects.
With PTaaS, the workflow is entirely different and far more efficient:
- Automated scanners run continuously against the thermostat’s cloud backend and firmware.
- The platform flags a potential cross-site scripting (XSS) flaw on the user settings page.
- A human pentester from the PTaaS provider is automatically notified of the automated finding.
- The expert validates the flaw, confirms it could be used to steal a user’s session cookie, and escalates its risk rating from ‘Low’ to ‘High’.
- A detailed finding—complete with a proof-of-concept—is published instantly on the PTaaS platform, which in turn automatically generates a ticket in the development team’s Jira board.
- Developers patch the flaw, deploy the fix, and then request a re-test directly through the platform with a single click.
This rapid, integrated cycle is perfectly suited for the agile development and post-market surveillance duties mandated by modern regulations. This is a key reason why third-party penetration testing services are seeing such wide adoption. They command a 71.30% market share in Europe, showing a strong shift towards specialised external expertise. For teams building complex products, our article on dynamic application security testing offers further context on related security methods.
Core Features and Service Models of PTaaS Platforms
Not all platforms offering penetration testing as a service are built the same. A truly robust PTaaS offering goes far beyond simple scanning, blending sophisticated software with human expertise to deliver a continuous, integrated security programme. Understanding the core features and the different service models is crucial for choosing a solution that fits your operational reality and budget.
An effective platform is built on several key components that work in tandem. These features are designed to embed security directly into your development workflow, turning it into a proactive and collaborative process rather than a reactive, one-off event.
Key Platform Features to Look For
A high-quality PTaaS solution should deliver more than just a list of vulnerabilities. It needs to provide tools that empower your team to act on findings quickly and efficiently.
- Centralised Management Dashboard: This is your single source of truth for security. It should provide a real-time, at-a-glance view of your entire product portfolio’s security posture, tracking ongoing tests, new findings, and remediation progress all in one place. For example, a product manager can instantly see that the new smart plug has two critical open vulnerabilities, while the older doorbell model is fully patched.
- Real-Time Vulnerability Reporting: Forget waiting weeks for a static PDF report. Findings should appear on the platform the moment they are discovered and validated by an expert, allowing your development team to start working on fixes straight away. A developer could receive an alert at 10 AM for a new vulnerability and have a patch ready by lunch.
- Direct Workflow Integrations: The platform must connect with the tools your team already relies on. Integrations with systems like Jira, Slack, or Azure DevOps can automatically create tickets for new vulnerabilities and notify the right people, cutting out manual steps and speeding up response times. A practical example is a high-severity flaw automatically creating a “P1” Jira ticket and pinging the on-call developer in a dedicated Slack channel.
- On-Demand Re-testing: Once you’ve deployed a fix, your team should be able to request a re-test with a single click. This rapid validation confirms that the vulnerability is actually resolved, closing the feedback loop much faster than with traditional testing methods.
- Direct Access to Security Experts: A key differentiator is the ability to communicate directly with the pentesters who discovered a vulnerability. This allows your developers to ask questions, get clarification, and receive guidance on tricky remediation challenges. For example, a developer could start a chat thread on the platform to ask the pentester, “Can you confirm if this proposed fix for the SQL injection is sufficient?”
Exploring PTaaS Service Models
The flexibility of penetration testing as a service extends to its business models, allowing organisations to align security spending with product development lifecycles and risk exposure. The growing demand for such adaptable options is clear, as the European penetration testing market is projected to swell from USD 1.11 billion in 2026 to USD 2.66 billion by 2034. Third-party managed services currently dominate with a 71.30% market share, driven by regulatory pressures and the need for independent validation. You can explore more about these trends in the full Europe penetration testing market report.
The right service model makes security scalable. It allows a global enterprise to secure hundreds of products continuously, while also enabling a startup to affordably test its first device before launch. The goal is to match security investment directly to business needs.
The most common models include:
1. Subscription-Based Model
Often called ‘all-you-can-test,’ this model provides continuous testing for a flat annual or monthly fee. It’s ideal for organisations with many products or those in rapid, agile development cycles.
- Practical Example: A large manufacturer of smart home devices with a wide product line and frequent firmware updates would choose a subscription. This gives them predictable costs and ensures all their products are continuously monitored, which is crucial for managing a secure software development life cycle. You can learn more about how to implement a secure software development life cycle in our detailed guide.
2. Pay-per-Test Model
This model allows you to purchase tests on an as-needed basis. It’s a great fit for smaller companies, startups, or for testing a single product before a major release.
- Practical Example: A startup launching its first connected medical sensor might opt for a pay-per-test model. This allows them to conduct a thorough, one-time security assessment before going to market without committing to a long-term contract.
3. Hybrid Model
Some providers offer a hybrid approach, combining a baseline subscription for critical assets with the option to purchase additional, on-demand tests. This offers a balance of continuous coverage and flexibility.
- Practical Example: An automotive supplier could use a subscription to continuously test the critical firmware in their main ECU and purchase separate, one-off tests for less critical infotainment apps as they are updated.
How PTaaS Directly Supports CRA Compliance
The EU’s Cyber Resilience Act (CRA) isn’t just about having good security; it’s about proving it. For manufacturers, this means building and maintaining a mountain of evidence to show you’re compliant, day in and day out. This is where Penetration Testing as a Service (PTaaS) shifts from being a simple security check to a core engine for generating that critical compliance evidence.
A traditional, one-off pentest report is a snapshot in time. It goes stale almost immediately, offering little help for the continuous post-market surveillance the CRA demands. PTaaS, on the other hand, creates a living audit trail of your security posture. Every test, finding, fix, and re-test is logged and timestamped, forming a solid foundation for your technical file.
Mapping PTaaS Outputs to Annex I Requirements
The CRA’s Annex I details the law’s essential cybersecurity requirements, with a huge focus on vulnerability handling. A PTaaS platform delivers direct, actionable evidence for many of these duties, turning abstract legal text into concrete, documented actions. This makes the whole compliance process far less daunting.
Think of the PTaaS platform as your compliance ledger. It doesn’t just find problems; it documents the entire lifecycle of each vulnerability, from the moment it’s discovered to the moment it’s verified as fixed. For example, an auditor can view a specific vulnerability (e.g., CVE-2023-1234), see the timestamp of its discovery, the Jira ticket number for the fix, the developer who committed the patch, and the timestamp of the successful re-test, all in one place. This is exactly the kind of detailed proof that regulators and notified bodies will be looking for.
The real power of PTaaS for CRA compliance is its continuous nature. It creates an unbroken chain of evidence showing you are proactively managing product security throughout its entire lifecycle, not just reacting to old reports.
A Practical Example of Compliance in Action
Let’s walk through a common scenario for an IoT device manufacturer. A new, critical vulnerability is found in a popular open-source library used in your product’s firmware. An annual pentest would miss this completely until the next scheduled test, leaving you unknowingly non-compliant and your customers at risk.
With PTaaS, the process looks very different—and it builds a clear evidence trail for auditors along the way.
- Continuous Monitoring Flags the Flaw: The platform’s integrated tools or expert testers spot the new vulnerability in your firmware, often within days of it being publicly disclosed.
- Instant Notification and Reporting: A detailed finding appears on the platform, complete with a severity score (like CVSS), a description of its potential impact on your specific product, and proof-of-concept details.
- Automated Workflow Integration: An automatic ticket pops up in your development team’s Jira board. It’s assigned to the right engineer and links directly back to the finding in the PTaaS platform, officially documenting that your remediation process has started.
- Remediation and On-Demand Re-testing: Your team develops and deploys a patch. Using the platform, they then request an immediate re-test targeting that specific vulnerability. The PTaaS provider’s experts validate the fix, often within 24-48 hours.
- Closing the Loop: The successful re-test is documented on the platform, the Jira ticket is closed, and the dashboard updates to show the risk has been resolved.
This entire workflow—from discovery to verified fix—is captured. The platform’s records serve as indisputable evidence for your technical file, demonstrating a robust and timely process for handling vulnerabilities as required by the CRA. To dive deeper, you can read our detailed guide on mastering CRA vulnerability handling to ensure your processes are fully compliant.
The diagram below shows the core features of a PTaaS platform that make this seamless workflow possible.
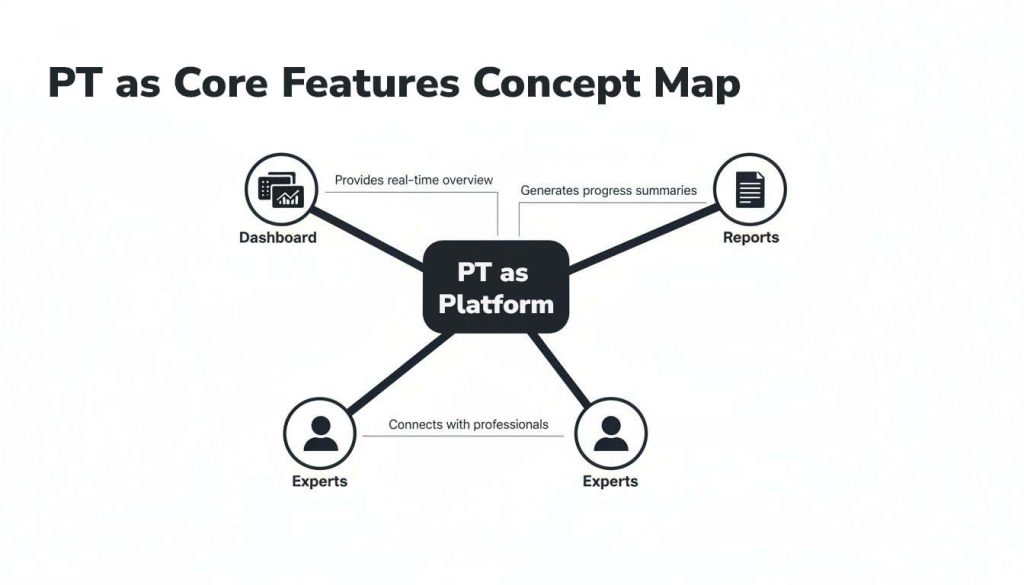
As you can see, the central platform connects the dashboard, reporting, and expert access to give you a unified view of your security activities—something that’s essential for streamlined compliance. This is what turns PTaaS from a simple testing activity into a comprehensive compliance management system.
Evaluating and Selecting the Right PTaaS Vendor
Choosing a partner for Penetration Testing as a Service isn’t just about ticking a box. It’s a critical decision that directly shapes your product’s security posture and your ability to meet compliance goals like the CRA. Not all PTaaS providers are created equal, especially when it comes to the unique challenges of IoT and embedded systems. You’re looking for a genuine security partner, not just another tool vendor.
This choice is becoming more significant as the market grows. Europe’s security testing market, which includes PTaaS, is forecast to hit €25.46 billion in 2026, then surge at a 23% compound annual growth rate to reach €130 billion by 2033. Research from Data Insights Market shows a major skills shortage is driving this, with 70% of organisations now depending on third-party solutions for their security testing. You can read more about the European security testing market growth on datainsightsmarket.com.
Essential Vendor Selection Criteria
When you’re evaluating potential PTaaS providers, a crucial first step is to thoroughly assess vendor risk and make sure they align with your own security and compliance standards. A generic checklist won’t cut it. You need to dig into criteria that prove the vendor actually understands your specific environment—from the hardware and firmware right up to the cloud services it connects to.
Your evaluation should be centred on these key areas:
- Proven Expertise in IoT and Embedded Systems: This is completely non-negotiable. Ask them for case studies or references from companies with products similar to yours. A vendor whose experience is mostly in web applications will likely miss the nuances of analysing firmware, radio protocols like BLE or Zigbee, and physical device security. For example, ask if they have experience with hardware-level attacks like fault injection or side-channel analysis.
- Industry-Recognised Certifications: You want to see that their testing team holds respected certifications. Credentials like CREST (Council of Registered Ethical Security Testers) and OSCP (Offensive Security Certified Professional) are a strong signal of high-level technical skill and a commitment to professional standards.
- Clear and Strong Service Level Agreements (SLAs): The vendor’s SLAs have to be explicit and meaningful. What’s their guaranteed turnaround for validating a new finding? After you deploy a fix, how fast will they re-test on demand? For agile teams, an SLA of 24-48 hours for re-testing is a good benchmark.
- Robust Integration Capabilities: The PTaaS platform must fit into your existing development world without friction. Make sure they have out-of-the-box integrations for your core tools—like Jira, Slack, or Azure DevOps—so you can automate workflows and ensure findings get actioned immediately.
What to Look for in a High-Quality PTaaS Report
The quality of a vendor’s reporting is a direct reflection of the quality of their service. A great report is far more than a data dump of vulnerabilities; it provides context, prioritisation, and clear, actionable guidance. It should be written for everyone from the C-suite to the engineers on the front line.
A world-class PTaaS report tells a story. It explains not just what is wrong, but why it matters to your business and exactly how to fix it. This clarity is what separates a basic vulnerability scan from a true penetration testing service.
Any comprehensive report from your PTaaS vendor must include these sections:
1. Executive Summary
This is the high-level overview written in plain business English for your non-technical stakeholders. It needs to summarise the overall risk posture, flag the most critical findings, and show how you’re tracking against previous tests.
- Practical Example: “The Q3 2024 testing cycle identified two critical and three high-risk vulnerabilities in the smart lock’s firmware. Remediation of these issues is our top priority to prevent potential unauthorised remote access.”
2. Detailed Technical Findings
Each vulnerability must be documented with technical precision. This means assigning a CVSS (Common Vulnerability Scoring System) risk rating, explaining which components are affected, and providing clear, reproducible steps that demonstrate the exploit.
- Practical Example: A finding for a buffer overflow should include the exact input that triggers it, memory dumps showing the crash, and an analysis of how an attacker could leverage it for code execution.
3. Actionable Remediation Advice
This is arguably the most important section. The vendor must provide specific, practical advice on how to fix each vulnerability, complete with code examples or configuration changes where possible. Vague recommendations like “sanitise user input” just aren’t good enough. For example, instead of just saying “fix the XSS,” good advice would be, “Implement output encoding on the user_name field on profile.php using the htmlspecialchars() function to mitigate the stored XSS vulnerability.”
4. Clear Evidence of Exploitation
Screenshots, logs, and video recordings are the undeniable proof of a vulnerability’s existence and impact. This evidence is vital for getting buy-in from development teams to prioritise fixes and serves as powerful documentation for compliance audits. For instance, a video could show the pentester using a simple script to unlock a smart door lock without any authentication.
Frequently Asked Questions About PTaaS for CRA
As manufacturers and product teams evaluate Penetration Testing as a Service, a number of practical questions tend to pop up. This modern approach to security testing is a significant shift from traditional methods, and getting a clear picture of its nuances is vital for building confidence and aligning it with your Cyber Resilience Act (CRA) compliance goals.
Below, we answer some of the most common questions we hear from teams getting started with PTaaS.
How Is PTaaS Different From a Vulnerability Scanner?
It’s a common question: isn’t penetration testing as a service just a fancier name for a vulnerability scanner? The answer is a hard no. Vulnerability scanners are automated tools that are great at flagging known issues based on a database of signatures, but they operate without context. This frequently leads to a flood of false positives and an inability to tell you the true business impact of a finding.
PTaaS, on the other hand, integrates automated scanning with indispensable human intelligence. Expert pentesters take the initial automated findings, validate them, and then actively try to exploit them. This hands-on work determines the real-world risk, delivering a much deeper and more accurate security assessment than a scanner could ever provide on its own.
The core difference is validation and impact. A scanner tells you a door might be unlocked, while a PTaaS expert actually picks the lock, walks inside, and shows you exactly what an intruder could get their hands on.
Can PTaaS Work for Hardware and Embedded Systems?
Yes, but this is where your choice of vendor becomes absolutely critical. PTaaS can be incredibly effective for complex hardware and embedded systems, but only if the provider has specialised expertise in IoT, Operational Technology (OT), and hardware security.
Unlike standard web application testing, securing a physical device demands deep knowledge of firmware analysis, radio protocols like Bluetooth Low Energy (BLE) or Zigbee, and hands-on debugging with tools like JTAG/UART.
A practical example: A PTaaS provider focused purely on web apps would almost certainly miss a critical flaw in a smart meter’s firmware that lets an attacker manipulate energy readings. A specialised IoT pentester, however, would know to analyse the firmware binary, probe the device’s physical interfaces, and uncover that kind of vulnerability. Always verify a vendor’s track record with physical products similar to your own.
Is PTaaS More Expensive Than Traditional Testing?
At first glance, a PTaaS subscription might seem more expensive than a single, traditional pen test. However, it often delivers far better value and a lower total cost of ownership over time. The “point-in-time” nature of traditional testing means you’re paying for a report that starts going out of date the moment you receive it.
With PTaaS, your subscription funds an ongoing security programme. The price typically includes continuous testing, on-demand re-testing of your fixes, and direct access to security experts. This model dramatically cuts the hidden costs that come with emergency fixes, potential data breaches, or the major non-compliance fines outlined in the CRA. For example, a single €15,000 traditional test might seem cheaper than a €30,000 annual PTaaS subscription. But if the subscription prevents a single data breach or compliance fine, which could cost millions, its ROI becomes clear. When you factor in the value of maintaining perpetual readiness, PTaaS becomes a very sound financial investment.
Are you preparing for the Cyber Resilience Act? The Regulus software platform helps manufacturers and IoT vendors build a clear, actionable roadmap for CRA compliance. Unify your assessments, generate tailored requirements, and create audit-ready documentation to confidently place your products on the EU market. Learn more about how Regulus can simplify your CRA journey.