The Cyber Resilience Act (CRA) introduces stringent vulnerability handling obligations for all Products with Digital Elements (PDEs). Under Annex I Section 2, manufacturers must implement continuous processes for identifying, assessing, mitigating and reporting vulnerabilities throughout the entire lifecycle of their product.
This guide provides a detailed technical interpretation of every vulnerability handling requirement under the CRA, including reporting timelines, remediation expectations and documentation duties under Annex VII. If your product includes software, firmware or connectivity, these obligations apply to you.
1. What Vulnerability Handling Means Under the CRA
In the context of the Cyber Resilience Act, vulnerability handling refers to a structured, documented and continuous set of activities that ensure a product remains secure throughout its supported lifetime. These activities must include:
- Continuous vulnerability identification (internal + external sources)
- Assessment and prioritization based on risk and exploitability
- Mitigation and remediation within a reasonable timeframe
- Secure deployment of patches and updates
- Communication of vulnerabilities to users when necessary
- Mandatory reporting of actively exploited vulnerabilities
- Record-keeping under Annex VII
This is more than a “best practice”: it is a legal obligation that applies to all manufacturers under the CRA.
2. Legal Basis: Where Vulnerability Handling Appears in the CRA
The CRA integrates vulnerability handling across several sections:
2.1 Annex I – Essential Cybersecurity Requirements
Section 2 mandates:
- Processes for handling vulnerabilities
- Mechanisms for secure update delivery
- Protection against exploitation
- Communication obligations toward users
2.2 Articles 15 & 16 – Reporting Obligations
Manufacturers must report:
- Actively exploited vulnerabilities
- Significant cybersecurity incidents
Reports must follow strict timelines.
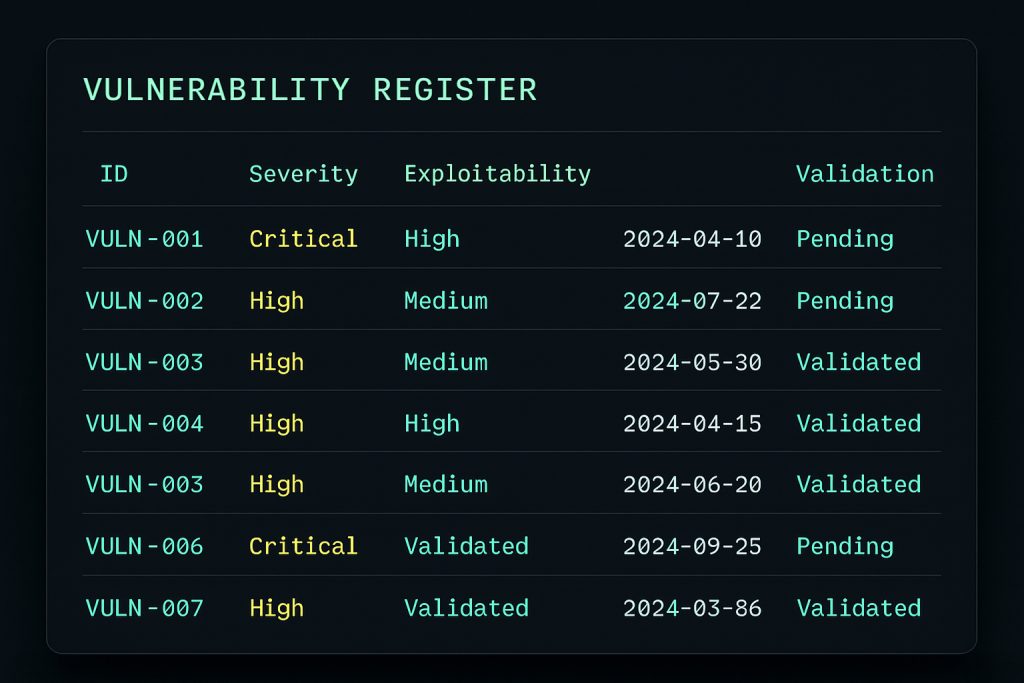
2.3 Annex VII – Post-Market Monitoring Documentation
Annex VII requires manufacturers to maintain:
- A vulnerability register
- Remediation evidence
- Incident reports
- Update history and validation logs
This documentation must be provided to authorities upon request.
3. CRA Vulnerability Handling Requirements (Annex I Section 2)
Below is a breakdown of each obligation in Annex I Section 2.
3.1 Continuous Vulnerability Identification
Manufacturers must continuously monitor:
- Internal testing and QA findings
- User-reported vulnerabilities
- Threat intelligence feeds
- Open-source vulnerability disclosures (for SBOM components)
- Supplier and third-party advisories
This implies the need for a formal intake process and a designated security contact point.
3.2 Assessment and Prioritization
Every identified vulnerability must be evaluated based on:
- Severity (CVSS or equivalent)
- Exploitability (public exploit, active exploitation)
- Impact (confidentiality, integrity, availability)
- Exposure (network vs local)
The CRA does not mandate CVSS specifically, but requires a structured and repeatable assessment methodology.
3.3 Remediation and Mitigation
Manufacturers must:
- Address vulnerabilities within a “reasonable timeframe”
- Apply temporary mitigations when necessary
- Document remediation decisions
Critical vulnerabilities, or those with active exploitation, require accelerated handling.
3.4 Deployment of Security Updates
Under CRA, updates must be:
- Delivered securely (signed, authenticated)
- Installed reliably
- Validated to avoid introducing new vulnerabilities
Manufacturers must also maintain a version history and a record of validation.
3.5 User Notification Requirements
In certain scenarios, manufacturers must notify users:
- When no patch is available for a known high-risk vulnerability
- When user action is required to mitigate impact
- When security updates include important fixes
4. Reporting Obligations: Vulnerabilities & Incidents
The CRA requires manufacturers to report:
4.1 Actively Exploited Vulnerabilities
If a vulnerability is being exploited in the wild, the manufacturer must notify:
- ENISA
- Relevant CSIRTs
Reports must be submitted without undue delay (interpreted as 24 hours in most regulatory guidance).
4.2 Significant Cybersecurity Incidents
Manufacturers must report:
- Exploitation causing substantial service disruption
- Widespread compromise of devices
- Incidents affecting critical infrastructure
5. Post-Market Monitoring Obligations (Annex VII)
Annex VII requires ongoing documentation of:
- A vulnerability register
- Assessment and prioritization records
- Mitigation steps taken
- Update verification logs
- Incident reports and timelines
Manufacturers must keep documentation for the entire support period.
6. Vulnerability Handling Workflow (Recommended)
- Receive vulnerability report
- Validate and acknowledge
- Assess severity and risk
- Define mitigation or remediation plan
- Develop and test the patch
- Deploy securely to devices/users
- Document all actions
- Report exploited vulnerabilities
This workflow ensures full alignment with Annex I and Annex VII.
7. Relationship with SBOM and Supply Chain Security
Vulnerabilities in third-party libraries and open-source components (SBOM items) are fully the responsibility of the manufacturer. You must:
- Monitor SBOM components for new CVEs
- Update libraries when fixes become available
- Document remediation
Neglecting SBOM monitoring is a direct violation of CRA obligations.
8. Common Compliance Mistakes to Avoid
- No formal intake process for vulnerability reports
- Missing or incomplete vulnerability register
- No evidence of update validation
- Failure to monitor SBOM components
- Not documenting mitigations
- No post-market monitoring plan
- Not reporting exploited vulnerabilities
9. How Regulus Helps
Regulus automates vulnerability handling compliance with:
- Centralized vulnerability register
- Automatic SBOM monitoring
- Annex I & Annex VII requirements mapping
- Evidence tracking for security updates
- Conformity risk scoring
Try the CRA Applicability Checker to determine requirements for your product.
Conclusion
Vulnerability handling is one of the most operationally complex aspects of CRA compliance. Manufacturers must adopt continuous monitoring, structured remediation processes, secure update mechanisms and strong documentation practices before the 2027 deadline.
For templates and workflows, explore: Cyber Resilience Act Resources