A supply chain attack is a bit like a Trojan horse, but for the modern digital world. Instead of launching a frontal assault on a well-defended target, attackers get clever. They find a crack in the armour of a trusted third-party supplier, vendor, or software component and slip in unnoticed. For example, instead of trying to hack a major bank directly, an attacker might compromise the smaller, less-secure software company that provides the bank’s customer chat feature.
This indirect approach completely changes the game. By targeting the less-secure elements in a product’s ecosystem—like software libraries, firmware updates, or even hardware chips—attackers can turn a trusted relationship into their primary weapon. It’s a method that massively expands the attack surface, making it one of the most significant threats to connected products today.
Understanding the Supply Chain Attack
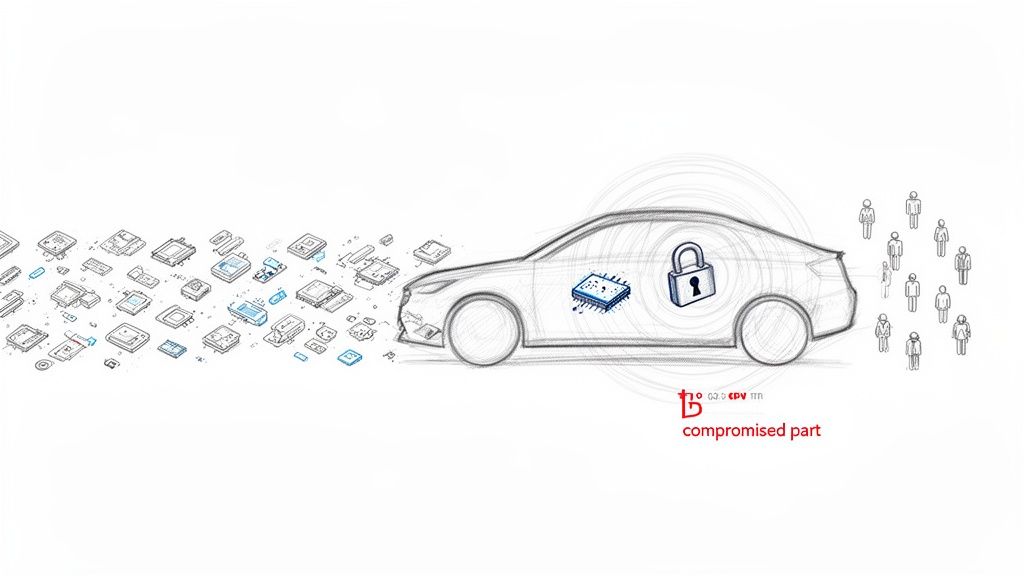
Let’s use a real-world analogy. Picture a state-of-the-art factory building a new electric vehicle. The assembly line sources thousands of parts from dozens of suppliers, including a critical navigation chip from a reputable, long-term partner. You trust that chip completely and build it into every single car.
But what if that chip was secretly backdoored at the supplier’s factory, long before it ever reached your production line?
That’s the essence of a digital supply chain attack. Attackers bypass your fortified corporate network and instead compromise a weaker link in your interconnected ecosystem. They might target a third-party software library, a managed service provider, or a physical hardware component, using it as a beachhead to breach your defences from the inside.
The Ripple Effect of a Single Breach
The true danger of these attacks lies in the devastating ripple effect. A single compromised component can cascade through an entire network of partners and customers, often silently. This makes the modern development lifecycle, which leans heavily on third-party code and services, a prime target.
To get a better sense of how this works in practice, here are a few common attack vectors:
- Compromised Software Updates: Attackers inject malicious code into a legitimate software update. When customers install the trusted update from a known vendor, they unknowingly install the malware alongside it. A classic example is the SolarWinds attack, where malicious code was hidden inside an official software patch.
- Infected Open-Source Libraries: A popular open-source library used by thousands of developers is tainted with malicious code. The threat spreads to every application that depends on that library, creating a massive, distributed vulnerability. The log4j vulnerability (Log4Shell) demonstrated this perfectly, affecting millions of applications that used the popular logging library.
- Hardware Tampering: Physical components, like microchips or sensors, are intercepted and altered during manufacturing or shipping. These embedded backdoors are notoriously difficult, if not impossible, to detect with standard quality checks. For instance, counterfeit network switches with hidden backdoors have been found in government and military supply chains.
To help break this down, the table below summarises the key elements that define this type of threat.
| Key Characteristics of a Supply Chain Attack |
| :— | :— |
| Characteristic | Description |
| Indirect Vector | The attack originates from a trusted third party, not a direct assault on the final target. |
| Exploitation of Trust | The attack leverages the trust between a business and its suppliers, partners, or vendors. |
| Broad Impact | A single breach can compromise numerous downstream targets simultaneously, creating a one-to-many effect. |
| Stealthy Nature | Malicious code is often hidden within legitimate software or hardware, making it difficult to detect. |
Ultimately, understanding these characteristics is the first step toward building a more resilient security posture.
A supply chain attack fundamentally flips the traditional security model on its head. It forces you to assume that threats can originate from within your trusted network, not just from external attackers. This requires a major shift from perimeter-based defence to a model of constant verification and deep visibility.
Why This Matters for Product Security
For manufacturers of connected products, this threat is particularly sharp. Every single third-party component—from a tiny sensor to a complex software development kit (SDK)—represents a potential entry point for an attack. Given how interconnected these products are, one vulnerability can have far-reaching consequences, compromising not just a single device but an entire fleet. A practical example would be a compromised Bluetooth chip used in a popular brand of smart locks, potentially allowing attackers to unlock thousands of homes.
Gaining visibility into the specific vulnerabilities within your product’s supply chain is the first step toward building a resilient defence. You can learn more about how to secure the different parts of your product by exploring various supply chain software solutions. In today’s landscape, securing your supply chain is no longer just an IT problem; it’s a critical pillar of product safety and business continuity.
Common Attack Vectors with Real-World Examples
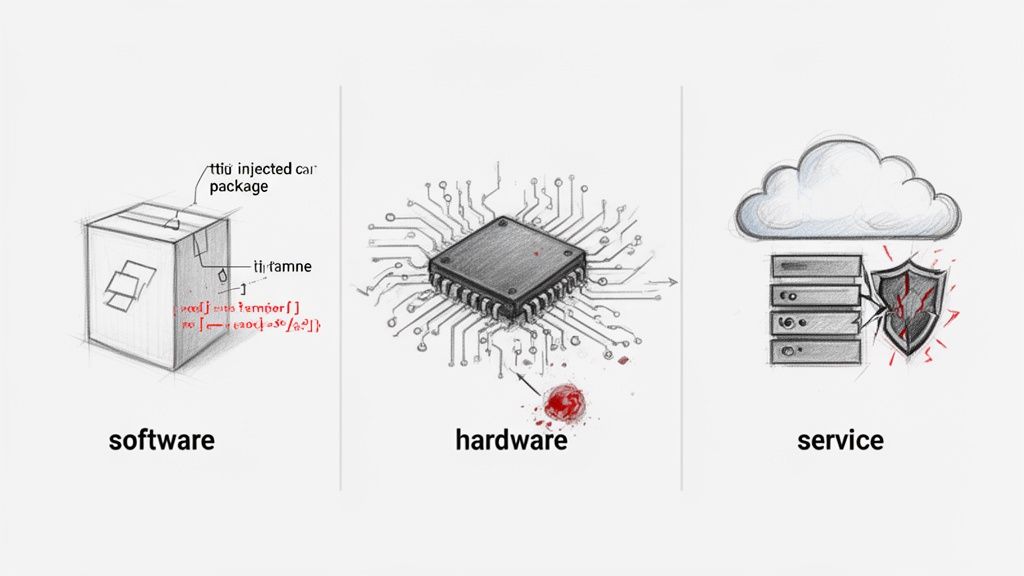
To build a solid defence, you first need to understand how attackers get in. A supply chain attack isn’t a single event; it’s a campaign that exploits trust at different stages of a product’s life. These attacks generally fall into three buckets: software, hardware, and service-based vectors, each posing unique challenges for security teams.
Software-based attacks are by far the most common, often targeting the building blocks of modern applications—open-source libraries and third-party code. Developers lean on these components to build faster, but that reliance creates a huge, interconnected web of dependencies that attackers love to exploit.
Software and Open-Source Compromises
Picture this: an attacker slips a few malicious lines of code into a popular open-source library used by thousands of applications. That’s exactly what happened in the s1ngularity attack, where poisoned versions of the widely used Nx build system package were uploaded to the npm registry. A simple post-install script was designed to steal developer assets like GitHub tokens and SSH keys.
This single point of failure meant any developer or automated build system that downloaded the compromised package was, in effect, installing malware. The attack shines a light on a critical vulnerability: the implicit trust developers place in the packages they use. What seems like a routine update can become a gateway for a massive breach. For a better sense of how these dependencies fit together, check out our guide on the Maven dependency tree.
This vector is so dangerous because of its scale. One compromised library can infect hundreds or thousands of downstream projects. We saw this in another large-scale npm supply chain attack where the malware was designed to propagate itself by automatically infecting other packages maintained by its victims, creating a domino effect that was incredibly hard to contain.
By poisoning the well of open-source software, attackers achieve massive leverage. They don’t need to breach thousands of companies individually; they just need to compromise one widely used component to get the same result.
The infamous SolarWinds attack stands as a landmark example of a software supply chain breach with devastating reach. Attackers got into the build environment of SolarWinds, a major IT management software provider, and injected malicious code directly into their Orion Platform software.
Here’s a quick rundown of how it happened:
- Initial Breach: The attackers gained access to SolarWinds’ systems and subtly modified the source code for the Orion software.
- Malicious Update: This tainted code was then bundled into official, digitally signed software updates.
- Widespread Distribution: Over 18,000 SolarWinds customers, including government agencies and Fortune 500 companies, downloaded and installed the trojanised update, thinking it was a legitimate patch.
- Backdoor Access: The malware, dubbed “Sunburst,” lay dormant for a while before activating, creating a backdoor that let the attackers infiltrate customer networks.
Hardware and Firmware Tampering
While software attacks grab the headlines, hardware-based threats are often more subtle and much harder to detect. A hardware supply chain attack involves physically tampering with components like microchips, sensors, or other integrated circuits during manufacturing or shipping.
For example, an attacker could intercept a shipment of microcontrollers and embed a hidden backdoor into the chip’s circuitry. This compromised component would pass all standard functional tests and look completely normal. Once it’s integrated into a final product—like a smart home device or an industrial control system—the backdoor could give an attacker privileged access, a way to bypass security controls, or a channel to siphon off data. The “VGA-gate” incident, where modified VGA cables were used to exfiltrate data from secure facilities, is a prime example of hardware tampering.
Compromised Third-Party Services
Finally, service-based attacks target the third-party providers businesses rely on for critical functions. This includes Managed Service Providers (MSPs), cloud hosting providers, and Software-as-a-Service (SaaS) platforms. By breaching a single service provider, attackers can gain access to the data and systems of all their clients.
A recent breach at the single sign-on provider Okta exposed 134 business clients across Europe, wiping $2 billion from its market value almost overnight. This incident shows the cascading risks in our interconnected world, as a single compromised vendor can create a ripple effect that hits hundreds of manufacturers. Similarly, the 2019 breach of a patient data management vendor exposed the sensitive information of over 20 million customers from multiple lab testing companies, all because one service provider was compromised.
Each of these vectors drives home the same fundamental truth: your security is only as strong as the weakest link in your supply chain.
The True Cost of a Supply Chain Breach
When a supply chain attack lands, it’s never just an IT ticket. It’s a full-blown business continuity crisis, with shockwaves that rattle every corner of the organisation. The most immediate pain point is usually operational disruption—something that can bring a manufacturer to its knees.
Picture an assembly line for a connected device grinding to a halt. Suddenly, production schedules are shredded, delivery deadlines are missed, and the threat of contractual penalties becomes very real. This isn’t just a worst-case scenario; it’s what happened when the NotPetya malware attack spread through the shipping giant Maersk’s software supplier, crippling their global logistics operations for weeks and costing them an estimated $300 million.
Financial Haemorrhaging and Recovery
The financial fallout from a breach is staggering, and it comes from all directions. The immediate hit is the cost of incident response—bringing in forensic experts, containing the breach, and kicking the attackers out of your systems. That alone can run into the millions.
But that’s just the start. The full bill includes:
- Lost Revenue: Every hour of downtime is an hour you’re not making or selling anything. For a manufacturer, that hits the bottom line instantly.
- Recovery and Remediation Costs: Rebuilding compromised systems, replacing infected hardware, and hardening your supply chain for the future requires a huge investment in both tech and people.
- Regulatory Fines: In places like the EU, failing to meet cybersecurity standards comes with a hefty price tag. Frameworks like the Cyber Resilience Act (CRA) are specifically designed to hold manufacturers accountable for the security of their products, supply chain and all.
A single supply chain attack can cause colossal financial damage. Take the devastating ransomware attack on a luxury carmaker. It didn’t just stop production; it disrupted over 5,000 organisations in its supply and distribution network, with estimated losses hitting £2.1 billion. The ripple effect triggered a 30% drop in UK car production for a month and even contributed to a surprise dip in the national GDP. You can read the full breakdown of this supply chain catastrophe in the Allianz Risk Barometer.
The Long Shadow of Reputational Damage
Perhaps the most lasting cost of all is the erosion of trust. A public breach obliterates a company’s reputation, leaving customers and partners wondering if its products can ever be trusted again. Rebuilding that confidence is incredibly difficult and can haunt a business for years. For instance, after the SolarWinds breach, many government agencies and corporations began re-evaluating their trust in all third-party software vendors, causing a chilling effect across the entire industry.
A brand’s reputation is built over years but can be shattered by a single supply chain incident. Customers who lose faith in a product’s security will quickly turn to competitors, leading to sustained market share loss that can persist long after the technical issues are resolved.
This damage spreads through the entire ecosystem. When a manufacturer’s product is compromised, it hurts distributors, importers, and end-users, creating a domino effect of mistrust. For companies selling connected products—where security is a core part of the deal—the reputational harm can be fatal.
Navigating the Regulatory Minefield
The consequences of a supply chain attack are no longer just commercial—they’re increasingly legal and regulatory. Authorities across the globe, especially in the European Union, are rolling out strict rules to enforce cybersecurity standards.
The EU’s Cyber Resilience Act (CRA) is a perfect example. This regulation puts the responsibility squarely on manufacturers to secure their products for their entire lifecycle. A supply chain breach that introduces a vulnerability could be seen as a direct failure to meet these obligations, leading to:
- Market Access Restrictions: Non-compliant products can be blocked from the EU market, cutting off access to millions of customers overnight.
- Forced Product Recalls: Regulators have the power to order recalls of insecure products—a logistical and financial nightmare.
- Substantial Fines: The CRA comes with serious financial penalties for non-compliance, adding yet another layer of risk to the equation.
Ultimately, the true cost of a supply chain breach is a toxic mix of operational paralysis, crippling financial losses, permanent reputational harm, and severe regulatory punishment. It’s a fundamental business risk that belongs in the boardroom, not just the IT department.
Building a Resilient Defence Strategy
Knowing the problem is one thing; solving it is another. A truly resilient security posture isn’t built on a single tool or a silver-bullet solution. It’s a multi-layered strategy grounded in three core pillars: proactive prevention, vigilant detection, and rapid response.
A cornerstone of this entire approach is implementing robust Third-Party Risk Management (TPRM). This is about doing your homework before you integrate a new supplier, partner, or piece of software into your ecosystem. It means asking the tough questions upfront to make sure their security standards are as high as your own, creating a much stronger, more defensible starting point.
Proactive Prevention Measures
The best way to win a fight is to avoid it in the first place. Proactive prevention is all about hardening your development lifecycle and supply chain to make it a much tougher target for attackers. This starts with rigorous supplier vetting—moving beyond simple questionnaires to conduct deep-dive security assessments of your partners. For instance, you could require potential software vendors to provide their own SOC 2 reports or evidence of regular penetration testing.
Another critical piece is embedding secure coding practices directly into your development workflow. This isn’t just about tools; it’s about training your developers to write code that is inherently resistant to common vulnerabilities. Use static analysis tools to catch potential issues before they ever make it into a final build.
Of course, you can’t secure what you can’t see. This is where a Software Bill of Materials (SBOM) becomes absolutely essential.
- What is an SBOM? Think of it as a detailed ingredients list for your software. It catalogues every single component—open-source libraries, third-party APIs, and all other dependencies.
- Why is it crucial? An SBOM gives you the visibility needed to identify outdated or vulnerable components almost instantly. When a new vulnerability is discovered, you can check your SBOM to see if your product is affected, rather than scrambling to manually inspect your entire codebase.
Take the s1ngularity attack, where malicious versions of the popular Nx build system were published. Organisations with a clear SBOM could immediately tell if they were using the compromised packages. Those without that visibility were left guessing, which dramatically slowed their response time.
Early and Accurate Detection
Even with the best preventative measures, you have to operate on the assumption that a breach is not a matter of if, but when. The detection pillar is all about spotting anomalies and potential intrusions as early as possible to minimise the damage. This requires a fundamental shift from periodic spot-checks to a model of continuous monitoring.
One of the most powerful detection techniques is implementing integrity checks for your software and hardware components. This involves creating a known-good baseline—a “golden image”—of your software or firmware and then constantly checking against it. Any unauthorised change or deviation from this baseline should trigger an immediate alert, signalling a potential compromise. For example, a car’s Engine Control Unit (ECU) software can be cryptographically signed, and the vehicle can refuse to start if the signature doesn’t match the manufacturer’s original.
A mature detection strategy operates on the principle of “trust but verify.” It assumes that even trusted components could be compromised and therefore subjects everything to continuous scrutiny. This vigilance is the key to catching a supply-chain attack before it escalates into a full-blown crisis.
The costs of a supply chain breach can quickly spiral out of control, affecting everything from production to your brand’s reputation.
As the diagram shows, the impact extends far beyond the initial technical glitch. It hits core business operations and, just as importantly, the trust you’ve built with your customers.
Battle-Tested Incident Response
When an attack is detected, your response needs to be swift, coordinated, and decisive. A well-documented and regularly rehearsed incident response plan isn’t a luxury; it’s an absolute necessity. This plan must clearly define roles, responsibilities, and communication channels for when a crisis hits. For example, your plan should specify who has the authority to take a production system offline and how customers will be notified of a potential data breach.
Key elements of a strong incident response plan include:
- Containment: The immediate priority is to isolate the affected systems. This stops the attack from spreading further across your network or, worse, to your customers.
- Eradication: Once contained, the next step is to hunt down and remove the root cause of the breach, whether it’s a malicious package, a compromised account, or a backdoored component.
- Recovery: This involves restoring affected systems from clean backups and thoroughly verifying that they are secure before bringing them back online.
- Post-Mortem Analysis: After the dust settles, conduct a thorough analysis to understand exactly what went wrong. Use those lessons to strengthen your defences and prevent it from happening again.
The following table maps these defensive strategies directly to the requirements of the EU’s Cyber Resilience Act, showing how good security practice is now becoming a legal mandate.
Supply Chain Defense Mapped to CRA Requirements
| Defense Strategy | Key Actions | Relevant CRA Obligation |
|---|---|---|
| Proactive Prevention | Rigorous supplier vetting, secure coding practices, maintaining a detailed SBOM. | Annex I, Section 2 requires secure-by-design principles and supply chain transparency. |
| Early Detection | Continuous monitoring of components, integrity checks against golden images. | Annex I, Section 2 mandates mechanisms to detect and log security-relevant events. |
| Incident Response | Documented response plans, vulnerability handling procedures, clear reporting channels. | Annex I, Section 2 requires documented vulnerability handling and mandatory reporting. |
This alignment demonstrates that building a robust defence isn’t just about protecting your business—it’s also about meeting your compliance obligations head-on.
These best practices are rapidly becoming legal mandates. Emerging regulations like the EU’s Cyber Resilience Act (CRA) explicitly require manufacturers to have documented processes for vulnerability handling and incident reporting. Your incident response plan is now a critical piece of compliance evidence. For those looking to deepen their technical capabilities, a great starting point is learning more about tools like the OWASP Dependency-Check to automate vulnerability detection.
Achieving CRA Compliance with Confidence
Trying to get your arms around complex regulations like the EU Cyber Resilience Act (CRA) can feel like a losing battle, especially with the constant threat of a supply chain attack. Many teams find themselves buried in spreadsheets and big consulting bills just to figure out where they stand. But there’s a much smarter way to turn this challenge into a clear, manageable process.
Modern compliance platforms are built to solve these exact problems. They start with the most basic, yet critical, questions: does the CRA even apply to your product? And if it does, is it a Default or Critical product? Getting this right is the absolute first step toward understanding what the law actually expects from you. For example, a smart toaster would likely be a Default product, whereas a network router for critical infrastructure would be classified differently, each with distinct obligations.
From Assessment to Actionable Roadmaps
Once you know the CRA applies, the real work starts. A dedicated platform can automatically map your product’s classification and your role in the supply chain to a precise set of obligations. This takes the guesswork out of compliance, giving you a tailored matrix of requirements covering everything from security design to post-market surveillance.
Instead of reinventing the wheel, you get access to ready-made templates for all the essential paperwork. This helps you structure technical files and gather evidence in a way that aligns perfectly with the CRA’s specific annexes. For any organisation serious about security, holding a certification like SOC 2 Type II certification shows a real commitment, and solid documentation is a huge part of proving it.
This dashboard from Regulus shows how a compliance platform provides a clear, step-by-step view of CRA requirements.
This kind of visual roadmap makes complicated legal text easy to understand, turning it into an actionable checklist that your engineering and compliance teams can actually use.
Integrating Vulnerability Management
A huge piece of the CRA puzzle is having a solid vulnerability management process. The regulation is very clear: you need established workflows for finding, reporting, and disclosing security flaws in your products. A good compliance platform builds these requirements right into your day-to-day work, guiding you on how to structure your processes to meet the standard.
This is especially important for defending against a supply chain attack. It ensures you have a documented, rehearsed plan for handling vulnerabilities that come from third-party components—a core requirement for any product sold in the EU. A practical example would be having a pre-defined process to notify all customers within 24 hours if a critical vulnerability is found in a third-party library used by your product.
A compliance platform acts as a single source of truth, translating abstract regulatory language into concrete engineering tasks. It moves teams away from reactive compliance efforts and toward a proactive security posture built for the long haul.
Ultimately, this approach gives teams clarity and brings down costs. It turns your assessment into a step-by-step plan for the 2025–2027 implementation period. This lets you prepare your products for the European market with confidence, knowing your processes are exactly what regulators expect. To get a head start, you can explore a detailed Cyber Resilience Act compliance roadmap to see the key milestones.
By swapping manual grunt work for a guided, automated system, you can achieve compliance with confidence and get back to what you do best: building great, secure products.
Why You Can’t Afford to Ignore Supply Chain Security
For a long time, supply chain security felt like someone else’s problem. Not anymore. Today, ignoring it is a direct threat to your business’s survival. A single compromised component—whether it’s a tiny piece of hardware or a third-party software library—can set off a catastrophic domino effect.
We’re talking about real, tangible consequences: production lines grinding to a halt, staggering financial losses, and the kind of reputational damage that takes years to repair. Customer trust, once lost, is incredibly hard to win back.
The threat isn’t just theoretical; it’s a clear and present danger. The data shows a dramatic uptick in these kinds of attacks, elevating them from a niche IT concern to a top-tier business risk. For any manufacturer with ambitions in the European market, the urgency is dialled up even further by regulations like the Cyber Resilience Act (CRA), which turns best practices into legally binding obligations.
The Risk Is Real—and It’s Growing
Recent statistics paint a sobering picture. A massive 76% of European shippers reported supply chain disruptions, with a quarter of them hit more than 20 separate times. And what’s driving this? Cyber risks are now cited by 16% as the top threat, a huge jump from just 5% the previous year.
When an attack does hit, the financial bleed is immediate. With the average disruption costing a company $1.5 million per day, the stakes couldn’t be higher. You can dig deeper into these trends in recent supply chain risk surveys.
Proactive supply chain security and regulatory readiness aren’t just about ticking compliance boxes. They’ve become fundamental to business continuity and market access in a world where everything is connected. The time for waiting and reacting is over.
Ultimately, this all points to one conclusion: it’s time for a decisive shift in mindset. We have to move away from a reactive, incident-driven posture and build a proactive culture of resilience. That means embedding security into every single stage of the product lifecycle—from vetting suppliers with scrutiny to managing vulnerabilities with transparency.
Now is the moment to take a hard look at your defences, get a firm grip on your obligations, and take meaningful action to lock down your supply chain.
Frequently Asked Questions
Digging into the details of supply chain security always brings up good questions. Here are a few of the most common ones we hear from product security teams and manufacturers trying to get ahead of modern supply chain attacks.
What Is the First Step to Secure My Product Supply Chain?
The first and most critical step is visibility. You simply can’t secure what you can’t see. That means your immediate priority should be creating a comprehensive Software Bill of Materials (SBOM).
Think of an SBOM as a detailed ingredients list for your software. It catalogues every single third-party library, open-source component, and dependency your product is built on. This inventory gives you the foundational visibility needed to track, manage, and ultimately fix vulnerabilities across your entire supply chain. Without an SBOM, responding to a new threat is slow, speculative work. With one, it becomes a fast, targeted process. For example, when the critical Log4Shell vulnerability was announced, companies with an up-to-date SBOM could instantly identify every affected application, while others spent days or weeks searching their codebases.
How Does the EU Cyber Resilience Act Address Supply Chain Attacks?
The EU’s Cyber Resilience Act (CRA) takes supply chain risk head-on by turning best practices into hard legal obligations for manufacturers. Security is no longer just a good idea; it’s a condition for market access.
Key provisions that directly target supply chain weaknesses include:
- Vulnerability Handling: Manufacturers are legally required to have a documented process for finding and fixing vulnerabilities, including those that come from third-party components.
- Security Updates: You have a legal duty to provide timely security updates for either your product’s expected lifetime or a period of five years, whichever is longer.
- Transparency: The CRA mandates that manufacturers provide an SBOM, making their software composition transparent to customers and regulators.
These rules force organisations to take ownership of the security of their entire supply chain, not just the code they write themselves.
Are Small Businesses a Target for Supply Chain Attacks?
Yes, absolutely. It’s a dangerous myth that attackers only go after big corporations. The reality is that attackers often see smaller, less-defended suppliers as the easiest way to get to a much bigger prize. A real-world case involved hackers breaching an HVAC vendor to gain access to the network of a major retail corporation, demonstrating how a small, seemingly low-risk supplier became the entry point for a massive data breach.
Attackers frequently compromise smaller businesses to use them as a Trojan horse. By breaching a trusted supplier, they can piggyback on that established relationship to infiltrate the more heavily defended networks of their larger corporate customers. This makes every business, regardless of size, a potential target and a critical link in the security chain.
This tactic means that if your business is part of any larger supply chain, you are an attractive target. Bolstering your own security isn’t just about protecting your assets—it’s about keeping the trust of your partners and customers.
Navigating CRA compliance and securing your products against a supply chain attack requires a clear, structured approach. Regulus provides the software platform to assess applicability, map requirements, and build a confident path to market. Learn more about how Regulus can help.