At its core, the CRA single reporting platform is a centralised EU portal, managed by ENISA, where manufacturers must report actively exploited vulnerabilities and severe security incidents. Think of it as a single, unified “911 dispatch” for cybersecurity, ending the chaos of notifying multiple authorities across different EU member states.
What is This New Cybersecurity Hub?
The EU’s Cyber Resilience Act (CRA) is overhauling how manufacturers of products with digital elements must deal with security problems. The centrepiece of this shift is a mandatory reporting system, built to orchestrate a rapid, coordinated response to emerging cyber threats across the entire European market.
This isn’t just another layer of administrative red tape. It’s a fundamental move toward proactive and transparent security management. Before, if a vulnerability was discovered in a smart TV sold across Germany, France, and Spain, the manufacturer would have to wrestle with different reporting rules for each country’s national authority. The single reporting platform does away with that complexity.
What Is the Platform’s Purpose?
The main objective is to centralise information and radically speed up the response to security threats. When a manufacturer submits a report, the platform ensures the details are immediately shared with the relevant national Computer Security Incident Response Teams (CSIRTs) and other key bodies. This coordinated approach helps protect consumers and businesses EU-wide, stopping isolated incidents before they can spiral into widespread crises.
The core idea is simple: one product, one vulnerability report, one central point of contact. This setup ensures critical security information doesn’t get bogged down in bureaucracy, enabling a swift and unified defence against cyber attacks.
The New Reporting Obligations At a Glance
To make these new duties clearer, here’s a quick summary of what the CRA’s single reporting platform entails.
| Requirement | Details | Governing Body/Article |
|---|---|---|
| Mandatory Reporting | Manufacturers must report actively exploited vulnerabilities. | ENISA / Article 14 |
| Initial Notification | An early warning is due within 24 hours of awareness. | CSIRT Network / Article 14(1) |
| Incident Notification | A more detailed report is required within 72 hours. | CSIRT Network / Article 14(2) |
| Final Report | A comprehensive report must be submitted within 14 days. | CSIRT Network / Article 14(3) |
This table highlights the strict timelines and the central role of ENISA and the CSIRT Network in managing the flow of information. It’s a system designed for speed and clarity.
Who Is Affected and What Are the Deadlines?
This new obligation impacts any manufacturer placing products with digital elements on the EU market. The scope is broad, covering everything from laptops and smartphones to industrial control systems and IoT devices. For companies managing a large portfolio, scaling up to meet these demands means turning to proven solutions for banking and financial document automation to handle the volume and complexity of evidence generation.
The clock is ticking. The CRA’s Single Reporting Platform (SRP) goes live for mandatory reporting on September 11, 2026. This is the hard deadline when manufacturers must start notifying CSIRTs about actively exploited vulnerabilities. The reporting timelines are aggressive, with initial warnings required within just 24 hours.
To get a complete picture of these crucial deadlines and what they mean for your team, you can dive deeper into CRA reporting obligations in our dedicated article.
The diagram from ENISA below visualises how this central portal will function as the nerve centre connecting all stakeholders.
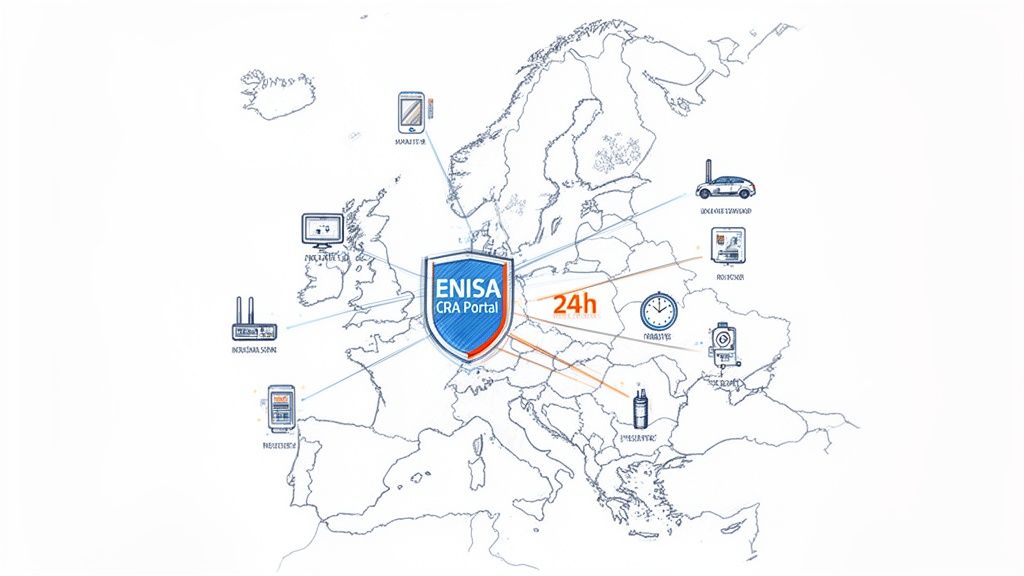
As you can see, the ENISA portal sits at the heart of the ecosystem, serving as the communication hub between manufacturers, national authorities, and the wider market to guarantee a seamless flow of information.
Understanding Your New Compliance Obligations
The Cyber Resilience Act isn’t just about a new reporting portal. It fundamentally changes the game by establishing a continuous standard of care for your products. This shifts your responsibilities from a reactive, break-fix model to a proactive, lifecycle-focused one. Your job doesn’t end when the product ships; it extends for years.
To get a handle on the CRA, it helps to have a good understanding of contract compliance and how it already protects your business. The core principles of following defined rules and responsibilities are exactly what you’ll need to navigate the CRA’s new legal landscape. These duties demand a clear, structured approach to keep your products secure and meet regulatory demands head-on.
Mastering Post-Market Surveillance
Under the CRA, post-market surveillance is no longer a passive waiting game. It forces manufacturers to actively and continuously monitor their products for new threats and vulnerabilities long after they’ve hit the EU market.
Think of a company that makes smart thermostats. In the past, they might have waited for a security researcher or a customer to report a problem. That approach is no longer good enough.
Practical Example: The smart thermostat company must now have systems in place to:
- Proactively scan threat intelligence feeds for new exploits that could impact their device’s OS or third-party code.
- Regularly test their products against new attack methods seen in the wild, even if no incident has been reported for their specific device.
- Analyse telemetry from their devices to spot unusual patterns that could signal a coordinated attack is in progress.
This constant vigilance makes security an ongoing process, not a one-time check. It’s about protecting consumers from threats that pop up months or even years after a product is installed in their homes.
Demystifying Coordinated Vulnerability Disclosure
Coordinated Vulnerability Disclosure (CVD) is another core pillar of the new regulation. It mandates a formal process for handling vulnerability reports from third parties, like ethical hackers and security researchers. The goal is simple: fix security flaws before malicious actors can find and exploit them.
The CRA effectively formalises the “see something, say something” principle for cybersecurity. It requires you to build a clear, secure channel for bug reports and a transparent process for fixing them in partnership with the finder.
Let’s say a connected car company gets a report from a researcher who found a bug in the infotainment system. This bug could let an attacker pivot to the car’s internal network.
Practical Example: A compliant CVD process would look like this:
- Acknowledge: The company must acknowledge the report within a set timeframe, confirming they’re on it.
- Collaborate: They work with the researcher to grasp the vulnerability’s scope and impact, setting a realistic timeline for a fix.
- Remediate: The engineering team develops and validates a software patch to resolve the issue.
- Disclose: Once the patch is ready for an over-the-air (OTA) update, the company publicly discloses the vulnerability and the fix, often crediting the researcher.
This structured workflow prevents a chaotic free-for-all where vulnerabilities are disclosed irresponsibly, giving attackers a window of opportunity.
Defining the Product’s Expected Lifetime
One of the biggest—and most debated—requirements is managing security updates for your product’s “expected lifetime.” The CRA establishes a default support period of at least five years, unless the product is reasonably expected to be used for a shorter time.
This means you are legally on the hook to provide free and timely security updates for that entire period. For a high-end smart fridge manufacturer, the expected lifetime might be ten years or more, extending this obligation significantly. For a simple Bluetooth tracker, it might only be a couple of years.
Practical Example: A company sells a high-end robotic vacuum cleaner advertised with a 10-year lifespan. They are now obligated to provide security patches for its software for that full decade. In contrast, a maker of a children’s smart-toy with an expected play-life of two years can define a shorter, two-year security support period, as long as this is clearly stated to the consumer.
This rule forces you to think about long-term security maintenance from the get-go, right in the design phase. It ensures products don’t become insecure, abandoned liabilities just a year or two after being sold, which would create risks for the entire digital ecosystem.
Building Your CRA Compliance Toolkit
Relying on scattered spreadsheets and chaotic email chains to manage your new Cyber Resilience Act obligations simply won’t work. The CRA’s strict timelines and detailed documentation needs demand a purpose-built system. Whether you build an internal solution or invest in a dedicated CRA single reporting platform, your toolkit must be equipped with specific, non-negotiable features.
This isn’t about just buying software; it’s about building a robust operational engine. Your toolkit must act as the central nervous system for your entire product security programme, connecting vulnerability intake, triage, and supply chain management into a single, auditable workflow.
Secure and Simple Vulnerability Intake
The first essential component is a secure channel for vulnerability intake. The CRA requires you to make it easy for others to report potential vulnerabilities, which means ethical hackers, researchers, and customers need a clear, safe way to contact you. An ad-hoc “security@company.com” email address is neither sufficient nor secure enough.
A proper intake system provides a structured, public-facing portal where researchers can submit their findings. This process needs to be straightforward, ensuring you get the critical details you need for an assessment without creating friction that might discourage someone from reporting a flaw in the first place.
Practical Example: A manufacturer of smart lighting systems puts a vulnerability disclosure portal on their website. A security researcher finds a flaw that could let an attacker control the lights remotely. They use the portal’s encrypted form to submit a detailed report, including steps to reproduce the issue, which automatically creates a high-priority ticket in the manufacturer’s system.
Triage and Tracking Against the Clock
Once a vulnerability is reported, the clock starts ticking. You have a 24-hour deadline to notify authorities of any actively exploited vulnerabilities and a 72-hour window for a more detailed report. Speed and accuracy are everything. Your toolkit needs a powerful triage and tracking system to cope.
This system must allow your Product Security Incident Response Team (PSIRT) to quickly assess a report’s severity, validate its authenticity, and prioritise it against other issues. It also has to provide a clear, real-time view of where each vulnerability is in the remediation lifecycle, with automated alerts to make sure no deadlines are missed.
A common mistake is treating all vulnerability reports as equally urgent. An effective triage system allows you to immediately distinguish a critical, actively exploited flaw from a low-impact bug, focusing your resources where they matter most.
The process flow below shows how a CRA toolkit should handle incoming reports, from the initial intake through to mapping it against your products.
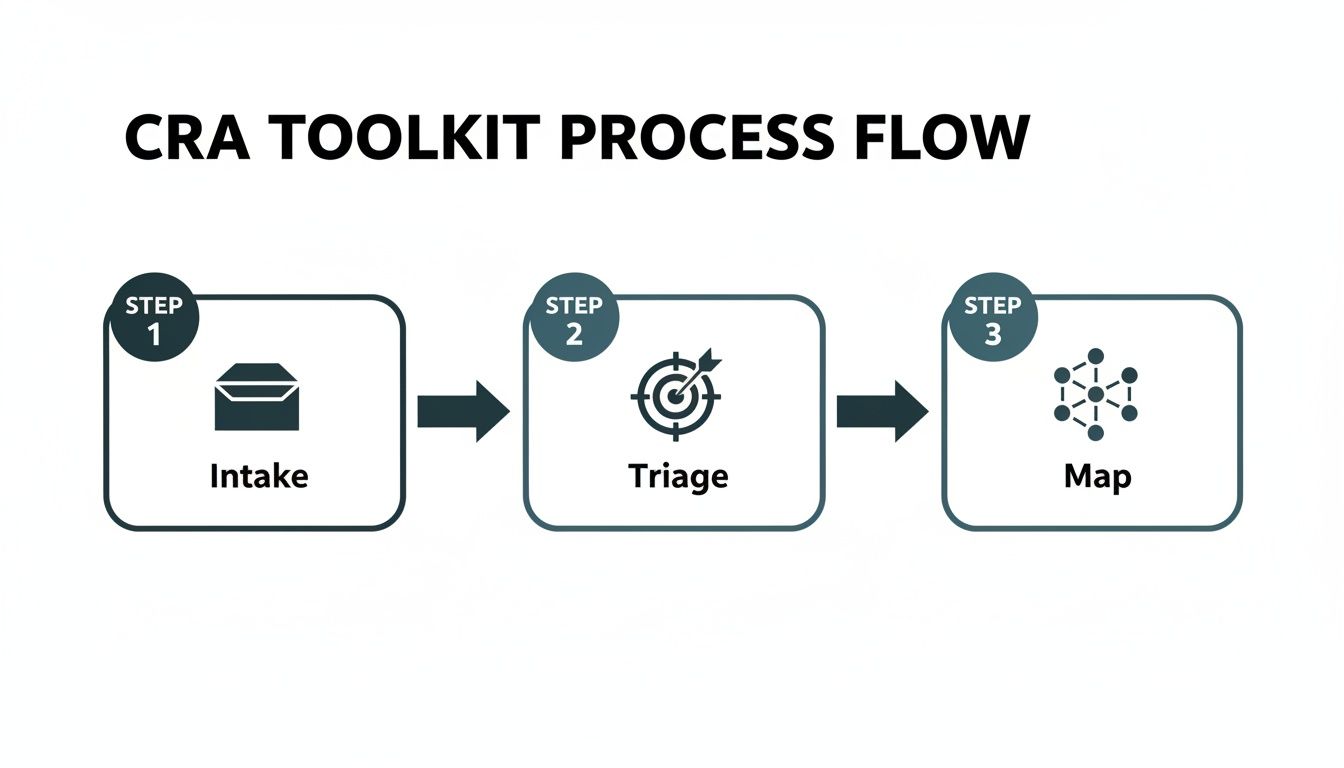
This shows how a structured process—Intake, Triage, and Map—is crucial for turning raw vulnerability data into actionable intelligence efficiently.
Supply Chain Mapping and Responsibility
Few modern digital products are built entirely in-house. Your smart device likely contains dozens of third-party software components, and under the CRA, a vulnerability in any one of them is your responsibility. This is why supply chain mapping is a critical function of your compliance toolkit.
When a vulnerability is reported for a component like Log4j or OpenSSL, you need to know instantly which of your products are affected. Your system must be able to connect the Software Bill of Materials (SBOM) for each product to your vulnerability database.
Practical Example: A company making connected home cameras gets an alert about a new vulnerability in a popular open-source video streaming library. Their CRA single reporting platform automatically scans the SBOMs of all their camera models. Within minutes, it identifies the three specific models that use the vulnerable library version, assigns tasks to the relevant engineering teams, and alerts the compliance manager to prepare for potential reporting.
Comparing Manual vs Platform-Based CRA Management
To manage these interconnected tasks effectively, teams must choose between traditional, manual methods and a modern, integrated platform. The table below outlines the key differences.
| Feature/Process | Manual Approach (Spreadsheets & Email) | Integrated Platform (e.g., Regulus) | Benefit of Platform |
|---|---|---|---|
| Vulnerability Intake | Ad-hoc email inbox; unstructured reports. | Public-facing portal with structured forms. | Consistent, complete data from day one. |
| Triage & Deadlines | Manual tracking; high risk of human error. | Automated timers, severity scoring, and alerts. | Prevents missed deadlines and ensures focus. |
| Supply Chain Mapping | Manual SBOM lookups; slow and error-prone. | Automated SBOM scanning and product mapping. | Instant visibility of affected products. |
| Evidence Generation | Manual, time-consuming report compilation. | On-demand, audit-ready evidence packs. | Drastically reduces audit preparation time. |
| Scalability | Breaks down as product portfolio or team grows. | Scales seamlessly with business growth. | Future-proofs your compliance operations. |
While a manual approach might seem feasible for a single product, it quickly becomes unmanageable. An integrated platform provides the structure, automation, and single source of truth needed for long-term, scalable CRA compliance.
Automated Evidence Generation for Audits
Finally, proving compliance is just as important as achieving it. Your toolkit must be capable of generating audit-ready evidence on demand. This includes records of every vulnerability report, triage decision, remediation action, and all communications with authorities.
Manually compiling this information for your technical files (as required by Annex II of the CRA) is an incredibly time-consuming and error-prone process. Automated evidence generation saves countless hours and ensures your documentation is always consistent, complete, and up-to-date. As your team grows, knowing how to manage your CRA compliance evidence pack becomes a key operational advantage. An integrated platform makes this seamless, creating a single source of truth for all your compliance activities.
How to Implement a CRA Governance Framework
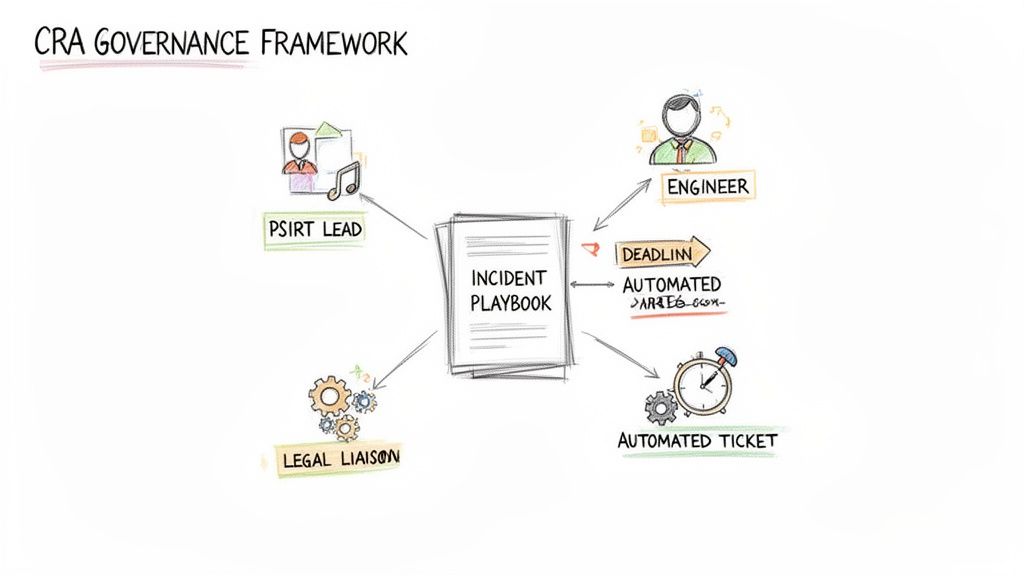
A powerful compliance platform is only as good as the people and processes that drive it. To make the Cyber Resilience Act’s requirements a part of your daily operations, you need a strong governance framework. Think of it as your organisational blueprint—it defines who does what, when, and how, especially when a security incident hits.
Without clear governance, even the best CRA single reporting platform won’t save you from chaos. This is your roadmap for weaving CRA compliance into your operational fabric, moving your teams from reactive scrambling to structured, confident action.
Defining Key Roles for CRA Readiness
Your first move is to get the right team on the field. CRA compliance isn’t just an IT or engineering problem; it’s a cross-functional responsibility that demands clear ownership. Standing up a dedicated Product Security Incident Response Team (PSIRT) is non-negotiable.
Your CRA governance structure should have these key roles clearly defined:
- PSIRT Lead: The ultimate owner of the incident response process. This person is the orchestrator, coordinating between teams and making the final call on severity assessments and reporting decisions.
- Technical Lead: A senior engineer or security architect who is responsible for validating the vulnerability, figuring out its technical impact, and guiding the development of any patch or mitigation.
- Legal Liaison: A representative from your legal or compliance team. They advise on regulatory obligations, communication strategies, and potential liability, making sure every action aligns with the CRA.
- Communications Manager: The person who drafts and sends out all external communications. This includes notifications to ENISA, customer advisories, and public disclosures.
This structure guarantees that every angle of an incident—from the technical nitty-gritty to the legal review—is handled by an expert. It cuts through the confusion and speeds up decision-making when the clock is ticking.
Creating Incident Response Playbooks
Once your team is in place, you need to arm them with clear, actionable incident response playbooks. These aren’t generic corporate documents; they are step-by-step guides built specifically for CRA scenarios and their tight timelines. A good playbook eliminates guesswork during a crisis.
Your playbook is your “in case of emergency, break glass” guide. It should be so straightforward that a team member can execute their role effectively even under immense pressure at 2:00 AM.
Let’s walk through what a playbook for handling a critical remote code execution (RCE) vulnerability might look like in practice.
Practical Example: A Sample RCE Playbook
- Initial Alert (Hour 0): A new, potentially critical vulnerability is submitted through your secure intake portal. The PSIRT Lead is automatically notified, and the 24-hour reporting clock officially starts.
- Triage and Validation (Hours 1-6): The Technical Lead gets to work validating the vulnerability. They confirm it is indeed an RCE, assess its severity using a framework like CVSS, and determine if it is being actively exploited.
- Go/No-Go for Reporting (Hour 7): The PSIRT Lead calls a quick huddle with the Technical Lead and Legal Liaison. Based on the evidence of active exploitation, they make the decision to notify ENISA.
- ENISA Early Warning (Hours 8-24): The Communications Manager uses a pre-approved template to draft and submit the 24-hour early warning notification through the single reporting platform.
- Patch Development (Hours 24-72): Under the Technical Lead’s guidance, the engineering team races to develop and test a security patch.
- Detailed Notification (Hour 72): The Communications Manager submits the 72-hour detailed incident notification. This one includes more technical details and the initial remediation plan.
- Patch Deployment & Disclosure: The patch is rolled out to customers, and a public security advisory is issued, crediting the security researcher where appropriate.
This kind of structured process ensures you methodically meet every CRA deadline. For a deeper dive into the documentation required, our guide to CRA technical documentation has valuable insights.
Leveraging Automation to Streamline Workflows
Finally, automation is what makes your governance framework both scalable and efficient. Trying to manage these processes manually is a recipe for human error and will absolutely slow down your response time.
Think about how you can use automation to supercharge your playbooks:
- Automated Ticketing: New vulnerability submissions can automatically create tickets in your project management tool, whether it’s Jira or Asana.
- Deadline Alerts: Set up automated alerts in Slack or email to ping the PSIRT when the 24-hour and 72-hour reporting deadlines are getting close.
- Evidence Collection: Use scripts to automatically gather logs, reports, and communication records related to an incident into a single folder, making audits a breeze.
By automating these routine tasks, you free up your team to focus on the high-value work: analysis and remediation. This is how you ensure your CRA governance framework operates like a well-oiled machine.
Choosing the Right Compliance Partner for CRA
Picking the right software partner is one of the most important decisions you’ll make on your journey to Cyber Resilience Act compliance. With the clock ticking and the requirements piling up, trying to juggle everything with spreadsheets and manual tools isn’t just inefficient—it’s a massive risk. Your partner should be more than a software vendor; they need to be a strategic asset for your long-term resilience.
This decision isn’t just about finding a tool to file reports. You need a solution that simplifies the entire compliance lifecycle, from figuring out if the CRA even applies to your product all the way to post-market surveillance. A patchwork of separate tools for different tasks will inevitably create data silos, leading to errors, missed deadlines, and a chaotic audit trail no one wants to untangle.
Look for a Unified Platform
Your number one priority should be finding a unified platform that brings all your CRA-related work into one place. A solution that combines applicability assessment, requirements management, and vulnerability reporting into a single workspace gets rid of the friction and risk that comes from managing compliance across scattered systems. This is what an effective CRA single reporting platform is all about.
Just imagine your team is using one tool to see if a product is in scope, a spreadsheet to track security requirements, and a shared email inbox for vulnerability reports. When a critical vulnerability is found, your team is left scrambling to connect the dots between these three disconnected systems, all while a 24-hour reporting deadline looms. That’s a recipe for failure.
A unified platform acts as your single source of truth. It ensures that when a vulnerability is reported, your team can instantly see which products are affected, what specific CRA requirements apply, and what your reporting obligations are—all in one place.
This integrated approach doesn’t just save time and cut down on human error; it gives you a seamless, audit-ready record of all your compliance activities. It turns a horribly complex, multi-step process into a clear, manageable workflow.
Prioritise Actionable Roadmaps and Templates
The best compliance partners don’t just hand you a blank canvas and wish you luck; they give you a running start. Look for a solution that comes loaded with ready-to-use templates and can generate actionable compliance roadmaps. These features alone can save your team hundreds of hours and dramatically reduce how much you have to spend on external consultants.
Here are some key things to look for:
- Ready-to-Use Templates: Does the platform offer pre-built templates for crucial documents like the Declaration of Conformity and the technical files required by Annex VII? This ensures your paperwork is structured correctly from the very beginning.
- Automated Roadmaps: Can the software take your product information and automatically generate a tailored, step-by-step compliance plan? A good roadmap should outline specific tasks, assign them to the right people, and track your progress against key deadlines.
Practical Example: A manufacturer of smart home sensors uses a compliance platform to classify its new product. The platform immediately identifies it as a “Class I” device and spits out a complete roadmap. This plan includes tasks for running a conformity assessment, creating an SBOM, and setting up a vulnerability disclosure policy, with all deadlines neatly aligned with the CRA timeline.
Ask the Right Questions
Finally, you need to put any potential vendor through their paces to make sure they have a deep, practical understanding of the regulation. Their expertise—or lack of it—will directly shape your ability to get compliant and stay compliant.
Here are some critical questions to ask any potential partner:
- How do you keep your platform updated with new guidance from ENISA or changes to the CRA implementing acts?
- Can you walk me through how your solution helps us meet the 24-hour and 72-hour reporting deadlines for actively exploited vulnerabilities?
- How does your platform help us manage and document the product’s “expected lifetime” support period?
A partner who can give clear, confident answers to these questions is showing you they have real expertise. They won’t just sell you software; they’ll be a strategic ally in your CRA compliance journey.
Your Actionable Roadmap to CRA Readiness
Turning dense regulation into a concrete plan is the most critical part of the journey. This roadmap is designed as a straightforward, step-by-step guide for your product, compliance, and engineering teams to get started on the Cyber Resilience Act. Forget the overwhelm; this is how you move forward with confidence.

The goal here isn’t to tackle everything at once. It’s about methodical progress, starting with the most fundamental questions and building your compliance posture one logical piece at a time.
1. Assess Your Product Portfolio
Your immediate first step is to run an applicability assessment. You need to figure out which of your products with digital elements actually fall under the CRA’s scope. Remember, the regulation has a wide reach, covering everything from smart home gadgets to industrial control systems.
Practical Example: A company making both simple electronic toys and connected security cameras needs to review each product line. The toys without any network connection are likely out of scope. But the security cameras, which connect to a network for video streaming and updates, are firmly in scope. This initial sort is absolutely critical for focusing your efforts where they matter.
2. Classify and Understand Your Obligations
Once you have a list of in-scope products, you must classify them according to the CRA’s risk categories: Default, Class I, or Class II. This decision dictates the stringency of your obligations, especially when it comes to conformity assessments.
Don’t just assume your products are “Default.” Annex III of the CRA lists specific product types, like network management systems and firewalls, that automatically fall into the higher-risk Class I or Class II categories. Getting this wrong is a costly mistake.
Practical Example: A smart thermostat that simply controls heating might be a Default product requiring only a self-assessment. A home router, which manages all network traffic, is listed in Annex III as a Class I product. This means it requires a more stringent conformity assessment, potentially involving a third-party notified body.
Correct classification is the foundation for your entire compliance strategy. To help map out your timeline, have a look at our guide on the key CRA deadlines for 2025-2027.
3. Start Documenting Immediately
Whatever you do, don’t wait until the deadline is looming to start your documentation. Begin gathering evidence and creating your technical files right now. This includes your cybersecurity risk assessment, Software Bill of Materials (SBOM), and Declaration of Conformity.
Practical Example: Instead of waiting, a product manager for a new IoT device starts an SBOM from day one of development. They use a tool that tracks every open-source library added by the engineers. By the time the product launches, the SBOM is already 90% complete, saving weeks of frantic reverse-engineering work later.
Using a platform with built-in templates for Annex VII requirements can save you from a last-minute scramble and ensures your files are structured correctly from day one. This proactive approach turns a massive task into a manageable, ongoing process. Trust me, your future self will thank you for getting an early start.
Cyber Resilience Act Compliance – FAQs
As the Cyber Resilience Act comes into focus, product teams often have pressing questions about what it means for them day-to-day. Here are some of the most common queries we hear from manufacturers, with practical, straightforward answers.
Does the CRA Apply to Free Products?
Yes, absolutely. If a product with digital elements is placed on the EU market under your brand, the CRA’s rules apply, even if you give it away for free. What matters is its commercial availability in the market, not its price.
Practical Example: A company offers a free smart home app that controls its smart bulbs. Since that app is made available on the EU App Store as part of a commercial activity (selling the bulbs), it falls squarely within the CRA’s scope.
What Is an “Actively Exploited Vulnerability”?
This term has a very specific meaning. An “actively exploited vulnerability” is a security flaw that isn’t just theoretical—it’s one that attackers are currently using in the wild to compromise systems or data.
It’s crucial to understand that vulnerabilities discovered by security researchers during good-faith testing do not count as “actively exploited.” The regulation’s urgent reporting rules are triggered by malicious, real-world attacks, not responsible disclosure.
Practical Example: Your security team discovers online chatter from hacking forums detailing how to exploit a flaw in your product’s firmware, along with telemetry data showing failed login attempts matching the attack pattern. This constitutes active exploitation, triggering the 24-hour reporting clock.
What Counts as a “Severe Incident”?
A severe incident is any cybersecurity event that seriously compromises the security of the product. This isn’t just limited to end-user devices; it can also include a breach in your own development or production environment that creates a new risk for your customers.
Practical Example: Imagine an attacker injects malicious code into your update server. This is a severe incident. Even if no customer devices have downloaded the compromised update yet, the integrity of your entire update process has been breached, posing a significant downstream risk that must be reported.
Are There Different Rules for Different Products?
Yes, the CRA isn’t a one-size-fits-all regulation. It classifies products into Default, Important (Class I and II), and Critical categories based on their potential risk. While everyone has to follow the core requirements, higher-risk products face stricter conformity assessment procedures.
Practical Example: A simple consumer smart plug might be a “Default” product, allowing for a self-assessment. But a product like a router or firewall, classified as “Important,” will almost certainly need an assessment from an independent, third-party notified body to verify its security claims.
What if Our Product Is Used for Less Than Five Years?
The CRA sets a default security support window of at least five years. However, the rules are also practical. If your product has a reasonably expected lifetime that is shorter, you can align the support period to that shorter timeline.
Practical Example: The manufacturer of a disposable fitness tracker with a non-rechargeable battery that lasts for 18 months can define its support lifetime as 18 months. The key is that they must clearly document and state this expected use time in the product materials and technical files.
Ready to turn these requirements into a clear, actionable plan? Regulus provides a unified platform to assess your product portfolio, generate tailored roadmaps, and manage all your CRA obligations from a single dashboard. Stop guessing and start complying with confidence by visiting goregulus.com.