The Qualys Cloud Agent is a small, lightweight piece of software you install on your digital products to get continuous security and compliance monitoring. Think of it as a sensor that reports back on vulnerabilities, configurations, and inventory directly to the Qualys Cloud Platform. This gives you constant visibility into the security posture of your deployed assets, without ever needing to run a traditional network scan.
Why the Qualys Cloud Agent Is a Strategic Tool for EU Market Access

For any manufacturer placing products with digital elements on the European Union market, the upcoming Cyber Resilience Act (CRA) changes everything. The days of shipping a product and forgetting about its security are over. The CRA demands continuous post-market surveillance, and this is where the Qualys Cloud Agent becomes more than just an IT tool—it becomes a business enabler.
Imagine the agent as a “digital nervous system” for your products. Once deployed, it constantly reports back on their security health, no matter where they are in the world. This continuous flow of information is exactly what you need to meet the CRA’s stringent obligations.
Answering the CRA’s Toughest Questions
The CRA requires you to have clear, evidence-backed answers to critical security questions about your products after they have been sold. Manually tracking this across thousands or even millions of devices is simply impossible. The Qualys Cloud Agent helps automate this, providing the data needed for credible compliance.
Let’s look at a few practical examples for a manufacturer of smart home devices or industrial machinery:
- “A new critical vulnerability like Log4j was just announced. Are our deployed products affected?” Without an agent, finding the answer means a frantic, manual scramble. With the agent, you can query your entire fleet in minutes to identify every single vulnerable device. For instance, you could run a search for “Log4j” and instantly get a list of all deployed smart thermostats running the vulnerable Java library.
- “Can we prove to auditors that our products remain secure throughout their lifecycle?” The agent provides a continuous, time-stamped record of each asset’s patch status and configuration. For example, you can generate a report showing that 99% of your EU-deployed devices received a critical security patch within the 14-day window your policy mandates.
- “How do we know if an unauthorised change was made to a product’s software in the field?” The agent’s file integrity monitoring can flag unexpected modifications. A practical scenario: if an attacker modifies the
/etc/shadowfile on a Linux-based security camera to add a rogue user, the agent detects the change and triggers an immediate alert.
The core challenge of the CRA isn’t just about building secure products; it’s about proving they stay secure over time. The Qualys Cloud Agent provides the continuous visibility needed to demonstrate this post-market diligence to regulators.
From Technical Data to Business Insight
Ultimately, the agent transforms raw security data into actionable business intelligence. It helps your security programme move from a reactive posture—scrambling when a vulnerability is disclosed—to a proactive one where you have a system in place to quickly assess risk and orchestrate a response.
This capability is fundamental for securing your position in the EU market. By integrating a Qualys Cloud Agent into your products, you are not just installing a security feature; you are building a foundation for long-term compliance, customer trust, and sustained market access under the new regulatory framework. It empowers product security teams to confidently report on the state of their deployed assets, satisfying a key pillar of the Cyber Resilience Act.
Understanding Core Features and How They Collect Data

At its heart, the Qualys Cloud Agent is a lightweight data collector. Think of it as a discreet security sensor installed directly onto your products, designed to gather vital information without getting in the way or slowing things down. This is absolutely critical for performance-sensitive devices where every CPU cycle and kilobyte of memory counts.
The agent works by periodically collecting data and sending small, compressed updates back to the Qualys Cloud Platform. This process is incredibly efficient, sidestepping the network saturation and performance drag that often come with traditional, heavy-handed vulnerability scanners. It’s this lean approach that makes it a practical choice for a huge range of connected products.
Vulnerability Management and Discovery
One of the agent’s main jobs is Vulnerability Management (VM). It meticulously inventories all the software installed on a device, tracking versions and running services. It then cross-references this inventory against the Qualys KnowledgeBase, one of the most extensive and continuously updated vulnerability databases in the industry.
This allows the agent to pinpoint specific weaknesses with surgical precision. If a product happens to be using an outdated open-source library with a known flaw, for instance, the agent will flag it immediately.
Practical Example:
Imagine a critical vulnerability like Log4j is discovered. Without an agent, your team faces a massive, manual scramble to figure out which products in the field are affected. With the Qualys Cloud Agent, you can run a simple query and get a definitive list of all vulnerable devices in minutes, letting you prioritise your patching efforts where they matter most.
Policy Compliance and Hardening
Another core feature is Policy Compliance (PC). This module doesn’t just look for vulnerabilities; it verifies that the operating system and key applications on your product are configured securely. It checks the device’s setup against established security benchmarks, like those from the Center for Internet Security (CIS), to ensure it’s properly hardened against common attacks.
This goes beyond just finding software flaws and assesses the security posture of the system itself. This function is vital for demonstrating that your products are secure by design and, just as importantly, remain so after deployment.
Practical Example:
Consider a connected medical device. The Policy Compliance module can verify that unnecessary network ports are closed, default administrative passwords have been changed, and system logging is correctly enabled. This provides an auditable record that the device meets your organisation’s security hardening standards—a key piece of CRA-related documentation.
The real power of the Qualys Cloud Agent lies in its ability to combine vulnerability data with compliance status. This gives you a complete picture of risk, showing not just what could be exploited, but also whether configuration weaknesses make an exploit more likely.
File Integrity Monitoring for Tamper Detection
File Integrity Monitoring (FIM) is another powerful capability. It acts as a digital watchdog, monitoring critical system files and directories for any unauthorised changes, additions, or deletions. For detecting tampering or the presence of malware, this is a fundamental security control.
For manufacturers, FIM provides a crucial layer of post-market surveillance. It helps answer the all-important question: “Is the software running on my device still the software I shipped?” This is a key consideration, and you can learn more about how this fits into broader compliance through our guide on CRA logging and monitoring requirements.
Practical Example:
Suppose an attacker gains access to one of your smart meters in the field and tries to install a rogue binary in the product’s firmware. The FIM module would detect this new, unauthorised file and immediately send an alert to the Qualys platform. This can trigger an incident response process before the malicious code even has a chance to activate, providing the real-time detection essential for mitigating threats in deployed products.
The table below summarises the data collection capabilities of the Qualys Cloud Agent and connects them to specific compliance needs.
Qualys Cloud Agent Data Collection Capabilities
| Data Type Collected | Description | Example | CRA Compliance Relevance |
|---|---|---|---|
| Software Inventory | A complete list of all installed software, versions, and patch levels on the device. | openssl-1.1.1k |
Supports SBOM creation and vulnerability identification in third-party components. |
| System Configuration | Settings for the operating system, network services, and critical applications. | Checking if a default password is still active on an administrative account. | Provides evidence of "secure by default" configurations and secure hardening. |
| Network Connections | A list of all active network listeners and outbound connections from the device. | Identifying an unexpected open port like Telnet (port 23). | Helps minimise the attack surface and detect unauthorised communication channels. |
| File Changes | Tracking of additions, modifications, or deletions to critical system files and directories. | An alert is triggered when /etc/passwd is modified. |
Directly supports tamper detection and post-market surveillance obligations. |
| Hardware Details | Information about the device's CPU, memory, and other core hardware components. | Intel(R) Atom(TM) x5-E3940 |
Useful for asset inventory and understanding the operational environment. |
By collecting these different data types, the agent provides a multi-faceted view of each device’s security posture, which is exactly what regulators expect for demonstrating due diligence under the CRA.
Deploying and Managing Agents Across Your Product Lifecycle
Getting the Qualys Cloud Agent deployed and managed effectively is where the rubber meets the road for continuous security monitoring. A solid deployment plan ensures that the moment a product comes online, it starts reporting its security posture—giving you the exact evidence needed for Cyber Resilience Act (CRA) compliance.
Think of agent deployment less like a post-launch IT task and more like a core part of your manufacturing process. It should be built directly into your product’s software from the very beginning. This is the key to achieving consistency, scalability, and immediate visibility.
Baking the Agent into Your Master Image
By far, the most effective deployment strategy is to “bake” the Qualys Cloud Agent directly into your master software image. This is the foundational image used to create the software for every new device or product that leaves your facility. When you embed the agent here, you guarantee that every single unit is born with its security sensor already active.
This method completely automates the installation, wiping out any need for manual setup after the product is shipped. As soon as a customer powers on their new device and it connects to the internet, the pre-installed agent activates and checks in with the Qualys Cloud Platform.
Practical Example:
Imagine an industrial equipment manufacturer building connected machinery for factory floors. During their software development cycle, they add the Qualys Cloud Agent installer and its unique activation key to their base operating system image. Now, every new piece of machinery that ships is automatically monitored from its first day of operation, providing immediate insight into its vulnerability status without anyone lifting a finger.
Deployment in Isolated or Air-Gapped Networks
Of course, not all products live on the open internet. Many are deployed in isolated factory networks, secure data centres, or other “air-gapped” locations. For these scenarios, the Qualys Cloud Agent can be configured to communicate through a Qualys Gateway.
The gateway acts as a secure middleman. Here’s how it works:
- Agents on isolated devices send their encrypted data to the local Qualys Gateway.
- The gateway gathers up this information.
- The gateway then makes a single, secure, outbound connection to the Qualys Cloud Platform to upload all the data.
This architecture gives you full visibility over assets in restricted networks while keeping outbound traffic locked down to a single, controlled channel.
Organising agents is just as important as deploying them. By grouping agents logically, you can transform raw security data into clear, actionable compliance reports that align directly with your business structure.
Organising Agents for Effective Reporting
Once your agents are out in the field, organising them correctly is absolutely critical for efficient management and reporting. The Qualys platform lets you create agent groups and assign tags based on any criteria you can dream up. For CRA compliance, this is a game-changer.
The best practice is to create groups that mirror your product lines, geographical regions, or customer segments. For instance, you could create groups like:
Product-Line-A-Smart-Widgets-EUProduct-Line-B-Industrial-Sensors-USCritical-Infrastructure-Customers
This kind of structure simplifies everything. When a CRA auditor asks for a report on the vulnerability status of a specific product line sold in the EU, you can generate it with a few clicks instead of manually sifting through thousands of assets. It turns what could be a week-long data-gathering nightmare into a five-minute task.
This move towards consolidated security platforms is gaining serious momentum. In fact, Qualys Cloud Agent adoption jumped by 18% year-over-year, which points to a major market shift. This growth isn’t just about new installs; it shows that companies are actively standardising on a single, lightweight agent to cut complexity and broaden security coverage. For EU manufacturers facing the CRA, this highlights the value of a unified platform that delivers vulnerability management, compliance monitoring, and asset visibility without piling on operational overhead—a huge factor as adoption grows on platforms like ARM-based Linux and Apple silicon. You can explore more about these updates and the agent’s market momentum on the Qualys blog.
Security data is only useful when it drives action. Simply collecting a list of vulnerabilities is the easy part; the real work is in getting them fixed. This is where integrating the Qualys Cloud Agent into your development and operations toolchains really shines. It helps you move from a chaotic, manual scramble to a smooth, automated system for managing vulnerabilities.
This kind of integration closes the loop between finding a problem and actually fixing it. Instead of security teams dumping massive spreadsheets on engineers, you can build a workflow that automatically creates tickets, tracks progress, and confirms the fix. Not only does this massively speed up your response time, but it also gives you a clear, auditable trail for compliance purposes.
Creating an Automated Remediation Loop
A classic and incredibly effective setup is to connect Qualys with a project management tool like Jira. This automates the entire lifecycle of a vulnerability, from the moment it’s discovered to the second it’s confirmed as fixed. Getting this process right is a huge step toward meeting the Cyber Resilience Act’s demands for timely vulnerability handling.
Let’s walk through how this looks in the real world:
- Detection: A Qualys Cloud Agent, humming away on one of your deployed products, spots a new critical vulnerability—say, a remote code execution flaw in an open-source library.
- Ticketing: The Qualys Cloud Platform automatically fires off an API call, creating a new ticket in your engineering team’s Jira project. This ticket isn’t just a blank slate; it’s pre-filled with all the critical details: the vulnerability’s severity, which product models are affected, specific software versions, and clear guidance on how to fix it.
- Assignment: Based on rules you’ve already defined, the Jira ticket is automatically assigned to the right engineering team—the one that owns that specific product or software component. No more triage meetings just to figure out who owns the problem.
- Remediation: The engineers get the ticket, develop a patch, and roll it out to the affected devices in the field.
- Verification: As the patch lands on each device, its Qualys Cloud Agent automatically runs another scan. It sees that the vulnerability is gone and reports this good news back to the platform.
- Closure: The Qualys platform then talks back to Jira, automatically changing the ticket’s status to “Resolved” or “Done.” The loop is closed, all without a single person needing to manually update a status.
This kind of closed-loop system drives accountability and gives everyone real-time visibility into your security posture. You can dive deeper into building these kinds of robust processes in our guide on CRA vulnerability handling best practices.
Prioritising Fixes with Real-Time Risk Data
When you’re staring at thousands of potential vulnerabilities across your entire product portfolio, the biggest question is always: “What do we fix first?” The Qualys Cloud Agent helps you get past just looking at CVSS scores and start prioritising based on actual, real-time risk. It adds the context you need to make smart decisions.
Practical Example: A vulnerability might have a scary-looking 9.8 CVSS score, but the agent data shows it only affects products in your lab network, which are not internet-facing. Meanwhile, a “medium” 6.5 CVSS flaw is found on thousands of customer-deployed, internet-exposed devices. The agent’s context makes it clear: the medium-severity flaw is the real, immediate fire that needs to be put out first.
By combining vulnerability data with asset context—like network exposure, device criticality, and active threats—the agent empowers your team to focus their limited resources on the flaws that present the biggest, most immediate danger to your products and customers.
This risk-based approach is exactly what the CRA is pushing for. The regulation doesn’t just want you to find vulnerabilities; it demands that you manage and fix them based on the real-world risk they pose.
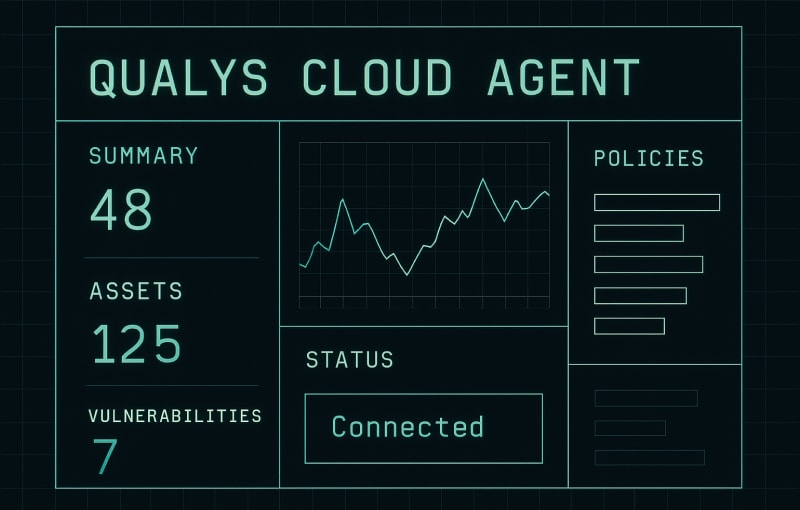
The graphic below shows a simple process for deploying agents, which is the foundational step for enabling these automated workflows.

This workflow, from embedding the agent in a master image to grouping assets for reporting, is the starting point for doing vulnerability management effectively at scale.
The trust in this model is clear from its adoption numbers. As of early 2026, there are over 110 million Qualys Cloud Agents deployed globally. That’s a huge testament to its central role in modern security. This massive scale, spanning over 10,000 customers including most of the Fortune 100, firmly establishes the agent as an industry-standard tool for continuous monitoring. For European manufacturers gearing up for CRA compliance, this widespread adoption sends a clear signal: the agent is a proven, reliable solution for meeting your vulnerability detection and surveillance duties. You can learn more about the global scale of the Qualys Cloud Agent on Qualys.com.
Limitations and Alternative Strategies for IoT Devices
While the Qualys Cloud Agent is a powerhouse for monitoring servers and traditional endpoints, it’s not a silver bullet. Its limits become obvious when you enter the world of Internet of Things (IoT) and embedded devices, where installing a full-blown software agent often just isn’t an option.
Many IoT products—think industrial sensors, medical wearables, or smart home gadgets—run on highly resource-constrained hardware. They simply lack the processing power, memory, or even the right kind of operating system to support an agent. Trying to force one on would either cripple the device’s main function or fail entirely. This is a critical hurdle for manufacturers needing the kind of comprehensive security coverage demanded by regulations like the EU’s Cyber Resilience Act (CRA) across a varied product line.
So, what do you do when you can’t put an agent on a device? You get creative.
Shifting Security Left With Firmware Scanning
When you can’t monitor a device live in the field, the next best thing is making sure it’s secure before it ever leaves the factory. This “shift left” approach moves security analysis into the development pipeline by scanning the device’s firmware.
Instead of waiting for a live agent to find problems, you analyse the complete firmware image before it’s ever flashed onto the hardware. This static analysis can uncover all sorts of issues—vulnerabilities in open-source libraries, insecure default configurations, or even hardcoded credentials baked right into the software.
- Practical Example: A smart thermostat manufacturer can integrate firmware scanning directly into their CI/CD pipeline. Before any new software update is cleared for release, its firmware image is automatically scanned for known vulnerabilities. If a critical flaw is found, the build fails, and the insecure update never reaches a single customer.
Network-Based Scanning for Agentless Devices
For devices already out in the wild that can’t host an agent, network-based scanning is a solid alternative. This technique uses a Qualys scanner appliance (either physical or virtual) placed on the same network as your IoT devices. The scanner actively probes them to identify open ports, running services, and potential vulnerabilities—all without needing any software installed on the targets.
The key takeaway here is that agentless scanning gives you essential visibility where the Qualys Cloud Agent can’t go. It fills in the gaps, covering assets that would otherwise be complete blind spots in your security posture.
This method works especially well in environments like factory floors or hospitals, where you have lots of connected devices operating on a local network. When you’re planning your security strategy, it’s vital to grasp how these specialised devices operate. As articles like “How IoT is Powering Small Business Efficiency” explain, their operational realities are very different from traditional IT assets.
To give you a clearer picture of when to use which approach, here’s a quick comparison of monitoring strategies based on device type.
Monitoring Approaches for Different Device Types
| Device Type | Recommended Approach | Why This Approach? | Practical Example |
|---|---|---|---|
| Servers & Laptops | Qualys Cloud Agent | These devices have ample resources (CPU, RAM, OS) to support a full agent, providing deep, real-time visibility. | A cloud agent on a Windows server tracking patch levels, vulnerabilities, and compliance with security policies. |
| Embedded IoT (e.g., sensors) | Firmware Scanning (Pre-market) | The device is too resource-constrained for an agent. Security must be built-in before deployment. | Scanning the firmware of a connected water meter for outdated crypto libraries before it's manufactured. |
| Agentless OT/IoT (e.g., PLCs) | Network-Based Scanning | Devices are already deployed but can't host an agent. Network probing provides external visibility. | A scanner on a factory network identifies an old, vulnerable web server running on a programmable logic controller. |
| Constrained Endpoints (managed) | Representative Monitoring | Individual devices are too simple for an agent, but they connect through a central, more powerful hub. | An agent on a building management gateway monitors traffic from hundreds of simple light sensors. |
Ultimately, choosing the right method comes down to understanding the constraints and context of each device in your ecosystem.
Representative Monitoring With a Gateway Agent
There’s also a clever hybrid strategy called “representative monitoring.” The idea is to install a single Qualys Cloud Agent on a more powerful gateway or controller that manages a fleet of smaller, agentless endpoints.
While this doesn’t give you direct insight into each tiny device, it provides incredibly valuable contextual security.
Practical Example:
Imagine a smart building where dozens of simple, low-power light sensors all report back to a central building management controller. By installing the Qualys Cloud Agent on that controller, you can monitor its security posture, track its vulnerabilities, and watch for any unusual network activity coming from the sensor network it manages. An attack on the controller could be the first sign of a wider compromise affecting all the devices connected to it.
For manufacturers dealing with a mix of complex and simple products, a combination of these strategies is usually the winning formula. To learn more about structuring a comprehensive security plan, check out our overview of endpoint protection services.
How to Meet EU Data Privacy and Hosting Requirements
If you’re selling products with digital elements in the European Union, data privacy isn’t just a “nice-to-have”—it’s a legal minefield. Getting to grips with regulations like GDPR and the fast-approaching Cyber Resilience Act (CRA) means having a solid strategy for data residency, making sure sensitive information never leaves the EU’s legal turf.
This is a critical need that the Qualys Cloud Platform addresses head-on. It was built with data sovereignty in mind, giving organisations the power to choose exactly where their security data is stored and processed. For any team using the Qualys Cloud Agent on products headed for the EU market, this feature is fundamental.
Selecting the Right Data Centre
When you first set up a Qualys subscription, you’re prompted to pick from one of several secure, geographically spread data centres, which Qualys calls “platforms.” To nail EU data residency requirements, all you have to do is select one of the EU-based platforms.
By choosing an EU platform, you ensure that all the security data collected by your Qualys Cloud Agent—from vulnerability scans to compliance checks—is stored and processed exclusively within European borders. This simple choice has massive implications for your GDPR and CRA compliance.
This decision isn’t just a technical box-ticking exercise; it’s a cornerstone of your compliance documentation. It gives you concrete proof for auditors and regulators that you are respecting Europe’s strict data privacy laws by design. To successfully meet these EU data privacy and hosting requirements, your approach must align with established governance, risk, and compliance (GRC) frameworks.
Why This Matters for CRA and GDPR
This capability gives your legal and compliance teams the confidence they need, assuring them that adopting the Qualys Cloud Agent fits perfectly with your EU market strategy. Here’s how it helps:
- GDPR Compliance: It prevents the cross-border transfer of potentially personal data collected during security scans without the necessary legal safeguards in place.
- CRA Documentation: It allows you to state definitively in your technical documentation that all post-market security surveillance data is handled in full accordance with EU regulations.
- Customer Trust: It sends a powerful signal to EU customers that you take data privacy seriously—a major deciding factor in that market.
Practical Example:
Imagine a manufacturer of smart medical devices sold across Europe. They can configure their Qualys Cloud Agent deployments to report exclusively to the Qualys EU Platform. When their legal team prepares the CRA documentation, they can include a clear statement specifying that all vulnerability and configuration data from these devices is hosted in a Frankfurt-based data centre, satisfying data residency rules from the get-go. This proactively answers key questions from regulators before they’re even asked.
Aligning your security tooling with robust data governance is also a core principle of international security standards. You can learn more about building this foundation by exploring our guide to achieving ISO 27001 ISMS certification.
Common Questions About the Qualys Cloud Agent and CRA
When you’re looking at the Qualys Cloud Agent for Cyber Resilience Act (CRA) compliance, a few practical questions almost always come up. Getting straight answers is the fastest way to decide if it’s the right tool for your product security team. Let’s tackle the most common ones.
How Much Does the Agent Impact Device Performance?
This is often the number one concern, especially if you’re working with IoT and embedded systems. The short answer is: very little. The Qualys Cloud Agent is designed to be lightweight.
It typically consumes a tiny amount of CPU—often under 2%—during its periodic checks and uses a minimal amount of RAM. Its activities are intentionally throttled to ensure it never interferes with a device’s main job.
Practical Example: On an industrial controller managing a factory assembly line, the agent might only run a full scan once every 24 hours during a low-traffic maintenance window. The data it sends back to the Qualys Cloud Platform is highly compressed, usually just a few kilobytes, so it won’t choke low-bandwidth networks or interrupt critical operations.
Can the Agent Work in Offline or Air-Gapped Environments?
Yes, it’s built for that. While the agent is designed for continuous connectivity, it works perfectly fine in disconnected scenarios. Agents installed on offline devices will continue to run scans and simply store the results locally.
Practical Example: A Qualys Cloud Agent on a piece of medical equipment in a hospital room with no internet access can store scan results for weeks. When a technician plugs the device into a maintenance port on the hospital’s network, the agent connects through a Qualys Gateway, uploads all its cached data, and downloads the latest configuration.
How Does the Agent Help With Creating an SBOM?
The agent is fundamental for generating an accurate Software Bill of Materials (SBOM). In fact, one of its first tasks after installation is to perform a deep inventory of all software on the device. This includes libraries, applications, and their exact versions.
This inventory data is the raw material for your SBOM. The Qualys platform can automatically compile this information into a detailed list of every software component—a core requirement for your CRA technical documentation.
Practical Example: An agent on a connected security camera discovers that the device is running a specific version of the OpenSSL library (1.1.1k) and the GStreamer media framework (1.14.5). This detail is instantly fed into your asset inventory, which can then be exported as an SBOM in a standard format like CycloneDX, directly supporting the CRA’s mandate for software supply chain transparency.
Does Qualys Provide Specific Reports for CRA Audits?
Absolutely. The Qualys platform lets you build customised dashboards and reports specifically for CRA compliance needs. You can easily filter your view by product line, geographical region (like “EU-deployed devices”), or vulnerability severity.
Practical Example: A regulator requests evidence of timely patching for your ‘Smart-Light-v2’ product line. Using Qualys, you can generate a report in minutes showing that all 15,000 devices in the EU received the critical ‘CVE-2024-1234’ patch within the required 14-day window. This report serves as auditable proof of your post-market security surveillance duties.
Gain clarity on your CRA obligations and build a confident path to compliance. Regulus provides the tailored roadmap, templates, and guidance your team needs to prepare for the EU market. Explore how Regulus can simplify your compliance journey at https://goregulus.com.