If you’ve stumbled here looking for “open south code,” you’re in the right place, even if the term isn’t quite right. You’re most likely looking for information on open source code, a cornerstone of modern software development. But that typo also points to something real and increasingly important: the OpenSouthCode conference in Malaga, a major hub for Europe’s open-source community.
This guide will clear up the confusion between the two, explain their growing connection, and show why it’s a topic that belongs in every product manufacturer’s boardroom.
Decoding Open South Code and Open Source
While “open south code” is a common typo, it neatly connects a place with a practice. The term you’re almost certainly after is open-source code (OSS). Think of it as a public recipe book for software; its source code is freely available for anyone to inspect, modify, and build upon. This collaborative model powers a huge portion of the digital world.
Practical Example: The popular web server software Apache HTTP Server is open source. Millions of websites use it for free, and developers worldwide can inspect its code for bugs, suggest improvements, or adapt it for their own needs.
It’s precisely this collaborative spirit that fuels events like OpenSouthCode. Since its first event in 2016, this conference has become a cornerstone for open-source advocacy in southern Spain, turning Malaga into a key meeting point for developers and hardware engineers.
The event’s rapid growth, with over 1,500 attendees in 2024 and a 35% jump in early paper submissions for 2026, isn’t just a sign of a healthy community. It signals a new urgency. To get a feel for its history and mission, you can explore the official OpenSouthCode conference website.
To make the distinction crystal clear, here’s a quick summary.
Open South Code vs Open Source Code at a Glance
| Term | Likely Meaning | Relevance to EU Manufacturers |
|---|---|---|
| Open South Code | A common typo for "open source code" or a reference to the OpenSouthCode conference in Malaga. | The conference is a key venue for learning about open-source security and compliance trends relevant to the EU market. |
| Open Source Code (OSS) | Software with publicly accessible source code that can be inspected, modified, and shared by anyone. | A critical component in most digital products. Its use brings significant cybersecurity responsibilities under the Cyber Resilience Act. |
This table clarifies that while one term is a typo, both point toward the same critical subject: the management of open-source software in commercial products.
Why This Matters Now More Than Ever
Understanding the world of open source is no longer just a technical exercise for developers. With the EU’s Cyber Resilience Act (CRA) deadlines fast approaching, it has become a C-suite concern for any company making products with digital elements for the European market.
The core issue is simple: if your product uses open-source components—from a smart thermostat’s operating system to a connected car’s infotainment unit—you are responsible for their security. The CRA places liability squarely on the manufacturer, not the original open-source contributor.
Practical Example: A company manufactures a smart home hub that uses an open-source library called libconnect to handle network communication. If a vulnerability is found in libconnect, the company that sold the hub is responsible for providing a patch to its customers, not the volunteer who originally wrote libconnect.
This shift in responsibility makes industry gatherings like OpenSouthCode more critical than ever. They are where developers, product managers, and compliance officers learn about the latest vulnerabilities, security best practices, and strategies for navigating complex regulations. For a deeper analysis of the legal frameworks, our guide on open source licensing and its implications is a must-read.
Beyond traditional software, these considerations are also crucial for emerging technologies. This is especially true for Open Source AI Models, which introduce their own unique set of risks and regulatory hurdles. As we’ll explore, knowing exactly what’s inside your software is the non-negotiable first step toward compliance.
The Hidden Risks of Open-Source Code in Your Products
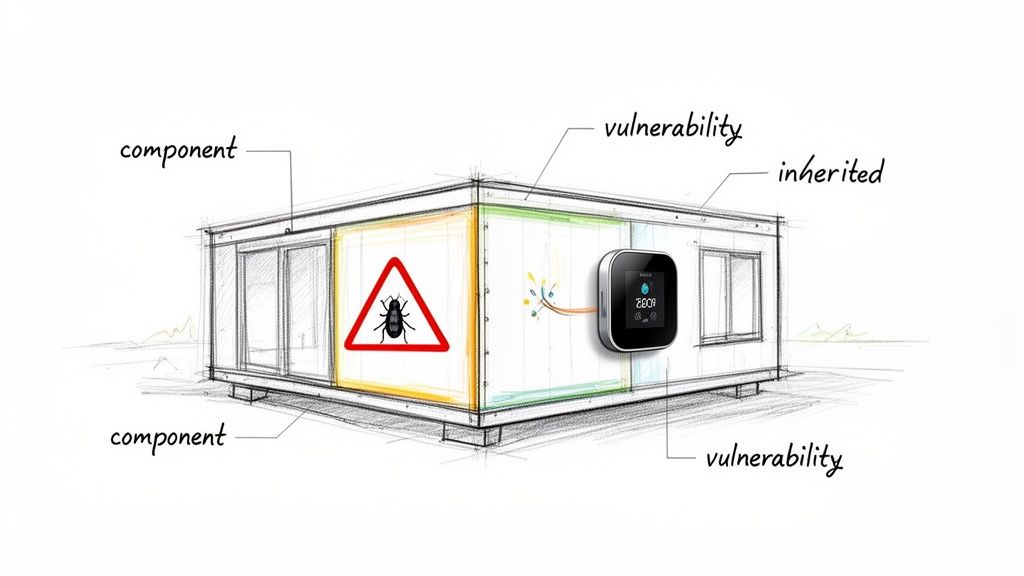
Using open-source software (OSS) is a bit like building a house with high-quality, pre-fabricated parts. It speeds up innovation, drives down development costs, and gives you access to a huge community of developers. But there’s a critical catch: you also inherit any defects hidden inside those parts.
This is the central trade-off of open-source. While it delivers incredible advantages, it also introduces serious risks, from inherited vulnerabilities to tricky licensing rules that can quickly turn into legal headaches. Understanding this balance is no longer optional for manufacturers.
Practical Example: A company making smart thermostats uses a popular open-source operating system to power their devices, allowing them to get their product to market fast. But when a new vulnerability like Log4Shell is discovered in a logging library used by that OS, millions of homes could suddenly be at risk, and the manufacturer is the one left holding the bag.
The Problem of Inherited Vulnerabilities
The most immediate risk of using open-source code is inheriting security flaws. When you pull a third-party library into your project, you’re also pulling in every bug and vulnerability it contains. If you aren’t tracking these components meticulously, you won’t even know when a new flaw is found.
This isn’t just a theoretical problem. Across the ES region, especially in Andalusia, the adoption of open-source software in manufacturing has boomed. Forecasts show that 62% of IoT and embedded device firms will rely on OSS for their firmware by 2025. This very dependency was a hot topic at recent OpenSouthCode conferences, where 2024 panels revealed a sobering statistic: 29% of southern Spanish products with digital elements contained unpatched OSS flaws. These are exactly the issues the EU’s Cyber Resilience Act is designed to fix. You can read more about these findings on the international status of OSS.
This reality means any product classified as “critical” under the CRA’s Annex I will face intense scrutiny. Suddenly, managing open-source components shifts from a development best practice to a legal necessity.
Practical Example: An Unseen Flaw in a Smart Lock
Let’s look at a company producing smart locks. They use a well-known open-source cryptography library to secure communications.
- The Component: The library is reputable and used across thousands of projects.
- The Flaw: A security researcher discovers a subtle bug allowing a specific, malformed data packet to bypass the lock’s authentication.
- The Impact: Every single smart lock using this library is now vulnerable. An attacker could exploit this flaw to unlock doors without a key, creating a severe physical security risk for every customer.
The lock manufacturer is now on the hook for patching thousands of devices, managing public disclosures, and facing potential regulatory fines.
The core principle of the Cyber Resilience Act is that the manufacturer is responsible for the security of the entire product throughout its lifecycle. This includes every line of open-source code integrated into it.
This level of accountability brings us to the need for a comprehensive Software Bill of Materials (SBOM), which acts as a detailed “ingredients list” for your software. Without a solid SBOM, it’s nearly impossible to track which open-source components are in your products, let alone manage their vulnerabilities. You can learn more about how these flaws are exploited in our guide on understanding supply chain attacks.
Licensing and Compliance Risks
Beyond security vulnerabilities, open-source licences introduce another layer of risk. Not all licences are created equal. Some, like the MIT or Apache licences, are very permissive. Others, known as “copyleft” licences (like the GPL), come with far stricter rules.
Practical Example: A startup builds a proprietary video editing software. Their developers unknowingly include an open-source library licensed under the GNU General Public License (GPL). The GPL requires that any software which uses a GPL component must also be released under the GPL. The startup now faces a legal crisis: either release their own valuable source code for free or re-engineer their product from scratch to remove the GPL component, causing massive delays and costs.
Using a component with a strong copyleft licence might legally force you to make your own proprietary source code public. An accidental violation can lead to intellectual property disputes and expensive legal battles. This is why a thorough “open-source code” strategy must include both security vetting and licence compliance, ensuring every component you use aligns with your business goals.
Understanding Your CRA Obligations with Open Source
If you’re integrating open-source code into your products, you’re no longer just a user of free software. Under the Cyber Resilience Act, you become a manufacturer with legal responsibilities. Navigating these rules is critical, and it all starts with a simple question: does the CRA even apply to your product?
For any product with “digital elements”—basically, any software or firmware—that you plan to sell on the EU market, the answer is almost certainly yes. This net catches everything from smart home devices and industrial sensors to standalone software. And no, using what some might call “open south code” (a common typo for open-source code) doesn’t give you a free pass. In fact, it puts your product squarely under the CRA’s microscope.
Once you’ve established the CRA applies, your next job is to classify your product. The regulation uses a risk-based approach, sorting products into different classes with escalating security duties.
Demystifying CRA Product Classes
The CRA divides products into a “Default” class and two “Critical” classes. Figuring out where your product fits is the key to understanding your specific obligations. You can’t afford to get this wrong.
Here’s a quick breakdown of the classes:
- Default Class: This is the baseline for most products with digital elements. If your product isn’t explicitly listed in one of the Critical Classes, it lands here. Practical Example: A smart toaster, a connected toy, or a consumer-grade fitness tracker.
- Critical Class I: These are products that carry a higher intrinsic risk. This category includes things like password managers, network management systems, and microprocessors intended for sensitive environments. Practical Example: A home network router or a standalone password manager application.
- Critical Class II: Reserved for the highest-risk products where failure could have severe consequences. Examples include industrial control systems running critical infrastructure and the core operating systems for many servers and desktops. Practical Example: The operating system for a hospital’s patient data server or software running a power plant’s control system.
A good analogy is vehicle safety ratings. A standard family car (Default Class) must have essential safety features. But a tanker truck designed to transport hazardous materials (Critical Class) is subject to far more specialised and stringent protective measures. The responsibility scales with the potential for harm.
The crucial takeaway is this: the more critical your product, the more rigorous your compliance obligations become. A smart light bulb and a hospital’s patient monitoring device both contain open-source code, but their regulatory burdens are worlds apart.
To help manage the demanding process of meeting these regulatory requirements, many organisations seek out specialised support. This might include a dedicated compliance managed service to help organise evidence and prepare for audits.
Your Responsibilities as a Manufacturer
No matter your product’s class, using open-source code means you inherit specific duties under the CRA. The regulation makes it crystal clear: you can’t just pass the buck to the original open-source developers. Your primary obligations include:
- Security by Design and by Default: Your product must be built to be secure from the ground up and shipped with secure default settings. This means vetting every single open-source component before it goes into your product.
- Vulnerability Handling: You are legally required to have a structured process for finding, managing, and fixing vulnerabilities. This absolutely includes flaws discovered in the open-source libraries you’ve used.
- Providing Security Updates: Manufacturers must provide timely security updates for a reasonable period, generally accepted as five years or the product’s expected lifetime. This includes patching vulnerabilities in third-party code.
- Clear Documentation and Instructions: You have to give users clear instructions on how to use the product securely, including details on its security features and the defined support period.
This is where having a complete software “ingredients list”—a Software Bill of Materials (SBOM)—becomes non-negotiable. Without one, you simply can’t prove you are fulfilling these duties. If you want to get into the weeds on this topic, our detailed guide on CRA SBOM requirements explains exactly how to create and manage this critical document. Using open-source software makes these tasks central to your entire compliance strategy.
Your Step-By-Step Open Source Compliance Plan
Knowing the rules is one thing, but turning them into action is what will prepare you for the Cyber Resilience Act. For any manufacturer using open-source code—which, by the way, is often mistakenly searched for as “open south code”—this means building a structured, repeatable process. A solid plan is your best defence against non-compliance penalties and, more importantly, against security breaches.
This section gives you a practical roadmap. We’ll break down the legal obligations into a clear, four-part plan that your team can follow to turn complex requirements into manageable tasks.
Step 1: Create a Software Bill of Materials
The absolute foundation of your compliance strategy is the Software Bill of Materials (SBOM). Think of it as a detailed ingredients list for your software. It needs to meticulously document every single component, library, and module that makes up your product, especially every piece of open-source code.
Practical Example: For a smart camera, your SBOM would list the specific version of the Linux kernel, the OpenSSL library used for encryption, the libjpeg library for image processing, and all other third-party components. Each entry would include the component name, supplier, version, and unique identifiers.
Without an SBOM, you’re flying blind. You simply cannot secure components you don’t even know you’re using. The CRA makes vulnerability management a core duty, and an SBOM is the only realistic way to fulfil that obligation. It’s your starting point for risk assessment, vulnerability scanning, and proving due diligence.
Thankfully, you don’t have to do this by hand. Standard formats like CycloneDX and SPDX are widely supported, and plenty of tools, both open-source and commercial, can scan your codebase to generate these files for you automatically.
Your journey to CRA compliance follows a few key stages. This simple flow shows how your initial obligations fit together.
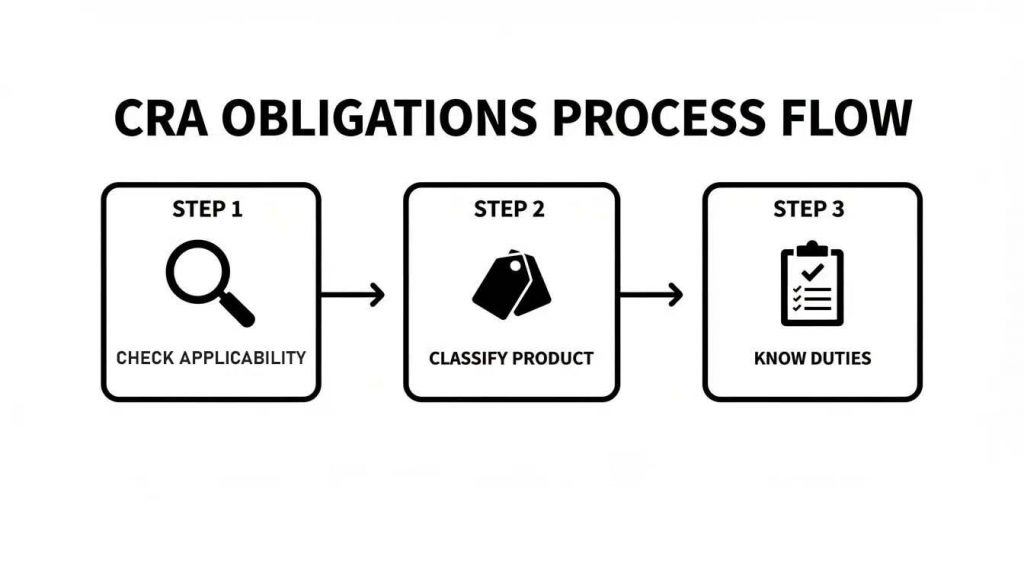
As you can see, understanding your duties comes directly from classifying your product correctly—a process that is impossible without first knowing its complete software composition.
Step 2: Set Up Continuous Vulnerability Scanning
Once your SBOM is ready, you need to monitor it constantly. Vulnerability scanning isn’t a one-time check; it’s an ongoing process. New security flaws in open-source projects are found every single day, so you must have a system in place to spot them as they appear.
This involves using automated tools to check the components in your SBOM against public vulnerability databases. When a match pops up, your security team gets an alert and can start assessing the risk.
Practical Example: Your scanning tool alerts you that OpenSSL version 3.0.1, listed in your SBOM, is vulnerable to a high-severity flaw (a new CVE). Your security team is immediately notified, investigates if your product uses the vulnerable function, and if so, prioritizes creating and deploying a patch.
A key part of modern vulnerability management is using formats like the Vulnerability Exploitability eXchange (VEX). A VEX document acts as a companion to your SBOM, allowing you to clarify whether a known vulnerability actually affects your product, reducing alert fatigue and helping your team focus on genuine threats.
For a hands-on approach, you can explore tools built for exactly this purpose. Our guide on using the OWASP Dependency-Check tool is a great starting point for integrating automated scanning right into your development workflow.
Step 3: Prepare Your Technical Documentation
The CRA demands extensive technical documentation to prove your product is compliant. This goes far beyond just having an SBOM. You need to assemble a complete file that demonstrates your security posture from the first design sketch to final deployment.
Before you can place your product on the market, you must be able to demonstrate how you’ve addressed the CRA’s requirements. To help you structure this, the following table outlines the key actions and documentation needed when using open-source software.
CRA Compliance Actions for Products Using OSS
| Compliance Area | Key Action | Relevant CRA Article/Annex | Practical Example |
|---|---|---|---|
| Supply Chain Transparency | Generate and maintain an SBOM in a machine-readable format. | Article 10(2), Annex II | Creating a CycloneDX or SPDX file listing all open-source libraries and their versions. |
| Risk Assessment | Analyse risks associated with open-source components, including their dependencies. | Article 10(2), Annex I | Documenting a risk assessment that evaluates a known vulnerability in an open-source library. |
| Vulnerability Management | Establish a process to identify, verify, and remediate vulnerabilities in OSS components. | Article 10(6), Annex I | Setting up automated alerts for new CVEs in dependencies and having a documented patch policy. |
| Secure Update Mechanism | Ensure you can securely deliver patches for vulnerabilities found in OSS components. | Article 10(5), Annex I | Implementing a firmware-over-the-air (FOTA) update system with cryptographic signature verification. |
| User Communication | Provide users with security instructions and information, including the SBOM upon request. | Article 10(8), Annex II | Including a section in the user manual on how to securely configure the product and where to find support. |
This documentation is not just a formality; it’s a legal requirement and your primary evidence of due diligence. Having a clear framework saves your team from reinventing the wheel and ensures nothing gets missed.
Step 4: Build a Secure Update Process
Finally, you must have a reliable and secure way to deploy patches. Under the CRA, manufacturers are obligated to provide timely security updates for the product’s expected lifetime or a minimum of five years.
This means you need a robust mechanism to:
- Develop and test patches for vulnerabilities found in your product, including those in its open-source components.
- Securely deliver these updates to all devices in the field, protecting the update files from being tampered with.
- Clearly communicate the availability and importance of security updates to your users.
Practical Example: A vulnerability is found in the Wi-Fi driver used by your smart speaker. Your team develops a patch. You then push this update via your secure Firmware-Over-The-Air (FOTA) server. The speaker downloads the update, verifies its cryptographic signature to ensure it’s authentic and untampered, and then installs it. Customers are notified of the update via the companion mobile app.
Failing to patch a known, exploited vulnerability in a timely manner is a direct violation of the CRA. Your update infrastructure is just as critical as the security of the product itself, as it’s your only way to respond to threats that emerge after the product has shipped.
How Regulus Simplifies Your Open Source Compliance
Navigating the Cyber Resilience Act’s demands often feels like trying to assemble a complex machine without the instructions. The rules are intricate, the stakes are high, and the widespread use of open-source code—sometimes mistyped as “open south code”—adds another layer of risk that many teams are unprepared for. Regulus is designed to cut through that confusion, transforming a regulatory headache into a clear, manageable workflow.
Instead of your team getting lost in dense legal articles and vague guidelines, our platform acts as your digital compliance expert. It translates the CRA’s requirements into a practical, personalised checklist for your product, even if it depends on hundreds of open-source components.
This structured approach is particularly critical for today’s product teams. Open-source software is everywhere. For instance, the OpenSouthCode conference in Malaga, a major hub for this community, saw attendance grow by 500% since 2016, with 1,800 attendees expected by 2026. This reflects a massive industry trend: regional data shows OSS adoption in IoT manufacturing is set to hit 71% by 2025.
But this growth introduces serious compliance risks. In Spain, 55% of connected products fall into the CRA’s Default Class, each needing over a dozen security measures. Yet, 34% lack the post-market surveillance processes the CRA mandates. For the small and medium-sized firms that make up 65% of Malaga’s tech industry, our analysis shows a 22% higher risk of fines without automated tools to manage compliance. You can explore broader economic data through the United Nations’ statistical divisions.
Automated Product Classification and Mapping
One of the first—and most important—steps is classifying your product correctly. If you get this wrong, you’ll be following the wrong rules, wasting engineering time and leaving yourself exposed. Is your smart speaker a “Default” product, or do its features push it into “Critical Class I”?
Regulus takes the guesswork out of this crucial decision. The platform guides you through a series of straightforward questions about your product’s function and intended use, helping you determine its official CRA classification with confidence.
Practical Example: You manufacture a smart baby monitor. Regulus asks if it handles sensitive personal data (yes), connects to the internet (yes), and is intended for a vulnerable population (yes). Based on your answers and the CRA’s criteria, it helps you classify the product, likely as Critical Class I, and then automatically generates the corresponding compliance checklist.
Once your product is classified, Regulus automatically maps out your specific obligations. It generates a requirement matrix that tells you precisely which security measures, documentation, and processes apply. This turns a mountain of regulatory text into a focused, actionable plan.
Ready-To-Use Documentation Templates
The CRA demands a huge amount of technical documentation, from risk assessments to the final declaration of conformity. Building these documents from scratch is not only time-consuming but also requires deep legal and technical knowledge, often leading teams to rely on expensive consultants and messy spreadsheets.
Regulus provides a full library of ready-to-use templates that are directly aligned with the CRA’s annexes. These aren’t just blank forms; they are structured documents designed to guide you in gathering and presenting the right evidence, ensuring nothing gets missed.
Practical Example: You need to create a risk assessment document. Instead of starting from a blank page, you open the Regulus template. It already contains sections for asset identification, threat modeling, and risk evaluation, with prompts explaining what evidence to provide for each—such as linking to the specific open-source components from your SBOM that pose the highest risk.
This single feature can save your team hundreds of hours. More importantly, it gives you the confidence that you are building a compliant technical file right from the start. You simply follow the template, fill in your product-specific details, and link to your evidence.
Vulnerability Management Guidance
For any product built with open-source software, vulnerability management is no longer just a best practice—it’s a legal requirement. The CRA mandates a formal, documented process for identifying, managing, and fixing security flaws throughout your product’s entire support lifecycle.
Regulus gives you clear, operational guidance for setting up this process. Our platform helps you define a robust workflow for:
- Detection: How you will find vulnerabilities lurking in your open-source dependencies.
- Reporting: The exact steps you must take to report significant flaws to authorities like ENISA.
- Remediation: Your internal policy for developing and deploying security patches in a timely manner.
By giving your team a clear roadmap for one of the toughest parts of open-source compliance, Regulus prepares you for the 2026 deadlines and beyond. It’s all about turning abstract regulatory obligations into a straightforward and achievable project plan.
Your Top Open-Source Questions Answered
Once teams start digging into the Cyber Resilience Act, the same practical questions about open-source software always pop up. It’s where the legal text meets the reality of modern development. Let’s tackle these pressing concerns head-on.
Am I Responsible for Vulnerabilities in an Open Source Library I Did Not Write?
Yes, without a doubt. The CRA is crystal clear on this point: if you are the manufacturer placing the final product on the EU market, you are 100% liable for the security of all its components. It makes no distinction between the code your team wrote and the open-source library you pulled from GitHub.
Practical Example: Your connected coffee machine uses an open-source library to parse XML data. A critical vulnerability is discovered in that library. Even though you didn’t write a single line of that library’s code, as the coffee machine’s manufacturer, you are legally obligated to patch the vulnerability for all your customers.
This is precisely why a complete Software Bill of Materials (SBOM) is no longer a “nice-to-have”; it’s your foundational tool for compliance. You simply have to know what’s inside your product to manage its security. Ignoring a known, fixable vulnerability in a dependency is a direct violation of your obligations and can lead to serious penalties.
Does The CRA Apply to My Internal Development Tools?
This is where it gets a little more nuanced, but the core principle is simple. The CRA applies to “products with digital elements” placed on the market. So, if your internal tools are used only within your company and never make their way into the final product, they generally fall outside the Act’s scope.
However, that line can get blurry fast. The real test is whether a piece of software is part of the final product that goes to the customer.
- Example 1 (Out of Scope): Your team’s internal bug-tracking system (like a self-hosted Jira). It helps you build the product, but it doesn’t ship with it. Therefore, it’s not covered by the CRA.
- Example 2 (In Scope): An open-source graphics rendering library your developers use. If that library is compiled into your product’s firmware, it’s absolutely in scope. You are now responsible for its security.
Always focus on the final shipped product. If a component is in the final build, it’s your responsibility.
The rule of thumb is straightforward: if the code ships, you are liable. This is why a thorough audit of what actually gets compiled into your firmware is so important. Many teams are surprised by what they find.
What if an Open Source Project Does Not Provide a Patch?
This is a scenario every manufacturer needs to plan for. Under the CRA, your responsibility to your customers doesn’t vanish just because an upstream open-source project is unmaintained or unresponsive. Relying on the goodwill of unpaid volunteers is not a compliant security strategy.
When a patch isn’t available, you are obligated to manage the risk yourself. This means you must:
- Assess the Risk: First, figure out the vulnerability’s actual impact on your product. Can it be exploited in your specific configuration? How severe is it for your users?
- Mitigate or Patch: If the risk is significant, you are expected to step in. This could mean developing your own patch, creating a temporary workaround, or implementing other mitigations to protect your users. You cannot knowingly leave them exposed.
- Disclose Responsibly: You must inform your users about the vulnerability and the steps you’ve taken. For serious issues, the CRA requires you to report them to the relevant authorities, like ENISA, within very strict timelines.
Practical Example: Your IoT device uses a small, decade-old open-source library for parsing dates, and its author is unreachable. A security flaw is found. Your team must analyze the flaw. If it’s exploitable, your engineers will have to either write a patch for the library themselves or replace the library with a more modern, maintained alternative, then push the fix to customers.
This reality highlights just how crucial it is to choose your open-source dependencies wisely. A project with an active community and a clear security policy is a far safer bet than one that’s been abandoned. Even a simple typo like “open south code” can be a clue about a project’s level of maintenance and support—factors that are vital for long-term security.
How Does Using a Major Linux Distribution Affect My CRA Obligations?
Building your product on a major, well-supported Linux distribution like Debian, Ubuntu, or a Yocto Project build can be a huge help. These projects have dedicated security teams that actively track vulnerabilities and release patches, which can definitely make your compliance job easier than if you were building a custom Linux system from individual components.
However, it does not remove your responsibility. As the manufacturer, you are still the one the CRA holds accountable.
When using a distribution, your duties include:
- Timely Patch Deployment: You need a solid process to get security patches from the distribution, test them, and roll them out to your devices without delay.
- Accurate SBOM: Your Software Bill of Materials has to be specific, listing the exact distribution version and all packages installed on the final product.
- Responsibility for Customisations: You are entirely responsible for any custom applications, drivers, kernel modules, or configurations you add on top. These are common places for new vulnerabilities to appear, and the distribution’s security team won’t cover them.
Practical Example: You build a network-attached storage (NAS) device using Ubuntu Server. When the Ubuntu security team releases a patch for the sudo command, your responsibility is to integrate that patch into your NAS firmware, test it to ensure it doesn’t break your custom storage management software, and then push the update to your customers’ devices. You are also solely responsible for securing the web interface you built to manage the NAS.
Think of it like building a car. You might use a high-quality engine from a reputable supplier, but you (the car manufacturer) are still responsible for installing it correctly, connecting it to the rest of the car, and ensuring the final vehicle is safe to drive.
Managing these complex duties for every open-source component can feel overwhelming. Regulus provides a structured platform to automate your CRA compliance, from product classification and documentation to vulnerability management. Get the clarity and tools you need to confidently meet your 2026 obligations. Learn how Regulus can simplify your compliance strategy.