CRA Requirements
-
Testing for sql injection: Essential Guide to Secure Your Applications
At its heart, testing for SQL injection is about sending carefully crafted inputs to an application to see if you can trick its database. It’s a hands-on method for finding those dangerous cracks in the armour where an attacker could slip through, bypass security, steal data, or even corrupt your entire database. Proactive, effective testing…
-
How to obtain a CE certificate for the CRA: A practical guide
Getting your product CE certified under the Cyber Resilience Act (CRA) might seem daunting, but it’s a journey with a clear, logical path. This guide is your practical roadmap, designed to turn the CRA’s complex legal requirements into a straightforward, actionable plan for manufacturers. Your Practical Roadmap to CRA CE Certification The Cyber Resilience Act…
-
The Top 12 Firewall Open Source Solutions for 2026
In today’s interconnected environment, securing your network perimeter is non-negotiable. While commercial solutions abound, the firewall open source ecosystem offers powerful, flexible, and transparent alternatives for businesses, home labs, and even complex IoT projects. These community-driven projects provide robust security features without the hefty price tag or vendor lock-in, giving you complete control over your…
-

A Practical Guide to NIST SP 800-53 for EU Compliance
If you’ve spent any time in cybersecurity, you’ve likely come across NIST Special Publication (SP) 800-53. It’s a beast of a document, a massive catalogue of security and privacy controls developed by the U.S. National Institute of Standards and Technology. Although it started life as a framework for American federal agencies, it’s now recognised globally…
-

Your Practical Guide to ISO 27001 ISMS Certification
An ISO 27001 ISMS certification is the official seal of approval showing that your company’s Information Security Management System (ISMS) meets a tough international standard. It’s more than just a certificate; it’s a clear, strategic signal to customers and partners that you take information security seriously and manage risks in a systematic way. Why ISO…
-
A Practical Guide to Open Source Licensing
An open source license isn’t just a file you find in a code repository; it’s the legal agreement that spells out exactly what you can—and absolutely cannot—do with free, publicly available code. Think of it as the rulebook for collaboration, designed to keep innovation flowing while still protecting the rights of the original creators. Why…
-
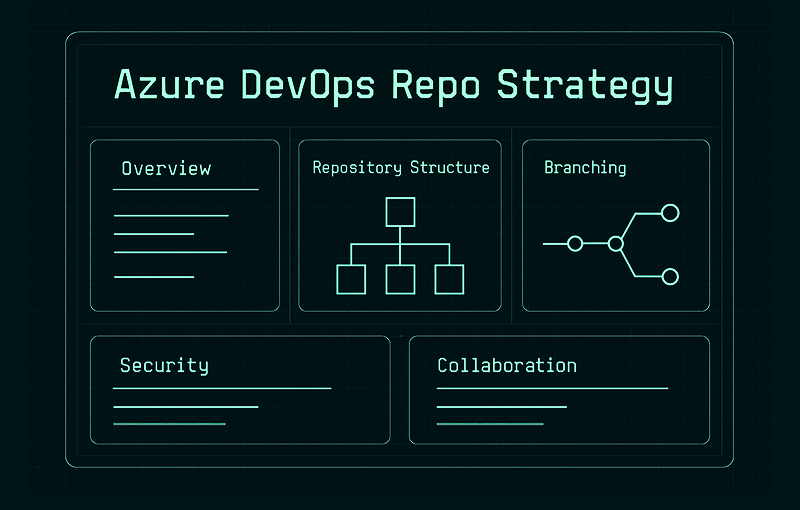
A Guide to Mastering Your Azure DevOps Repo Strategy
An Azure DevOps Repo is a version control system baked right into the Azure DevOps suite, giving your team a central place to manage, track, and collaborate on your codebase. It’s far more than just a folder for your files; it’s a complete toolkit for modern software development that supports both Git and Team Foundation…
-
GitLab Jira Integration A Guide to Faster DevSecOps Workflows
Connecting GitLab to Jira does more than just link two tools; it creates a single, unified workflow between your code repository and your project management hub. When you set this up, actions like code commits, creating branches, and opening merge requests can automatically update the right Jira issues. For instance, a developer can push a…
-
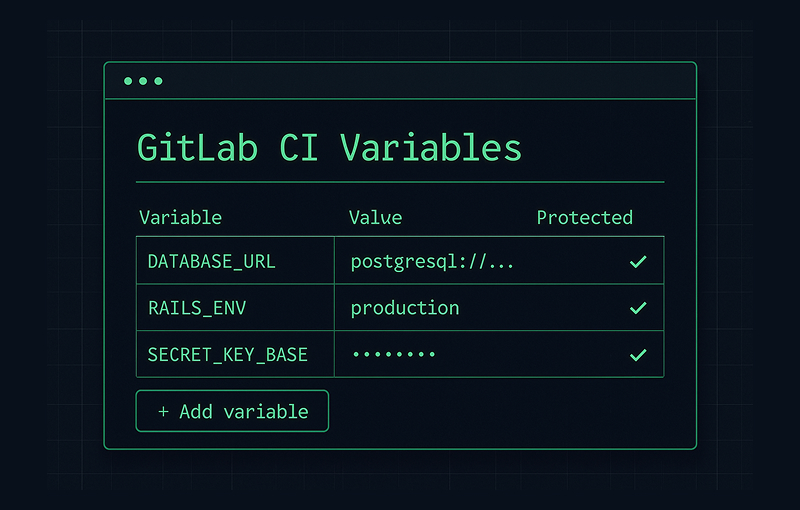
A Guide to GitLab CI Variables for Secure Pipelines
GitLab CI variables are the secret ingredient for building dynamic, secure, and adaptable automation. At their core, they are simply placeholders for information your pipeline needs while it’s running. Think of them as secure digital vaults where you store everything from server passwords to version numbers, keeping your CI/CD process both flexible and safe. Why…
-
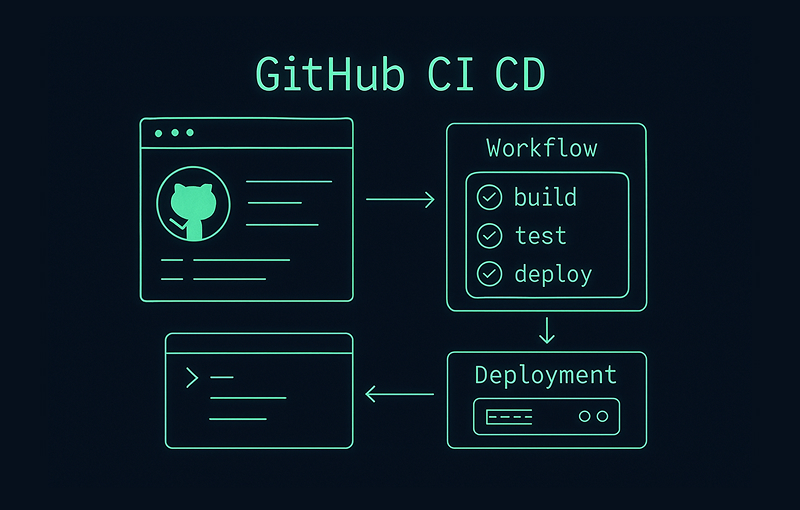
A Practical Guide to GitHub CI CD for Secure Product Development
At its core, GitHub CI/CD is the native, integrated way to automate your software builds, tests, and deployments, all handled directly within your GitHub repository. The feature that powers this is called GitHub Actions. It lets developers cook up custom workflows that kick off automatically based on events like code pushes or new pull requests.…
-
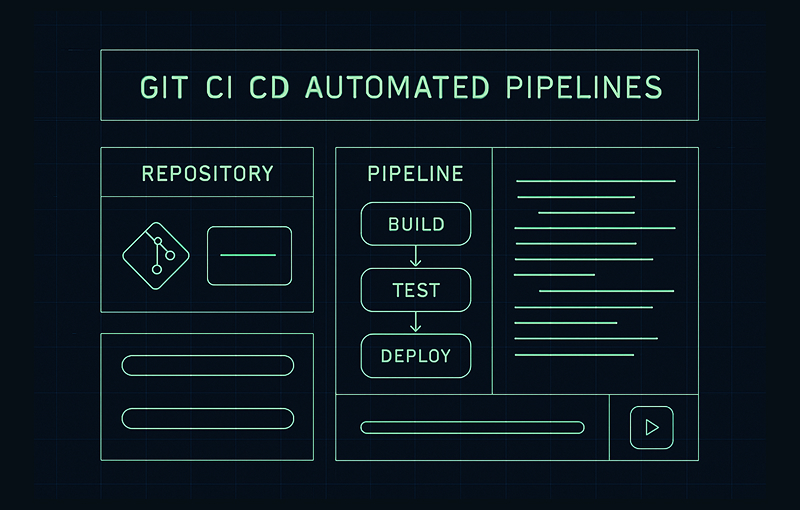
A Practical Guide to Git CI CD Automated Pipelines
When you’re staring down the barrel of modern compliance demands, especially regulations like the European Union’s Cyber Resilience Act (CRA), a Git CI/CD pipeline is your single most powerful ally. It takes what used to be a mountain of manual checklists for building, testing, and deploying software and transforms it into a smooth, auditable, and…
-
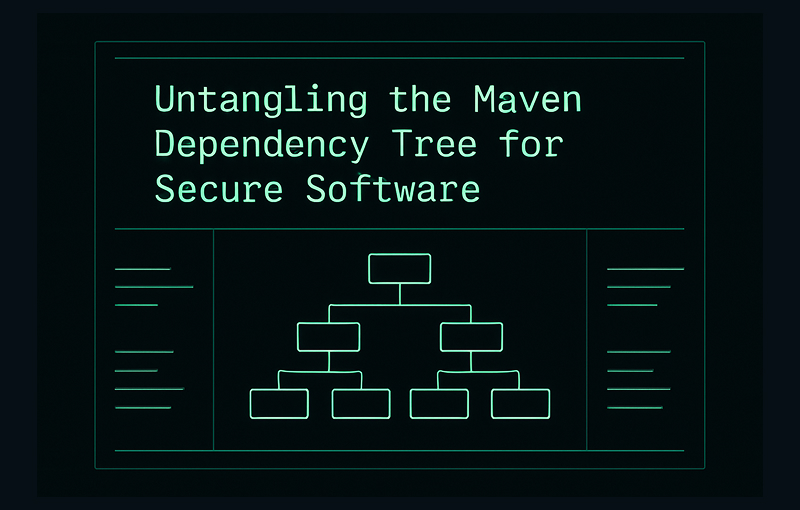
Untangling the Maven Dependency Tree for Secure Software
Managing your Maven dependency tree is much more than a build-time convenience; it’s a critical security and compliance function. Don’t think of it as a simple list. See it for what it truly is: the complete architectural blueprint of your software’s supply chain. This blueprint reveals every single component, both direct and inherited, that makes…
-
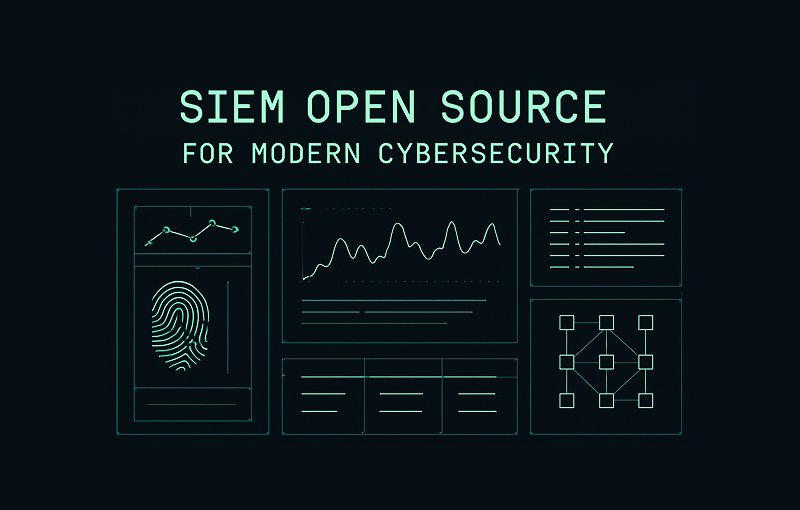
A Practical Guide to SIEM Open Source for Modern Cybersecurity
An open-source SIEM is a Security Information and Event Management platform built on publicly available source code. This means it’s fundamentally free-to-use—anyone can inspect, modify, and build upon it. It delivers the core functions you’d expect from any SIEM, like log collection, threat detection, and security monitoring, but without the hefty upfront licensing fees that…
-

A Practical Guide to Scan for Malware in Apps and IoT Devices
To really get a handle on scanning for malware in your applications and IoT devices, the first thing to realise is why you’re doing it. This isn’t just a technical chore to tick off a list. It’s about protecting your market access, securing your supply chain, and staying on the right side of tough regulations…
-
Your Guide to the National Vulnerability Database
The National Vulnerability Database (NVD) is the U.S. government’s public library for cybersecurity vulnerabilities. It takes the raw list of Common Vulnerabilities and Exposures (CVEs) and enriches it with crucial analysis, like severity scores and details on affected software. Think of it as the place that provides the full story behind every identified digital flaw.…
-
Path Traversal Attack Your Guide to CRA Compliant Security
A path traversal attack, sometimes called directory traversal, is a classic web security vulnerability that lets an attacker read—and in some cases, write to—files they should never be able to reach. It’s a simple but powerful trick. Attackers pull this off by manipulating file paths using the “dot-dot-slash” (../) sequence. Think of ../ as a…
-
Your Guide to Cross Site Scripting Attacks and Prevention
Cross-site scripting, or XSS, is one of the most persistent and damaging vulnerabilities plaguing the web. It’s a sneaky type of attack where a threat actor injects malicious code, usually JavaScript, into a legitimate website. When an unsuspecting user visits that site, their browser executes the script, believing it’s part of the trusted content. The…
-
A Practical Guide to SQL Injection Test Labs and Vulnerability Hunts
A SQL injection test is a security procedure we use to find vulnerabilities in an application’s database layer. It’s all about sending carefully crafted, malicious SQL queries to an input field—like a search bar or login form—to see if the application will blindly execute them. If it does, an attacker could potentially expose, manipulate, or…
-

A Practical Guide to the OWASP Top Ten for CRA Compliance in 2026
The OWASP Top Ten provides an essential framework for identifying the most critical security risks facing web applications, IoT devices, and embedded systems. For manufacturers targeting the European market, this list is no longer just a set of best practices. It has become a direct map to the security obligations mandated by the EU’s Cyber…
CRA Requirements: what the EU Cyber Resilience Act demands and how to operationalize it
CRA Requirements are the obligations set by the EU Cyber Resilience Act (CRA) for products with digital elements placed on the EU market. They focus on reducing cybersecurity risk through security by design and by default, consistent vulnerability management, and clear accountability across the product lifecycle.
This page consolidates practical resources and related posts to help teams interpret CRA, implement them in engineering and operations, and maintain audit-ready evidence over time.
What counts as CRA in practice
CRA Requirements typically span product security engineering, supply chain controls, documentation, and post-market processes. The goal is to make cybersecurity measurable and maintainable rather than ad hoc.
Who needs to care about CRA
CRA Requirements can affect manufacturers, software publishers, importers, distributors, and other parties involved in delivering products with digital elements. If you build or ship software, connected devices, or components that end up in the EU market, you should assume CRA Requirements are relevant to your product governance and delivery model.
Core CRA Requirements for products with digital elements
Although the details depend on product category and risk profile, most implementations of CRA Requirements can be organized into a few operational domains.
Security by design
Security by design requires embedding cybersecurity controls into architecture and development practices from the earliest stages, minimizing attack surface and preventing common classes of vulnerabilities.
Security by default
Security by default means shipping products with secure configurations out of the box. Default credentials, unnecessary services, and permissive settings should be avoided unless there is a justified and controlled need.
Vulnerability handling and coordinated disclosure
CRA Requirements push organizations to implement a repeatable vulnerability lifecycle: intake, triage, prioritization, remediation, validation, and communication. Clear channels and responsibilities are essential.
Secure development lifecycle controls
- Threat modeling and security requirements definition
- Secure coding standards and peer review practices
- Automated security testing integrated into CI/CD
- Release gating based on severity and risk acceptance
Supply chain and dependency risk management
CRA Requirements extend to the software and component supply chain. Organizations should track critical dependencies, assess risk, and maintain the ability to rapidly respond to vulnerabilities in third-party components.
Technical documentation and compliance evidence
CRA Requirements are enforceable only if organizations can demonstrate that controls are implemented and maintained. Documentation should be consistent, traceable, and versioned.
Common evidence artifacts aligned to CRA Requirements
- Product security architecture notes and threat models
- Risk assessments and mitigation plans
- Security testing results and remediation records
- Component inventory and SBOM where applicable
- Vulnerability management policy and operating procedures
- Support, update, and end-of-life policy
How to implement CRA step by step
A strong implementation turns CRA Requirements into concrete controls, measurable outcomes, and sustained operational routines.
Step 1: define scope, product boundaries, and ownership
- Identify products and versions in scope
- Map responsibilities across product, engineering, security, legal, and support
- Define an internal compliance owner and escalation paths
Step 2: map CRA Requirements to your SDLC and operations
- Translate requirements into security controls, policies, and runbooks
- Embed controls into development workflows and release processes
- Operationalize monitoring, vulnerability intake, and patch delivery
Step 3: establish metrics and continuous improvement
- Remediation time by severity and component criticality
- Testing coverage across code, dependencies, and releases
- Update adoption and support window adherence
- Defect trends and recurring vulnerability classes
Related posts about CRA
This section is intended to host posts that unpack CRA Requirements by theme and provide implementation guidance.
Interpretation and scope
CRA explained: scope, roles, and obligations
A practical breakdown of what CRA Requirements mean for product teams and how to translate them into responsibilities and delivery milestones.
Engineering and security controls
Security by design vs security by default under CRA
How to implement secure architectures and ship hardened defaults while keeping usability and operational constraints in mind.
Vulnerability and disclosure
Vulnerability handling aligned to CRA
How to design an intake-to-fix workflow, set internal SLAs, validate patches, and communicate updates effectively.
Supply chain
SBOM and dependency governance for CRA
How to build practical dependency visibility and response capability without creating operational overhead.
Audit readiness
Evidence pack for CRA: what to collect and how to maintain it
Which artifacts matter most, how to version them, and how to keep evidence current as products evolve.
Download free CRA Checklist 2025
The definitive CRA checklist for assessing your organization’s readiness for the Cyber Resilience Act.
By submitting this form, you accept our Terms and acknowledge that Regulus will process your data to send the checklist. For more details, see our Privacy Policy.