CRA Requirements
-
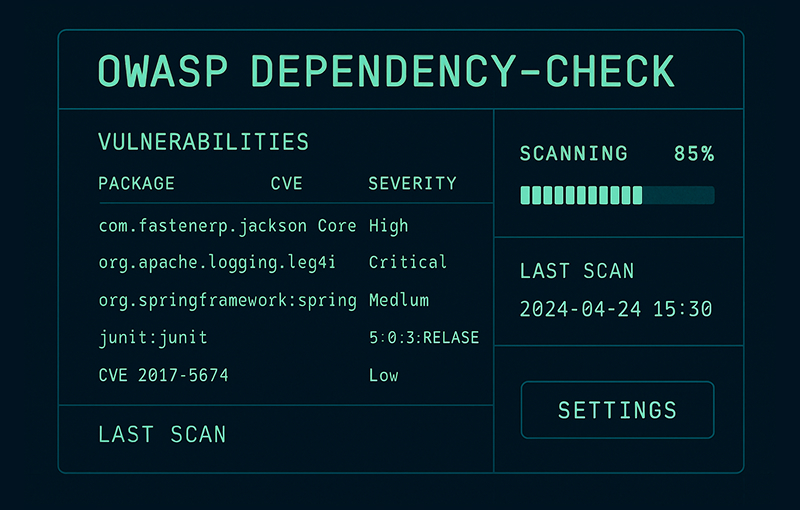
OWASP Dependency-Check: How It Works, Examples, and CRA Use Cases
OWASP Dependency-Check is an open-source Software Composition Analysis (SCA) tool used to identify known vulnerabilities in third-party dependencies. It scans project dependencies against public vulnerability databases such as the NVD and produces detailed reports to help teams assess security risks. This guide explains how OWASP Dependency-Check works in practice, shows concrete usage examples, and clarifies…
-
A Practical Guide to Static Code Analysis
Think of static code analysis as a spellchecker, but for your source code. It’s an automated process that scans your code for potential errors, vulnerabilities, and deviations from best practices before you even try to run it. It’s like having an expert engineer meticulously review every line of a building’s blueprint for structural flaws before…
-
A Guide to Dynamic Application Security Testing for CRA Compliance
Dynamic application security testing (DAST) is a black-box security testing method that probes an application from the outside, mimicking exactly how a real-world attacker would approach it. DAST interacts with the application while it’s running—without any knowledge of its internal code or architecture—to find vulnerabilities that only show up during operation. This approach is essential…
-

Secure SDLC (Secure Software Development Lifecycle): Phases, Checklist, and Policy
A secure software development life cycle (SDLC) is a framework that weaves security practices into every single stage of creating software. Instead of treating security as a final check before launch, it becomes a core part of the process from the very beginning. This concept is often called ‘Shift Left’, and it’s all about building…
-

A Guide to the Modern Product Lifecycle Manager
When you hear the term product lifecycle manager, it’s easy to get confused. Are we talking about a person or a piece of software? The answer is both. The term refers to two distinct but deeply connected concepts: a strategic professional role and a powerful software tool. Both are absolutely essential for steering a product…
-
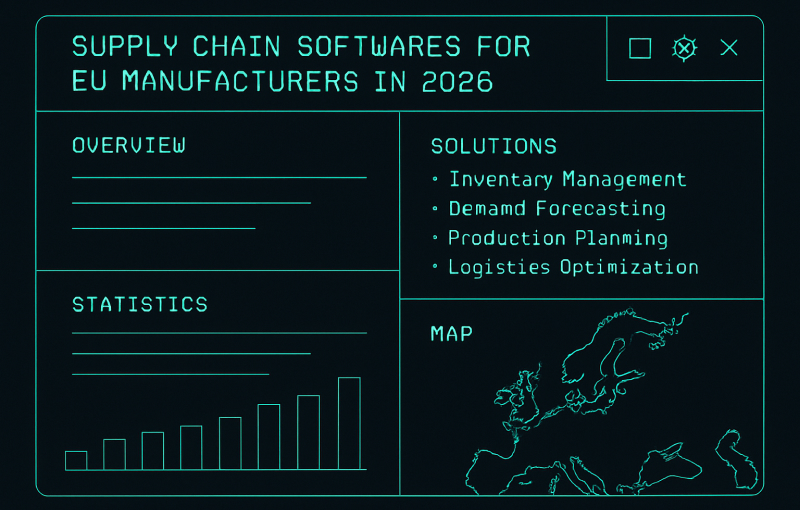
Top 12 Supply Chain Softwares for EU Manufacturers in 2026
The European Union’s upcoming Cyber Resilience Act (CRA), set to be enforced from 2026, fundamentally changes the requirements for manufacturers. Selecting the right supply chain softwares is now a critical task, shifting from a focus purely on operational efficiency to one centred on compliance, security, and sustained market access. This guide is designed to help…
-
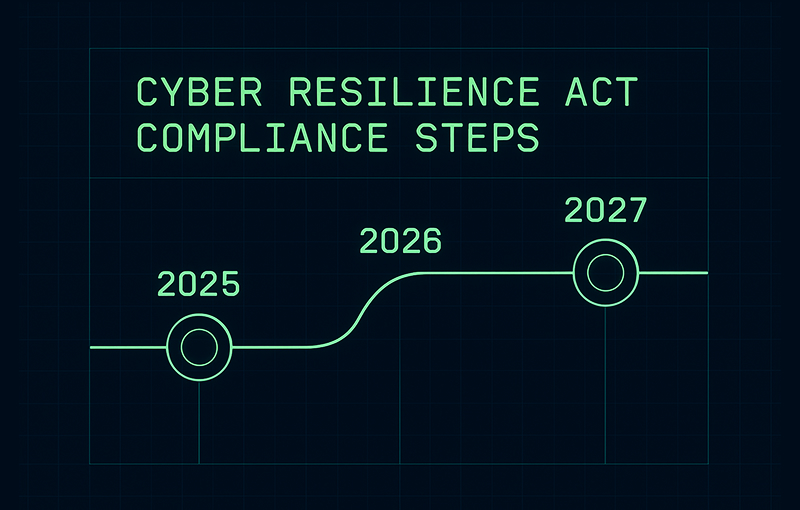
Cyber Resilience Act Compliance Roadmap 2025–2027: Complete Guide
This long-form guide provides a complete Cyber Resilience Act compliance roadmap for manufacturers, importers and distributors of products with digital elements. It explains CRA scope, obligations, deadlines 2025–2027, key technical requirements and documentation, and links to detailed articles, templates and checklists to help you move from awareness to execution.
-
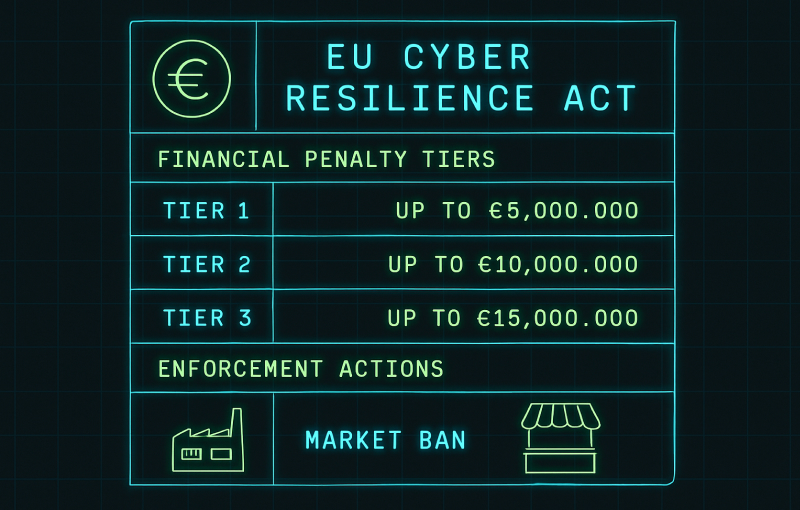
CRA Penalties and Enforcement: Complete Guide
CRA penalties can reach up to €15 million or 2.5% of global annual turnover, and authorities can also order recalls, withdrawals and market bans. This guide explains how CRA penalties work, the different fine tiers, how enforcement is applied in practice and what manufacturers, importers and distributors can do to reduce enforcement risk.
-
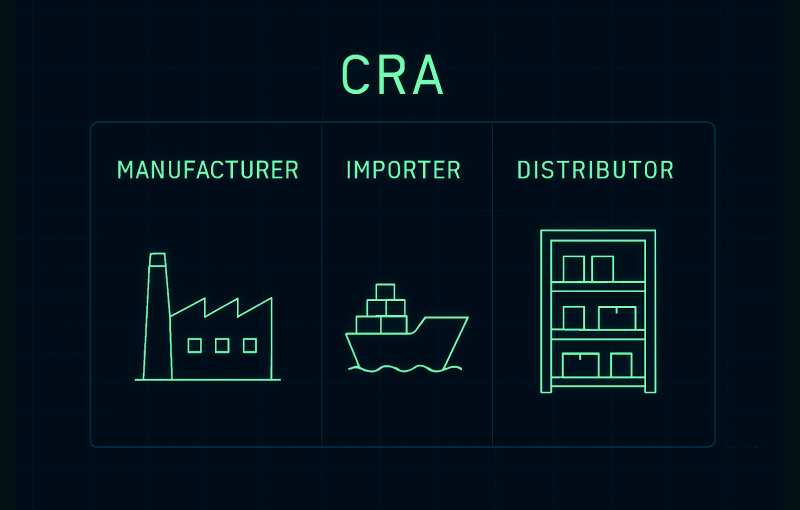
CRA Manufacturer, Importer and Distributor Obligations: Complete Guide
The Cyber Resilience Act introduces specific obligations for manufacturers, importers and distributors of products with digital elements in the EU. This guide explains CRA manufacturer obligations in depth, shows how importer and distributor duties compare and clarifies when an importer or reseller becomes a manufacturer in the eyes of the regulation.
-
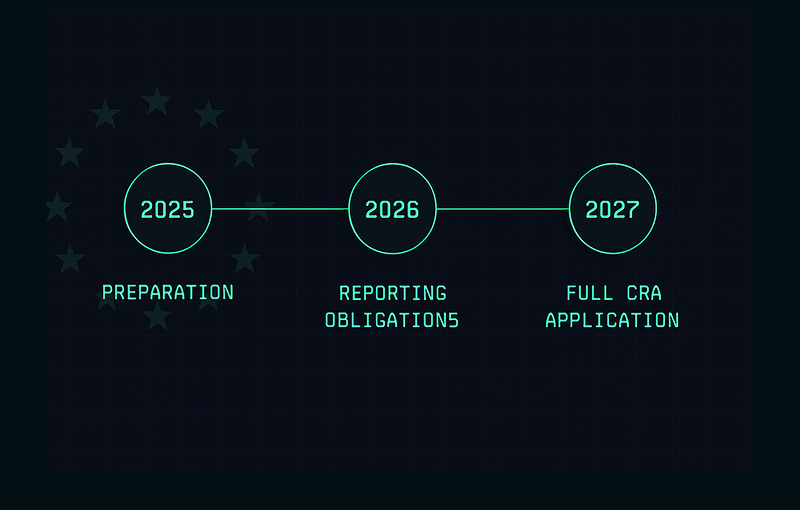
CRA Deadlines 2025–2027: Key Dates and What Manufacturers Must Do
Understand CRA deadlines 2025–2027. This guide explains the official Cyber Resilience Act timeline, what changes in 2025, 2026 and 2027, and how manufacturers, importers and distributors should plan their compliance roadmap.
-
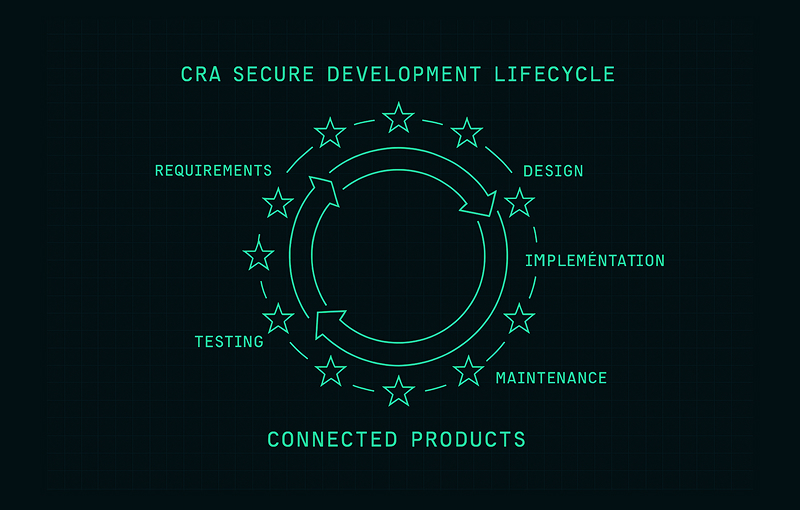
CRA Secure Development Lifecycle (SDL): Practical Guide for Manufacturers
A practical guide to the CRA secure development lifecycle. Learn how SDL activities, controls and documentation support Cyber Resilience Act compliance across the product lifecycle.
-

CRA Logging and Monitoring Requirements: Complete Guide
CRA logging and monitoring requirements help you detect incidents, investigate root causes and prove security controls over time. Learn what to log, how to protect and retain logs, and how to document telemetry for compliance.
-

CRA Declaration of Conformity (DoC) Guide: How to Build a Compliant CRA DoC
A practical guide to the CRA Declaration of Conformity. Learn how to structure a Cyber Resilience Act DoC, what it must contain, how it connects to the technical file and common mistakes to avoid.
-
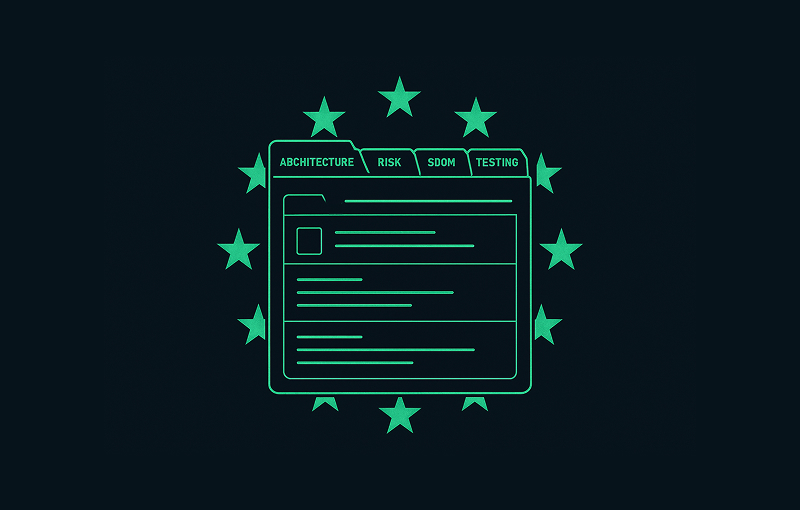
CRA Technical File Structure: Complete Guide for Cyber Resilience Act Compliance
A practical guide to CRA technical file structure. Learn how to organise Cyber Resilience Act technical documentation, from product architecture and risk assessment to SBOM, testing evidence and lifecycle security.
-
Cyber Resilience Act FAQ: 30 Essential Questions Answered
A practical Cyber Resilience Act FAQ for manufacturers, IoT vendors and software teams. This guide answers the most common CRA questions about scope, obligations, deadlines, documentation, SBOM and conformity assessment.
-

CRA SBOM Requirements: Complete Guide for Manufacturers, IoT Vendors and Software Teams
CRA SBOM requirements make component transparency a compliance obligation. Learn what your SBOM should include, which formats work (SPDX/CycloneDX), and how SBOMs support vulnerability handling before 2027.
-
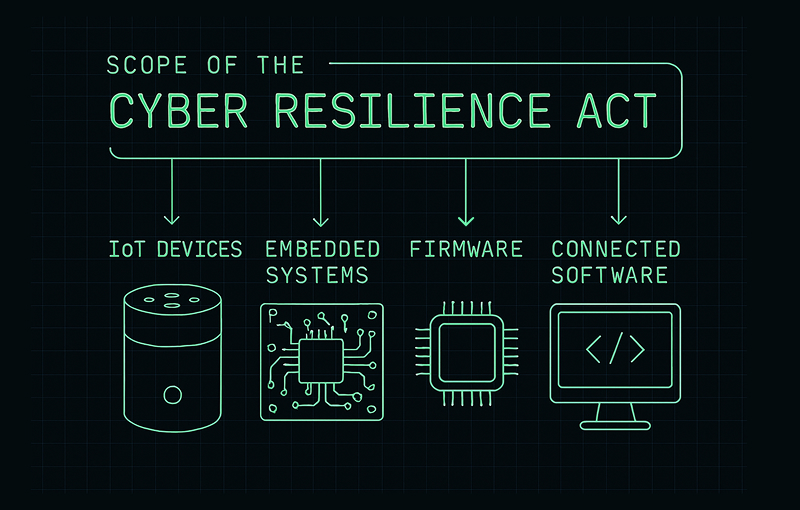
CRA Scope Explained: What Products Are In and Out (Complete Guide)
A practical guide to understanding the scope of the Cyber Resilience Act (CRA). Learn which products are in scope, which are excluded, and how to determine whether your digital product must comply with the CRA.
-

CRA Risk Assessment: Requirements, Methodology & Templates
A complete, in-depth guide to CRA cybersecurity risk assessments. Learn how to meet Annex I, II and VII requirements, structure a compliant analysis, build threat models, document vulnerabilities, evaluate risks, map mitigations and prepare audit-ready technical documentation for Cyber Resilience Act conformity.
-

CRA Conformity Assessment: Internal Control vs Third-Party Assessment (Complete Guide)
Understand how CRA conformity assessment works under the Cyber Resilience Act, including the differences between Internal Control and Third-Party Assessment, when each pathway applies, and what manufacturers must prepare to achieve compliance.
-

CRA Update & Patch Management Requirements: Complete Guide for Manufacturers and Software Teams
CRA update and patch management requirements make secure updates and lifecycle support mandatory. Learn what the CRA expects for signed delivery, validation, rollback prevention, user communication and Annex II/VII evidence.
CRA Requirements: what the EU Cyber Resilience Act demands and how to operationalize it
CRA Requirements are the obligations set by the EU Cyber Resilience Act (CRA) for products with digital elements placed on the EU market. They focus on reducing cybersecurity risk through security by design and by default, consistent vulnerability management, and clear accountability across the product lifecycle.
This page consolidates practical resources and related posts to help teams interpret CRA, implement them in engineering and operations, and maintain audit-ready evidence over time.
What counts as CRA in practice
CRA Requirements typically span product security engineering, supply chain controls, documentation, and post-market processes. The goal is to make cybersecurity measurable and maintainable rather than ad hoc.
Who needs to care about CRA
CRA Requirements can affect manufacturers, software publishers, importers, distributors, and other parties involved in delivering products with digital elements. If you build or ship software, connected devices, or components that end up in the EU market, you should assume CRA Requirements are relevant to your product governance and delivery model.
Core CRA Requirements for products with digital elements
Although the details depend on product category and risk profile, most implementations of CRA Requirements can be organized into a few operational domains.
Security by design
Security by design requires embedding cybersecurity controls into architecture and development practices from the earliest stages, minimizing attack surface and preventing common classes of vulnerabilities.
Security by default
Security by default means shipping products with secure configurations out of the box. Default credentials, unnecessary services, and permissive settings should be avoided unless there is a justified and controlled need.
Vulnerability handling and coordinated disclosure
CRA Requirements push organizations to implement a repeatable vulnerability lifecycle: intake, triage, prioritization, remediation, validation, and communication. Clear channels and responsibilities are essential.
Secure development lifecycle controls
- Threat modeling and security requirements definition
- Secure coding standards and peer review practices
- Automated security testing integrated into CI/CD
- Release gating based on severity and risk acceptance
Supply chain and dependency risk management
CRA Requirements extend to the software and component supply chain. Organizations should track critical dependencies, assess risk, and maintain the ability to rapidly respond to vulnerabilities in third-party components.
Technical documentation and compliance evidence
CRA Requirements are enforceable only if organizations can demonstrate that controls are implemented and maintained. Documentation should be consistent, traceable, and versioned.
Common evidence artifacts aligned to CRA Requirements
- Product security architecture notes and threat models
- Risk assessments and mitigation plans
- Security testing results and remediation records
- Component inventory and SBOM where applicable
- Vulnerability management policy and operating procedures
- Support, update, and end-of-life policy
How to implement CRA step by step
A strong implementation turns CRA Requirements into concrete controls, measurable outcomes, and sustained operational routines.
Step 1: define scope, product boundaries, and ownership
- Identify products and versions in scope
- Map responsibilities across product, engineering, security, legal, and support
- Define an internal compliance owner and escalation paths
Step 2: map CRA Requirements to your SDLC and operations
- Translate requirements into security controls, policies, and runbooks
- Embed controls into development workflows and release processes
- Operationalize monitoring, vulnerability intake, and patch delivery
Step 3: establish metrics and continuous improvement
- Remediation time by severity and component criticality
- Testing coverage across code, dependencies, and releases
- Update adoption and support window adherence
- Defect trends and recurring vulnerability classes
Related posts about CRA
This section is intended to host posts that unpack CRA Requirements by theme and provide implementation guidance.
Interpretation and scope
CRA explained: scope, roles, and obligations
A practical breakdown of what CRA Requirements mean for product teams and how to translate them into responsibilities and delivery milestones.
Engineering and security controls
Security by design vs security by default under CRA
How to implement secure architectures and ship hardened defaults while keeping usability and operational constraints in mind.
Vulnerability and disclosure
Vulnerability handling aligned to CRA
How to design an intake-to-fix workflow, set internal SLAs, validate patches, and communicate updates effectively.
Supply chain
SBOM and dependency governance for CRA
How to build practical dependency visibility and response capability without creating operational overhead.
Audit readiness
Evidence pack for CRA: what to collect and how to maintain it
Which artifacts matter most, how to version them, and how to keep evidence current as products evolve.
Download free CRA Checklist 2025
The definitive CRA checklist for assessing your organization’s readiness for the Cyber Resilience Act.
By submitting this form, you accept our Terms and acknowledge that Regulus will process your data to send the checklist. For more details, see our Privacy Policy.
