The European Union’s Cyber Resilience Act (CRA) is about to overhaul digital product safety, and its latest version puts high-risk vendors squarely in the spotlight with much stricter rules. If your company makes hardware or software with digital parts for the EU market, this isn’t just another update. It transforms cybersecurity from a “nice-to-have” into a hard legal requirement you can’t afford to ignore.
Understanding The New Cyber Resilience Act Rules
For a long time, the cybersecurity of digital products was more of a suggestion than a rule. The EU’s Cyber Resilience Act (CRA) flips that script completely. A good way to think about it is how safety standards became mandatory for cars or home appliances. The CRA does the exact same thing for the security of every “product with digital elements” sold inside the EU.
This means if you’re a manufacturer, developer, or importer of anything from a smart thermostat to industrial control systems or even standalone software, you’re now legally on the hook to build security in from the very start. The whole idea revolves around security-by-design, making sure products are not only secure out of the box but stay that way for their entire lifespan. To really get a handle on these new duties, it helps to understand what regulatory compliance entails in a broader sense.
A New Focus On High-Risk Vendors
One of the biggest shifts in the CRA is its new risk-based classification system. The regulation is smart about this—it recognises that not all digital products are created equal when it comes to risk. A connected light bulb, for instance, just doesn’t pose the same threat as a network router that guards a company’s entire digital fortress.
So, the EU CRA revamp singles out high-risk vendors by creating specific categories based on a product’s potential for causing serious disruption if it gets compromised. This tiered system makes sure that the most critical products get the toughest security checks and face the most stringent ongoing obligations. You can get up to speed on the core concepts in our detailed overview of the https://goregulus.com/cra-basics/cyber-resilience-act/.
What Does This Mean For Your Business?
The CRA’s rules create a clear list of responsibilities that go far beyond just the development stage. You now have to think about the entire lifecycle of your products. This includes:
- Vulnerability Management: You must have a solid process for finding, reporting, and patching security holes. This isn’t optional, and it comes with a strict 24-hour deadline to report actively exploited vulnerabilities to ENISA, the EU’s cybersecurity agency. For example, if a security researcher finds a flaw in your smart lock’s firmware that is being used by criminals to open doors, you have 24 hours from discovery to officially report it.
- Security Updates: You’re now obligated to provide security updates for a reasonable period, ensuring your products are protected against new threats long after they’ve been sold. A practical example would be a software vendor for a point-of-sale system that must continue to issue patches for five years, matching the device’s expected lifespan.
- Supply Chain Transparency: You need to be able to document every software component inside your products. This is often done with a Software Bill of Materials (SBOM) so you can quickly trace any potential vulnerabilities back to their source.
The Cyber Resilience Act shifts the burden of liability from the consumer to the manufacturer. It establishes a clear legal expectation that digital products sold in the EU must be secure, effectively ending the era of “sell and forget.”
This is a massive change, and it means every business needs a solid plan to get ready. The transition period has already started, with full compliance becoming mandatory by the end of 2027. The time to start assessing your product line-up, understanding your specific duties, and building a roadmap for this new era of digital liability is right now.
How To Identify High-Risk Products Under The CRA
The EU Cyber Resilience Act doesn’t just paint everything with the same broad brush. Instead of a one-size-fits-all approach, it uses a smart, risk-based system that scales the rules to match the potential danger. It’s a bit like vehicle licensing—you don’t need the same permits for a family car as you do for a tanker carrying hazardous chemicals.
This tiered approach is the core of how the EU CRA revamp targets high-risk vendors. By sorting products into different classes, the regulation makes sure that the most critical digital components get the toughest security checks. For you, the first step to compliance is figuring out exactly where your products land in this structure.
This visual shows how the CRA’s legal requirements flow downwards, creating specific rules that define what makes a product—and by extension, its vendor—high-risk.
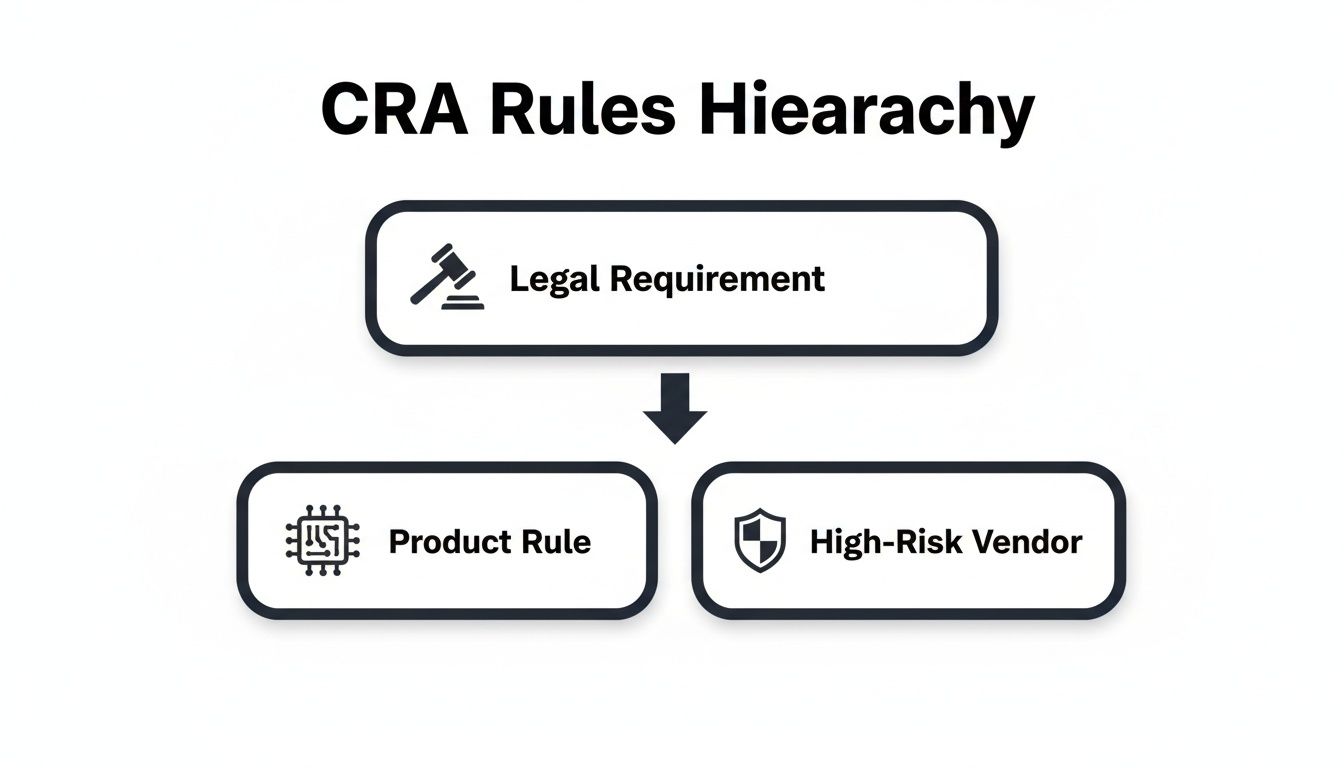
As you can see, being labelled a high-risk vendor isn’t random. It’s a direct result of your product’s function and its position in the wider digital ecosystem.
To help clarify these distinctions, the table below breaks down the CRA’s product classes, their risk levels, and what they mean in the real world.
CRA High-Risk Product Classifications Explained
| Product Class | Risk Level | Conformity Assessment | Practical Example |
|---|---|---|---|
| Default | Low | Self-assessment by the manufacturer is sufficient. | A smart toaster or a word processing application. |
| Critical Class I | Significant | Self-assessment is possible if harmonised standards are followed; otherwise, a third-party assessment is mandatory. | A home network router or a password manager application. |
| Critical Class II | High | Mandatory third-party assessment by a Notified Body is always required. No self-assessment option. | An industrial control system for a power grid or a hardware security module (HSM). |
Understanding these categories is the foundation of your compliance journey, as each class comes with a very different set of obligations.
Understanding The Default Category
The vast majority of digital products will land in the Default category. These are items where a cybersecurity slip-up would be an annoyance for an individual but isn't likely to cause widespread societal or economic chaos.
For these products, manufacturers are allowed to perform a self-assessment to declare they meet the rules. This puts the responsibility on you to run your own security checks, pull together the required technical documents, and issue an EU declaration of conformity.
Think of a smart coffee machine. If a vulnerability lets someone remotely turn it on, it’s a nuisance for the owner, but it’s not going to trigger a systemic crisis. Other examples include smart speakers, connected toys, and most consumer software like a photo editing app.
Classifying Critical Class I Products
One step up the ladder, we find Critical Class I. This bucket is for products that handle more sensitive tasks or are more deeply woven into our digital lives. A security failure here could easily affect multiple systems or users, creating a much bigger problem.
Products in this class face a tougher conformity process. You can still do a self-assessment, but only if you stick strictly to a harmonised standard. If you don't, a mandatory third-party assessment from a designated Notified Body becomes a requirement.
- Example 1: Network Routers. A router is the gatekeeper for all internet traffic in a home or office. A flaw could expose every connected device, opening the door to data theft or a complete network shutdown.
- Example 2: Password Managers. These tools are vaults for our most sensitive credentials. A breach here could lead to the mass takeover of user accounts across countless services.
- Example 3: Firewalls. A firewall is a network’s first line of defence. If it goes down, an organisation’s entire digital infrastructure could be left wide open to attack.
For a deeper look into the evaluation process, our guide on conducting a CRA risk assessment breaks down the details you’ll need to navigate.
Identifying Critical Class II Products
At the very top sits Critical Class II. This is the highest-risk category, reserved for products that are fundamental to critical infrastructure or perform functions where a failure could have catastrophic consequences for public safety, the economy, or national security.
Given their extreme risk profile, these products are always subject to mandatory third-party conformity assessments. There’s no self-assessment option here—the stakes are simply too high.
Clear examples include:
- Industrial Control Systems (ICS). These are the brains behind power plants, water treatment facilities, and factory floors. A cyberattack could shut down essential services for millions.
- Hardware Security Modules (HSMs). These specialised devices protect the digital keys used for strong authentication in banking and government systems. If they're compromised, the trust in entire digital systems could collapse.
- Operating Systems. The core software running on our desktops and servers is foundational. A deep-rooted vulnerability could have a global ripple effect.
Getting your product classification right is the non-negotiable first step. It determines everything that follows, from the type of assessment you’ll need to how intensely you must monitor your products after they hit the market.
Meeting Your New Obligations As A High-Risk Vendor
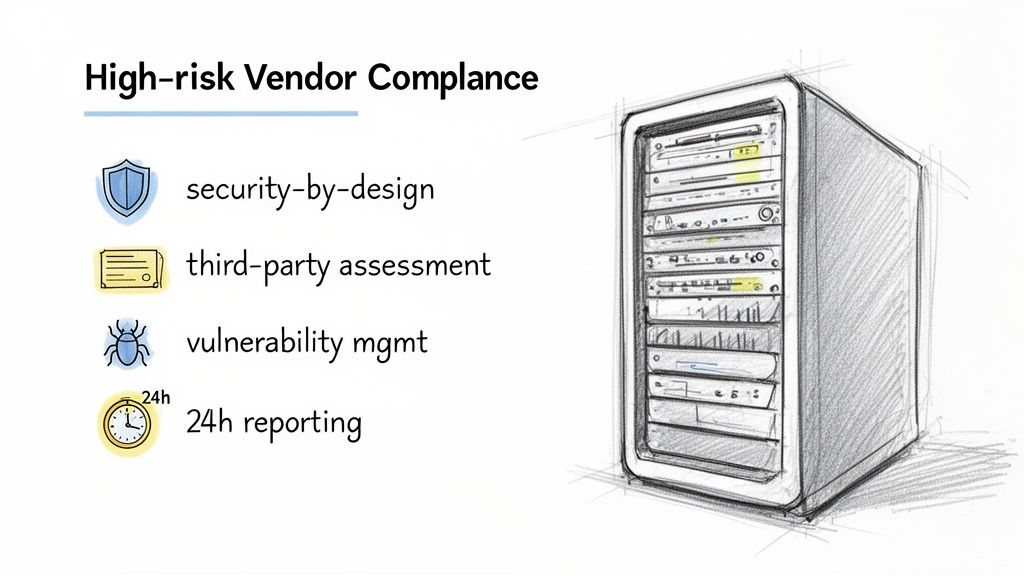
Once your product lands in a high-risk category under the Cyber Resilience Act, your compliance journey isn't just about ticking boxes anymore. It’s a mandatory set of actions you must complete before your product can even touch the EU market. The EU CRA revamp targets high risk vendors with a very specific list of duties, all designed to make sure these critical products are secure from day one and stay that way.
Think of it like the pre-flight checks a pilot runs. Every single step is non-negotiable and has to be documented because getting it wrong has serious consequences. For high-risk products, these checks go way beyond a simple self-assessment, pushing you into a world of third-party verification and constant oversight.
This is the new reality. It demands a structured, operational approach to meet your responsibilities head-on.
Mandatory Third-Party Conformity Assessments
The biggest shift for high-risk vendors is the mandatory third-party conformity assessment. If your product is in Critical Class I and you're not following harmonised standards, or if it's in Critical Class II at all, you can no longer just declare compliance yourself.
Instead, you’ll have to bring in a Notified Body. This is an independent organisation, officially designated by an EU country, to audit your product before it hits the market. They will put your product's security, its documentation, and your internal processes under a microscope to confirm you meet the CRA's strict criteria. For instance, a German manufacturer of industrial robots (Class II) would need to have its products audited by an organization like TÜV or DEKRA before they could be legally sold anywhere in the EU.
This step fundamentally changes the game. It introduces an impartial layer of scrutiny, making sure the most critical digital products have been properly vetted by an expert third party.
The 24-Hour Vulnerability Reporting Rule
One of the most pressing new duties is the vulnerability reporting mandate. If you discover a vulnerability in your product that is being actively exploited, you have just 24 hours to report it to ENISA, the European Union Agency for Cybersecurity.
That's an incredibly tight deadline. It means your internal incident response process needs to be lightning-fast and ruthlessly efficient. Your team has to be able to spot, validate, and escalate reports of active exploits almost immediately to stay on the right side of the law. This rule is all about giving EU authorities a real-time view of emerging threats so they can coordinate a response across member states.
The CRA's 24-hour reporting rule is a massive change for incident response. It drags vulnerability disclosure out of the shadows of a voluntary, often slow, process and turns it into a hard legal deadline with immediate consequences.
Having a clear communication plan and people ready to act at a moment's notice is no longer just good practice—it's the law.
Robust Vulnerability Management Protocols
Beyond that 24-hour rule, the CRA demands that high-risk vendors run a robust vulnerability management system. This is about more than just reporting. It means you must have a clear, public policy for coordinated vulnerability disclosure.
This policy needs to give security researchers a secure and straightforward way to tell you about flaws they find. More importantly, you are now legally required to act on those reports by developing and shipping security patches without delay. For example, your website must have a dedicated /security page with contact details and a PGP key for encrypted communication, outlining how you will respond to and patch valid bug reports. The days of ignoring or slow-rolling vulnerability reports are officially over.
For a complete breakdown of all these duties, check out our guide covering CRA manufacturer obligations, which dives deeper into what’s expected.
A Practical Example: A Firewall Manufacturer's Journey
To see how this all fits together, let’s imagine a company called "SecureNet" that makes a 'Class I' network firewall.
- Security-by-Design: Right from the start, SecureNet's engineers build security controls directly into the firewall's architecture. They use threat modelling to figure out how attackers might try to break it and build in defences from the ground up.
- Engaging a Notified Body: Six months before launch, SecureNet packages up its firewall, technical documents, and risk assessments and sends them to an accredited Notified Body for the third-party assessment.
- Coordinated Disclosure Policy: SecureNet posts a clear vulnerability disclosure policy on its website, complete with a dedicated, encrypted email for researchers to send in their findings.
- Post-Market Surveillance: After launch, SecureNet’s security team keeps a close watch for new threats. They use threat intelligence feeds and maintain a Software Bill of Materials (SBOM) to track every component in their software.
- Incident Response: A researcher reports a critical vulnerability. SecureNet’s incident response plan kicks in. The team validates the issue and develops a patch within a week. Because it wasn't being actively exploited, they don't have to make the 24-hour call to ENISA, but they do issue a security advisory and push the patch to all customers through a secure update channel.
This example shows how the CRA's rules translate into a continuous cycle of design, assessment, monitoring, and response—the new operational standard for every high-risk vendor in the EU.
Why Connected Toys Are a Prime Example Of High-Risk
Theory is one thing, but to really grasp how the Cyber Resilience Act will play out, we need a real-world example. It helps to see how regulators are thinking on the ground. For that, connected toys offer the perfect case study, embodying exactly what the EU CRA revamp targets high risk vendors with.
These aren't your grandparents' playthings; they're complex digital products. Most connect to the internet, are managed via mobile apps, and frequently collect sensitive data like audio recordings, photos, or location info. Because the end-users are children—a legally defined vulnerable group—the potential for harm from a security breach is massively amplified. This puts these products squarely in the regulatory spotlight.
This combination of factors—handling personal data and serving a vulnerable user base—makes connected toys a textbook example of a product that demands much tougher security scrutiny. It’s no surprise that national bodies are already getting ahead of the curve, setting a clear precedent for how the CRA will be enforced across the EU.
Spain’s Proactive Stance On Toy Cybersecurity
Regulators aren't sitting on their hands waiting for the 2027 deadline. Spain, for instance, is already taking the lead in applying the CRA's principles. Its National Institute for Cybersecurity (INCIBE) has launched the first-ever comprehensive security analysis of connected toys, showing a remarkably forward-thinking approach to the new rules.
This landmark report, presented on 17 December 2024, dives into the vulnerabilities of toys with digital components. It’s a clear signal that member states are already identifying product categories they consider high-risk and are building the skills to assess them, even during the CRA's transition period. You can find more details on this pioneering cybersecurity analysis on lamoncloa.gob.es.
This initiative sends a powerful message to the market. National authorities aren't just waiting for top-down instructions from the EU; they are actively interpreting the spirit of the CRA and applying it to products that pose an obvious risk to their citizens.
The proactive analysis of connected toys is more than just a report; it's a warning shot. It tells every vendor of consumer IoT devices that the era of lax security is over and that regulators are already building their enforcement capabilities.
But this story isn't just about toys. It’s a critical heads-up for vendors in many other sectors making products with a similar risk profile.
Broader Implications For Other High-Risk Sectors
The lessons from the connected toys example reach far beyond the playroom. Any manufacturer making products with similar characteristics should be paying very close attention. If your product connects to a network, collects user data, and is used in a sensitive environment, you are officially on the regulatory radar.
Think about these parallel sectors:
- Smart Home Devices: Products like security cameras, smart locks, and voice assistants are embedded in our most private spaces. A vulnerability in a smart door lock could lead to a physical break-in, while a compromised baby monitor could result in an intimate privacy violation.
- Wearables and Health Tech: Devices that track fitness, sleep, or even medical data like heart rate and glucose levels handle incredibly sensitive personal information. The fallout from a data breach of a connected insulin pump, for example, is severe.
- Educational Technology: Tools and devices used by children for learning carry almost identical risks to connected toys, often processing data on minors' progress and behaviour. An app that tracks a child’s location for school bus monitoring is a prime example of a high-risk educational product.
The move by INCIBE reveals a clear pattern. Regulators will go after products where a cyber incident could cause the most direct harm to individuals, especially vulnerable ones. This proactive enforcement model is almost certain to be copied across the EU for other high-risk product categories.
For manufacturers, the takeaway is urgent and unambiguous. You cannot afford to wait until the deadline is looming. The time to assess your products, understand your obligations as a potential high-risk vendor, and start building a robust compliance strategy is right now.
Navigating The Digital Supply Chain Responsibilities
The Cyber Resilience Act's rules don't just stop at the factory door. They send a powerful ripple effect across the entire digital supply chain, fundamentally changing the game for anyone bringing connected products into Europe. While manufacturers of high-risk products carry the main burden, the EU CRA revamp targets high-risk vendors by turning importers and distributors into the new gatekeepers of the EU market.
Think of it this way: they're no longer just moving boxes. They're now the front-line quality inspectors on a digital production line. Their new legal duty is to be the first line of defence, ensuring that any product entering the EU is secure and compliant before it ever reaches a customer.
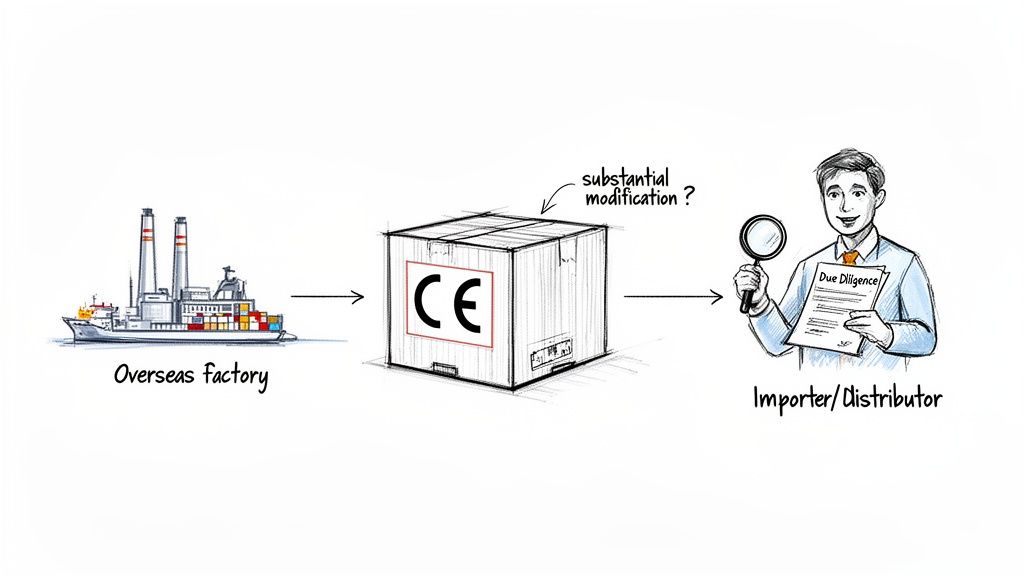
This shift adds a crucial layer of accountability, placing clear, non-negotiable obligations on every single entity that introduces a product with digital elements to the Union.
The Gatekeeper’s Due Diligence Checklist
For importers and distributors, the core mandate is due diligence. It's not a suggestion; it’s a legal requirement. Before putting any product on the market, they must verify that the original manufacturer has done their homework correctly.
Their verification checklist has to confirm that:
- The product carries the CE marking, signalling it conforms with EU law.
- The manufacturer has drawn up an EU Declaration of Conformity.
- All the necessary technical documentation is present and correct, including user instructions and security information.
- Both the product and the manufacturer can be clearly identified with contact details.
If an importer or distributor even suspects a product doesn’t meet the CRA’s essential cybersecurity requirements, they are legally forbidden from selling it. Instead, they must immediately inform the manufacturer and the relevant market surveillance authorities.
When Modification Transfers Full Responsibility
The CRA also brings in another critical concept: substantial modification. If an importer or distributor makes a significant change to a product that could affect its cybersecurity compliance, the law treats them as if they were the original manufacturer.
A substantial modification isn't just slapping on a new brand name. It's any change that alters the product's original purpose, performance, or safety features, potentially creating new vulnerabilities. For example, if an importer takes a generic smart camera and integrates it into their own proprietary cloud storage system, that’s a substantial modification. When this line is crossed, the full weight of CRA compliance—from risk assessments to 24-hour incident reporting—lands squarely on the shoulders of whoever made the change.
This rule is designed to stop companies from importing a non-compliant product, making a few tweaks, and then pleading ignorance. If you modify it, you own its security. It’s that simple.
Practical Example: Importer Due Diligence
Let’s walk through a realistic scenario. An EU-based company, "EuroImports," wants to bring in a new line of smart home security cameras from a non-EU manufacturer. Given their function, these cameras will almost certainly fall into a high-risk category.
Before any contracts are signed, EuroImports must conduct rigorous due diligence. This means asking the manufacturer some very pointed questions:
- Conformity Assessment: "Can you provide the certificate from the Notified Body that assessed this product as a Critical Class device?"
- Vulnerability Management: "What is your public vulnerability disclosure policy? How do you guarantee security updates for the product's five-year expected lifecycle?"
- Documentation: "We require a complete Software Bill of Materials (SBOM) for the camera’s firmware to verify all open-source components." You can learn more about these requirements in our guide covering CRA SBOM requirements.
- Reporting Protocol: "How will you notify us within 12 hours of discovering an actively exploited vulnerability, so we can meet our 24-hour reporting duty to ENISA?"
This level of scrutiny is particularly vital in sectors like finance, where the integrity of the supply chain is non-negotiable. For instance, recent findings in Spain's financial sector underscore the intense focus on third-party provider risks, pushing national bodies to identify critical vendors and mitigate concentration risks. You can discover more insights about how Spain is enhancing its financial cyber resilience on fsb.org.
By asking these tough questions upfront, EuroImports doesn't just tick a compliance box. It protects itself from huge financial and legal liabilities down the road.
Your Step-by-Step Roadmap to CRA Compliance
Moving from simply understanding the Cyber Resilience Act to actually preparing for it requires a solid plan. It's easy to feel overwhelmed, but the best approach is to break it down into a series of manageable stages. This roadmap turns a complex set of legal requirements into a clear, actionable project your team can get behind.
The goal here is to methodically build up your compliance posture, making sure every requirement is ticked off long before the 2027 deadline hits. This proactive mindset is crucial, especially since the EU CRA revamp targets high risk vendors with such detailed scrutiny. It’s all about turning uncertainty into confident preparation.
Step 1: Conduct an Applicability Assessment
First things first: does the CRA even apply to your products? The regulation is incredibly broad, covering just about all "products with digital elements" placed on the EU market, from software applications to connected hardware.
Your initial move should be to inventory every single product you sell in the EU and figure out if it falls within this scope. This isn't always a simple yes/no question, which is where tools like the Regulus platform can help by guiding you through a structured assessment for each item in your portfolio. A practical example is a medical device manufacturer in the US reviewing its portfolio to identify which of its connected pacemakers and glucose monitors sold in Germany and France fall under the CRA's scope.
Step 2: Classify Your Product Portfolio
Once you know which products are covered, the next critical step is classification. As we’ve seen, the CRA isn’t one-size-fits-all. It uses a tiered system: Default, Critical Class I, or Critical Class II. This classification is what dictates the intensity of your obligations.
Getting this wrong can be seriously costly. You could end up over-investing in compliance for a low-risk product or, even worse, failing an audit for a high-risk one. You need to carefully evaluate each product against the specific criteria laid out in the CRA’s Annexes to land it in the right category.
A critical component of any step-by-step roadmap to CRA compliance involves efficient handling of all related documentation. To ensure smooth operations, adopting document management best practices is essential for organising assessments, technical files, and declarations of conformity.
Step 3: Perform a Gap Analysis and Implementation
With your products neatly classified, you can now map out your specific obligations and see where your current processes fall short. This gap analysis is the heart and soul of your implementation plan.
Your roadmap from here should break down into a few key actions:
- Requirement Mapping: For each product class, generate a complete list of your duties—covering security, documentation, and vulnerability management.
- Process Review: Hold up a mirror to your existing development lifecycle, incident response plans, and documentation practices. For example, review your software development lifecycle (SDLC) to see if it includes mandatory security checkpoints like static code analysis and penetration testing.
- Action Plan: Create a detailed project plan to close every gap you've found. Assign owners, set deadlines, and make it happen.
- Post-Market Processes: This isn't a one-and-done exercise. You need to establish robust systems for ongoing vulnerability monitoring, secure updates, and the mandatory 24-hour reporting of exploited vulnerabilities to ENISA.
Following a structured approach like this ensures nothing gets missed. It transforms a daunting regulation into a concrete checklist your team can execute with confidence.
Cyber Resilience Act – FAQs
Got questions about the Cyber Resilience Act? You’re not alone. This section tackles some of the most common queries we hear from manufacturers and product teams, giving you clear, practical answers.
How Does The CRA Affect Open-Source Software?
This is a big one, and the CRA makes a critical distinction. Purely non-commercial, unpaid open-source development is generally exempt. This is great news, as it protects the collaborative spirit that makes the open-source community thrive.
However, the moment you integrate that software into a commercial product, the game changes. The manufacturer of the final product—the one you sell—becomes fully responsible for its compliance. So, if your team uses a free open-source library like Log4j in a smart thermostat you're bringing to market, you are on the hook for ensuring the entire product, including that library, meets all CRA security and vulnerability management standards.
What Are The Penalties For Not Complying?
The financial penalties are severe, and they're designed to make sure businesses take these obligations seriously. The EU's CRA revamp targets high-risk vendors with fines hefty enough to make non-compliance a massive business risk.
- For serious non-compliance: Fines can climb as high as €15 million or 2.5% of your company's total worldwide annual turnover from the previous year, whichever is higher.
- For other obligations: You could be looking at fines up to €10 million or 2% of global annual turnover.
- For supplying false information: Don't even think about it. Providing incorrect or misleading information to authorities can cost you up to €5 million or 1% of global annual turnover.
And it doesn't stop at fines. Authorities also have the power to order product recalls or completely ban a non-compliant product from the entire EU market. For example, a national authority in France could force a company to recall every unit of its non-compliant smart security cameras from shelves across all 27 EU member states.
How Does The CRA Interact With GDPR And DORA?
The CRA doesn’t operate in a silo. Think of it as one crucial layer in the EU's broader digital security framework, working hand-in-hand with regulations like GDPR and the Digital Operational Resilience Act (DORA).
The CRA sets the baseline security for the product itself. GDPR protects the personal data processed by that product. And DORA secures the operational resilience of financial entities using it.
Here’s a practical example: a smart health watch must be secure by design under the CRA. That built-in security directly helps the manufacturer meet their GDPR obligation to protect the sensitive health data the watch collects. If a bank uses a software product that falls under the CRA, that product's compliance helps the bank satisfy its own DORA requirements for third-party risk management. They all fit together.
Navigating the complexities of the CRA shouldn't feel like a struggle. Regulus provides a clear, step-by-step platform to assess applicability, classify your products, and generate a tailored compliance roadmap. You can finally move beyond spreadsheets and gain the confidence to place your products on the EU market. Find out how Regulus can help.