A no root firewall acts as a dedicated security guard for individual applications, controlling their internet access without needing the ‘master keys’ to the entire system (root privileges). This is a major shift away from traditional firewalls that demand deep system integration, offering a far more contained and secure way to manage network traffic—especially for modern connected devices.

Understanding the No Root Firewall
Before we get into the specifics of ‘no root’ implementations, it’s worth remembering the crucial role of a firewall in any security strategy. A traditional firewall guards the whole network or operating system, but a no root firewall operates on a completely different principle.
Think of it as assigning a personal bouncer to every single app on your device.
Instead of needing the master key to control every door in the building (the operating system), this bouncer only manages who comes and goes through its assigned door (one application). It doesn’t have—or need—permission to go anywhere else. For example, a weather widget app on an embedded device can be restricted by a no root firewall to only connect to weather.api.com, preventing it from accessing any other part of the internet, even if the app itself is compromised.
Why This Matters for Security
This approach brings some huge advantages, especially for the Internet of Things (IoT) and embedded systems, where minimising privileges is a core security principle. By not asking for root access, you dramatically shrink the potential damage if one of your applications gets compromised.
A no root firewall is foundational to implementing ‘security by design’. It ensures that even if one component is breached, the attacker cannot easily move across the system, containing the threat at the application level.
This kind of containment is exactly what’s needed to meet the strict requirements of regulations like the EU’s Cyber Resilience Act (CRA). You can find out more about how open-source solutions fit into this model in our guide on firewalls and open-source for CRA compliance.
Real-World Application Examples
To make this concept more concrete, let’s look at a couple of practical scenarios:
- Smart Thermostat: An attacker finds a vulnerability in the thermostat’s weather update feature. With a no root firewall, you can build a rule allowing that specific app to only talk to the official weather service server. Any attempt to connect to a malicious server would be blocked on the spot, even with the app itself compromised.
- Android Kiosk: Imagine a public-facing tablet in a retail store that only needs to access the company’s inventory website. A no root firewall can be configured to block all other network activity, preventing users from browsing other sites or accidentally downloading malware.
- Industrial IoT Sensor: A sensor in a factory needs to send temperature data to a specific internal server at
192.168.1.100. A no root firewall rule ensures the sensor’s application can only establish a connection to that IP address and port, blocking any attempt to communicate with the wider internet or other devices on the local network.
The table below summarises the core principles that distinguish the no root firewall from its traditional, root-based counterpart.
No Root Firewall Core Principles at a Glance
| Aspect | Traditional (Root) Firewall | No Root Firewall |
|---|---|---|
| Privileges | Requires highest system access (root) | Runs with standard user permissions, no root needed |
| Scope | Manages traffic for the entire system | Manages traffic on a per-application basis |
| Attack Surface | Larger; a breach can compromise the system | Smaller; a breach is contained within the app |
| Typical Use Case | Securing network perimeters or servers | Securing apps on IoT, mobile, and embedded devices |
As you can see, the no root firewall approach isn’t just a minor tweak—it’s a fundamentally different way of thinking about application security, one that prioritises containment and least privilege from the ground up.
Meeting CRA Compliance with a No Root Firewall
The EU’s Cyber Resilience Act (CRA) is forcing a fundamental rethink of security for any product with digital elements sold in the European market. For manufacturers, achieving compliance isn’t about adding a security feature at the last minute; it’s about embedding security deep into a product’s DNA. A no root firewall is one of the most effective tools for this job, directly supporting core CRA principles like ‘security by design’ and ‘privilege minimisation’.

Instead of relying on powerful, system-wide permissions that create a massive attack surface, this technology operates with the lowest possible privilege. This design choice is critical because it inherently limits the blast radius of a security breach—a key expectation under the CRA.
Applying No Root Principles to CRA Requirements
Let’s look at a practical example: a smart thermostat. An attacker finds a flaw in a third-party library it uses to display the weather. With a no root firewall in place, the application process running that feature is strictly confined to communicating with its approved weather service API. Nothing else.
Even if the component is fully compromised, it can’t phone home to a malicious command-and-control server. It can’t pivot to other devices on the local network. This containment is precisely what regulators want to see for meeting the CRA’s strict vulnerability management obligations.
By containing a threat at the application level, you prevent a localised flaw from becoming a system-wide breach. This significantly simplifies incident response and makes meeting the CRA’s 24-hour vulnerability reporting deadline more manageable.
This approach transforms a potential catastrophe into a contained, reportable incident. It’s a proactive measure that demonstrates a clear commitment to security throughout the product lifecycle. This fits directly into your overall strategy, which you can map out by completing a CRA risk assessment.
A Strategic Choice for EU Market Access
Adopting a no root firewall isn’t just a technical decision; it’s a vital business strategy for accessing the EU market. The CRA mandates that all products with digital elements undergo rigorous conformity assessments. A huge number of connected devices currently lack these fundamental protections, creating a massive compliance gap for manufacturers.
Here’s how a no root firewall directly addresses key CRA articles:
- Secure by Default Configuration: You can ship your device with firewall rules that enforce the most secure state right out of the box, allowing only essential network connections and blocking everything else. For example, a smart plug might ship with rules that only permit connections to the manufacturer’s update and control servers.
- Vulnerability Handling: When a vulnerability is discovered, you can deploy a new firewall rule as a rapid virtual patch. For instance, if a flaw is found in an authentication service, you can push a rule that temporarily blocks all traffic to that service’s port until a full firmware fix is ready.
- Technical Documentation: The architecture, ruleset, and logic of your no root firewall become powerful evidence in your Annex VII technical documentation, proving you have implemented appropriate and effective security measures.
For an industrial sensor in a factory, this means you can prove to regulators that a device designed only to send temperature data to an internal server is physically incapable of doing anything else. This kind of documented, verifiable control is precisely what the CRA demands, helping you avoid fines and secure your place in the European market.
Practical Ways to Implement a No Root Firewall
Understanding the theory behind a no root firewall is one thing, but building a robust one is another challenge entirely. The good news is you don’t have to start from a blank slate. There are several well-established patterns you can adapt, each with its own strengths depending on the environment and use case.
Let’s break down the four most common methods you’ll encounter in practice.
1. VPN-Based Interception
On mobile platforms like Android, the most popular technique is to use a local VPN service. Don’t think of this as a traditional VPN that tunnels your traffic to a remote server. Instead, it’s more like an internal redirection system. The firewall application itself creates a local VPN interface right on the device.
Because the operating system sees this local VPN as the designated network gateway, it routes all outbound and inbound traffic through it. This gives the application a central point to inspect, filter, and block any connection based on its ruleset—all without needing root privileges. It’s a clever workaround to gain system-wide traffic control.
Practical Example:
Imagine an Android-based kiosk in a retail store. It needs to be locked down to a single app that communicates only with the company’s inventory server. By using a VPN-based no root firewall, developers ensure the device can only talk to that specific server. Any attempt by the app to access other websites is simply dropped by the local VPN filter. This is the exact method popular apps like NetGuard use.
2. User-Space Packet Filtering
This approach moves the firewall logic directly into the application’s own process, operating in what’s known as user-space. Instead of trying to hook into the kernel (which always requires root), the application intercepts its own network data packets before handing them off to the operating system.
It inspects every packet’s destination, port, and content within its own memory. If a packet matches the security rules, it’s allowed to go out. If not, it’s discarded on the spot.
This method gives you incredibly granular control over an application’s specific network behaviour. It’s like having a dedicated security inspector stationed right on your application’s loading dock, checking every single package before it leaves.
Practical Example:
An embedded medical device runs a custom application to transmit patient data to a hospital’s server. The developers can build user-space filtering directly into the application code. This logic would inspect every outgoing packet to ensure its destination is the hospital server’s IP address and the port is the correct one for secure transmission (e.g., port 443). Any packet destined for another address is dropped internally.
3. Application-Level Proxying
Another highly effective method involves forcing an application’s traffic through a local proxy server. Here, you configure the application—either directly in its code or through device settings—to send all its network requests to a proxy running on the same device (localhost).
This local proxy then becomes the middleman. It receives each request, inspects it against the security policy, and then decides whether to forward it to the real destination, modify it, or block it completely. This technique is particularly robust for filtering web traffic like HTTP and HTTPS.
Practical Example:
A smart home hub aggregates data from various sensors before sending it to a cloud platform. To prevent potential data leaks, its main application could be hard-coded to use a local proxy. This proxy is then configured with a whitelist of allowed domains (e.g., api.smarthome.com), effectively blocking any attempt to exfiltrate data to an unauthorised server.
4. Advanced Linux Techniques with eBPF
For modern Linux-based embedded systems, the extended Berkeley Packet Filter (eBPF) offers a far more sophisticated way to implement a no root firewall. eBPF is a game-changer because it allows developers to run sandboxed programmes inside the Linux kernel itself, but without having to change the kernel source code or load risky kernel modules.
By using a combination of user namespaces and specific eBPF programme types, a non-root process can attach its filtering logic directly to network sockets. This delivers the performance of kernel-level packet inspection without granting the dangerous, all-access privileges of root, blending high efficiency with strong security.
The table below summarises these four implementation patterns, outlining how they work and where they fit best.
Comparison of No Root Firewall Implementation Methods
| Implementation Method | How It Works | Best For | Key Trade-Off |
|---|---|---|---|
| VPN-Based Interception | Creates a local VPN on the device to intercept all system-wide traffic for filtering. | Mobile platforms (Android) and devices where system-wide control is needed. | Can be complex to manage battery life and potential conflicts with other VPN apps. |
| User-Space Filtering | The application inspects its own network packets in its own memory space before sending them to the OS. | Single-purpose applications and embedded systems with full source code access. | Requires deep integration into the application code; only controls the app it's built into. |
| Application Proxying | Forcing all application traffic through a local proxy (localhost) that inspects and forwards or blocks requests. |
Filtering web (HTTP/S) traffic and securing applications with configurable network settings. | May not capture all traffic types (e.g., raw UDP packets) unless the app is specifically designed for it. |
| eBPF & User Namespaces | Attaching sandboxed filtering programmes directly to network sockets in the kernel from an unprivileged user-space process. | Modern Linux-based embedded systems requiring high performance and low latency. | Requires a recent Linux kernel (4.x or newer) and specialised developer knowledge of eBPF. |
Each of these methods offers a legitimate path to building a firewall without root access, but choosing the right one depends entirely on your platform, performance needs, and how much control you have over the application code itself.
Analysing the Security and Performance Trade-Offs
Opting for a no root firewall brings major security advantages, but like any architectural choice, it involves a careful balancing act. Understanding these trade-offs is essential for making an informed decision that suits your device’s specific purpose and operating environment.
The biggest win is a drastically reduced attack surface. By running without root privileges, these firewalls stick to the principle of least privilege. If an application is compromised, the damage is contained within its own sandbox, stopping an attacker from getting system-wide control. This containment strategy is a powerful part of a modern security posture.
But this approach isn’t a silver bullet. Because a no root firewall operates in user-space, it has limitations. Sophisticated malware built specifically to evade these kinds of filters could potentially slip past its defences, especially if it can exploit low-level kernel vulnerabilities and operate underneath the firewall’s line of sight.
This diagram shows the common implementation methods we’ve touched on, each with its own set of trade-offs to consider.
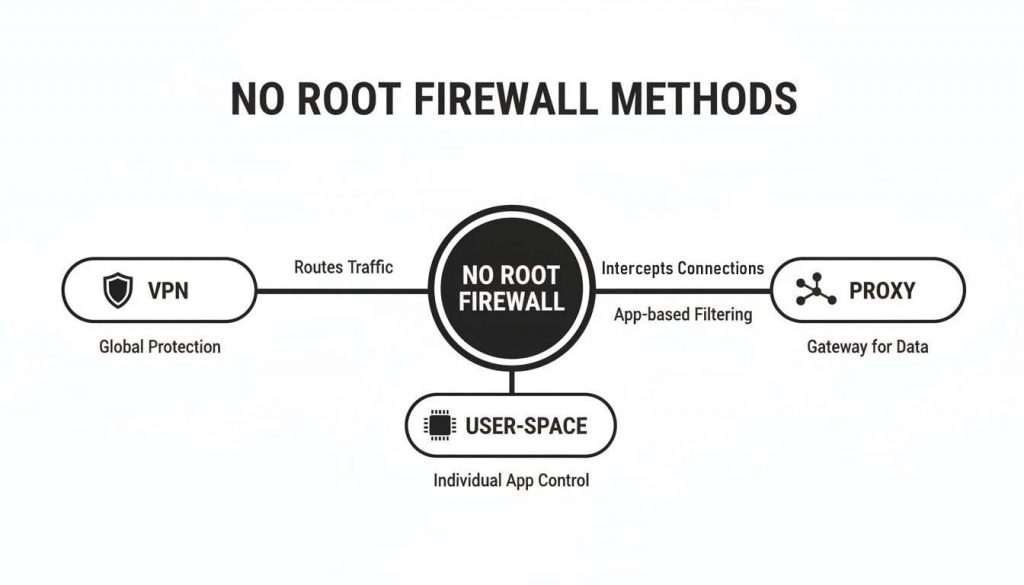
As the visualisation shows, methods like VPN interception offer broad, device-wide coverage. In contrast, user-space and proxy techniques provide more granular, application-specific control, highlighting the need to match the method to your security goals.
Balancing Performance and Power Consumption
Performance impact is another critical factor. Will running a local VPN service 24/7 drain the battery on a mobile device? Does user-space packet filtering add latency that bogs down an IoT gateway? The answer really depends on the implementation and the hardware it’s running on.
Think about a battery-powered environmental sensor that only wakes up to send a tiny data packet once an hour. A device like that will be highly sensitive to any persistent background process. Here, a lightweight user-space filtering method built directly into the application might be the best choice.
On the other hand, a mains-powered smart hub that constantly processes data from multiple sources can easily absorb the overhead of a local VPN or proxy service. The key is to measure the impact.
The goal isn’t to eliminate all performance overhead, but to find an acceptable balance. A 1-2% increase in battery drain might be a worthy price for blocking 100% of unauthorised connections.
Mitigating Performance Hits
You can take practical steps to measure and mitigate these performance impacts. Profiling tools can help you analyse CPU usage and battery consumption before and after you implement the firewall.
Consider these strategies:
- Optimise Rule Sets: Keep your firewall rules as simple and efficient as possible. Complex regular expressions or overly broad rules can increase the processing time for every single packet. For example, instead of a rule that filters based on a complex URL path, use a simple rule that blocks or allows an entire domain.
- Use Efficient Methods: For high-throughput devices running modern Linux kernels, eBPF offers near-native performance that is significantly more efficient than traditional user-space proxying.
- Batch Connections: If your application design allows for it, batch data and send it in bursts rather than maintaining a constant connection. This reduces the firewall’s active processing time. For example, an IoT sensor could collect readings for an hour and send them all in one short connection, minimizing the time the firewall needs to be actively inspecting traffic.
The urgency for these solutions is undeniable. Historical data reveals a startling 92% rise in root-level breaches in the EU region between 2022 and 2025, with a massive 68% of those incidents tied to firmware that lacked a no root firewall. As regulations like the Cyber Resilience Act (CRA) come into force, proving you have these protections in place is no longer a choice. You can find out more about how these developments impact EU market access by reading the latest research on the European Cyber Resilience Act.
How to Test and Harden Your Firewall Implementation
Building a no root firewall is just the start. The real work is ensuring it stays robust and secure over its entire lifecycle. This isn’t just good practice—it’s a critical part of meeting ongoing obligations under regulations like the EU’s Cyber Resilience Act (CRA).
A firewall that hasn’t been deliberately attacked is a firewall you can’t trust. This is where you have to put on your attacker hat and actively try to break what you’ve built.

Penetration testing for a no root firewall isn’t about just checking if rules block known bad traffic. It’s about getting creative. You need to craft non-standard or even malformed data packets to see if they can slip past your filters and hit their target.
Here’s a practical example. Imagine your IoT device is only supposed to talk to api.yourcompany.com. A good test is to try sending a DNS query for a completely forbidden domain from the application. If that query gets any kind of response, you’ve found a leak in your firewall. Another test would be to try connecting to the allowed domain but on an unapproved port (e.g., port 22 for SSH) to ensure the rule is specific enough.
This kind of proactive testing is absolutely vital. A stark statistic from recent EU cybersecurity audits revealed that 65% of IoT incidents in the ES region between 2023-2025 stemmed from bypassed no root firewalls, where attackers escalated privileges without being detected. This is precisely why the CRA puts such a heavy emphasis on proven security.
Hardening Your No Root Firewall
Hardening goes a step further than testing. It’s about fortifying the firewall against tampering and ensuring it remains reliable in the field. The best place to start is with a secure-by-default configuration.
This means your firewall rules must block everything except the absolute minimum connections needed for the application to do its job. Anything else is explicitly denied, no exceptions.
Your default policy should be “deny all, permit by exception.” This simple principle is one of the most effective security postures you can adopt, making it much harder for unexpected behaviour to go unnoticed.
You should also implement integrity checks. These are mechanisms that periodically verify that the firewall’s configuration files—or even the application binary itself—haven’t been modified by an unauthorised process. A practical example is to store a cryptographic hash (like SHA-256) of the firewall ruleset in a secure, read-only location. At startup, the device recalculates the hash of the current ruleset and compares it to the stored value to detect tampering.
Key Hardening and Testing Techniques
To build a truly resilient no root firewall, you need to bake security practices directly into your development and maintenance cycles. Here’s what that looks like in practice:
- Static and Dynamic Code Analysis: Before you even deploy, run automated tools to scan your firewall’s source code. These tools are great at catching common programming errors and potential security flaws early.
- Network Traffic Monitoring: Use monitoring tools to keep a close eye on the traffic leaving your device. This is how you verify that the only connections being made are the ones you’ve explicitly allowed in your ruleset.
- Fuzz Testing: This technique involves bombarding your firewall with random, malformed data. The goal is to trigger a crash or an unexpected state that an attacker could potentially exploit to bypass your rules.
For ensuring the long-term effectiveness and security of your firewall, adopting a robust approach like the Secure Software Development Lifecycle is key. You may also find our detailed OWASP testing guide useful for structuring your security assessments.
Frequently Asked Questions About No Root Firewalls
As with any security control, practical questions always come up during implementation. Let’s tackle some of the most common ones we hear from teams working with no root firewalls in their products.
Can a No Root Firewall Block Everything?
A no root firewall is exceptionally good at application-level containment. It gives you precise control over which network connections an individual application can make. For instance, you could configure it so a smart camera’s software can only talk to your company’s secure cloud server, and nothing else.
But that strength is also its boundary. Because it operates within the user-space, it can’t see or block traffic generated at a much lower level, like from the operating system kernel. It’s most powerful when used as one layer in a wider security strategy, not as a single solution.
Think of a no root firewall as a powerful tool for application containment. It isn’t a replacement for every other security measure, but it’s a vital layer that dramatically shrinks the attack surface on the device itself.
Is a Network Firewall Still Necessary?
Yes, absolutely. A traditional network firewall is still a critical part of your defence. The two firewall types serve different, complementary roles. They work together to create a much stronger security posture.
Imagine your security setup like this:
- Network Firewall: This is your building’s perimeter security. It sits at the edge of your local network, protecting everything inside from external threats coming from the internet. A practical example is blocking incoming connections on all ports except those needed for your VPN or web server.
- No Root Firewall: This is the dedicated security guard assigned to a specific room inside the building. It polices what one application on one device is allowed to do, preventing it from causing trouble if it ever gets compromised.
So, your network firewall might block suspicious traffic from ever reaching your office network, while the no root firewall on an IoT device stops its firmware update client from connecting to anything except your official update server.
How Do I Document This for the CRA?
For Cyber Resilience Act (CRA) compliance, clear documentation isn’t just good practice—it’s mandatory. Your technical file must prove you have implemented effective and justified security measures.
For a no root firewall, this means you need to document:
- Design Architecture: Provide a diagram and clear description showing how the firewall is integrated into your product’s architecture.
- Implementation Pattern: You must specify the technical approach you chose, such as VPN-based interception or user-space packet filtering.
- Rule Sets: Document the specific rules you have configured. For example, provide a table listing each application, its permitted domains/IPs, and the justification for that access. Critically, you need to show you are following a “deny-all, permit-by-exception” policy.
- Testing Results: Include evidence from penetration tests, code reviews, and operational monitoring that proves the firewall effectively blocks unauthorised traffic as designed. This could include logs from a test where the firewall successfully blocked an attempt to connect to a forbidden IP address.
Preparing for the Cyber Resilience Act requires more than just technical implementation; it demands structured documentation and a clear compliance strategy. Regulus provides a complete platform to assess your obligations, map requirements, and generate the necessary evidence to confidently place your products on the EU market. Learn how Regulus can simplify your CRA compliance journey.