Harmonised standards under the Cyber Resilience Act (CRA) are your most direct, pre-approved path to proving a product meets its legal requirements. Think of them as certified recipes for cybersecurity; follow a standard that’s listed in the Official Journal of the European Union, and you gain a legal “presumption of conformity.” This single benefit can dramatically simplify your entire compliance journey.
Understanding CRA Harmonised Standards and Why They Matter
Imagine the Cyber Resilience Act is a destination you must reach to place your products on the EU market. Harmonised standards are the official, EU-endorsed GPS route. You could navigate on your own with a custom map, but following the pre-approved route guarantees you’ll arrive with far less friction from regulators.
These standards are highly detailed technical documents drafted by European Standardisation Organisations (ESOs) like CEN and CENELEC. Their whole purpose is to translate the high-level legal obligations in the CRA’s Annex I into concrete, actionable engineering tasks that your development teams can actually implement.
Bridging Legal Requirements and Technical Implementation
The CRA’s essential requirements are written in broad legal terms by design. For instance, Annex I requires products to “protect the integrity of stored, transmitted or otherwise processed data… against any manipulation or modification not authorised by the user.” This is clear in its goal, but leaves manufacturers wondering how to achieve it in practice.
This is precisely where a harmonised standard cuts through the fog. Instead of your team endlessly debating whether a simple checksum is sufficient, a relevant standard might specify the exact cryptographic hashing algorithm (like SHA-256) and implementation methods needed to meet that integrity requirement.
A harmonised standard acts as a bridge between a legal obligation and an engineering task. It removes the ambiguity from compliance, giving you a clear, defensible, and repeatable method for meeting the CRA’s security objectives.
This approach gives manufacturers several powerful advantages:
- Legal Certainty: Applying a harmonised standard gives you a presumption of conformity. This means market surveillance authorities will assume your product meets the corresponding CRA requirements, shifting the burden of proof.
- Reduced Guesswork: Your teams get a clear technical checklist. This stops them from wasting time interpreting vague legal text and lets them focus on building secure products.
- Streamlined Audits: When you face a conformity assessment, pointing to the specific harmonised standards you’ve implemented is powerful evidence of due diligence. It makes the entire process faster and smoother.
A Practical Example of Using Harmonised Standards
Let’s take a smart home camera manufacturer. The CRA demands they ensure the product is secure by design and protects user data. Without clear guidance, the development team is left with a mountain of questions:
- What level of encryption is strong enough for the video stream?
- How should we deliver firmware updates securely?
- What’s the “appropriate” way to manage user credentials and prevent brute-force attacks?
A set of CRA harmonised standards would provide direct, technical answers. One standard might mandate TLS 1.3 for data in transit. Another could detail specific requirements for code-signing and secure boot processes to protect firmware updates. For instance, instead of just guessing, the standard might require a bootloader that verifies the firmware’s digital signature using an RSA-4096 key before execution. By implementing these specifications and listing them in their technical documentation, the manufacturer builds a rock-solid case for compliance.
To understand how these requirements fit into the bigger picture, our guide on the Cyber Resilience Act basics offers a foundational overview.
Ultimately, harmonised standards are much more than just technical documents. They represent your most reliable and cost-effective path to market access under the CRA, offering a structured framework that reduces risk, cost, and complexity.
The Legal Power and Official Timeline of Harmonised Standards
While following harmonised standards for the CRA is technically voluntary, it’s by far the smartest path a manufacturer can take. Aligning with them gives you a powerful legal advantage called the “presumption of conformity.” It’s a concept that acts as a legal safe harbour, dramatically simplifying your route to market.
Think of it this way: if you build your product using the EU’s own certified blueprint—the harmonised standard—market authorities assume your product meets the law’s essential requirements. You don’t have to spend time and resources proving every single security choice from scratch. This effectively shifts the burden of proof from you to anyone who might challenge your product’s compliance, a massive commercial and legal benefit.
The Cost of Choosing an Alternative Path
You can choose not to use the CRA’s harmonised standards. It’s a valid choice, but it’s a much harder road. If you go your own way with custom technical solutions, the responsibility is entirely on you to meticulously document, test, and defend how your methods provide an equivalent—or better—level of security.
This alternative path almost always involves:
- Heavier Documentation: You’ll need to write exhaustive justifications for every technical decision, explaining exactly how it satisfies the CRA’s security requirements without the shortcut of a standard.
- Intense Scrutiny: Your technical file will be put under a microscope by auditors and national surveillance authorities. Expect more questions and a tougher review process.
- Greater Legal Risk: Without the “safe harbour” of a standard, your product is far more exposed to legal challenges, which can lead to costly disputes, sales freezes, or even recalls.
Imagine you manufacture a smart thermostat and decide against using the future standard for secure updates. Instead of just referencing the standard in your documentation, your technical file must now contain a detailed analysis proving your proprietary update mechanism is just as secure. That means providing penetration test results, code reviews, and a cryptographic protocol analysis—a far more expensive and time-consuming process.
The “presumption of conformity” isn’t just legalese; it’s a tool for business efficiency. It gives your engineering and legal teams the confidence to operate, knowing their work is built on a pre-approved, defensible foundation.
The Official Standardisation Roadmap
To properly align your product development, you need to know the official timeline. The European Commission isn’t dropping all these standards at once. They’re being rolled out in phases, creating a clear roadmap that helps you plan ahead and avoid a last-minute scramble for compliance.
The EU’s standardisation work is already well underway, with key deliverables scheduled for 2026 and 2027. According to the European Commission’s plan, the first set of standards—a mix of both horizontal and product-specific ones—is expected in Q3 2026. You can review the full implementation details on the European Commission’s CRA implementation page.
Here are the key dates to watch for:
- August 2026: Release of the horizontal standard covering vulnerability handling processes.
- October 2026: First publication of “Type C” vertical standards for specific high-risk product categories.
- October 2027: Publication of the broad horizontal standard for general cybersecurity requirements.
This schedule is actionable intelligence. For instance, if you make an Industrial IoT (IIoT) device, knowing its specific standard is slated for October 2026 lets you align your R&D cycle and budget right now. Proactive planning like this is critical for navigating the complex web of CRA deadlines between 2025 and 2027. By building this timeline into your project management, you can turn a regulatory hurdle into a predictable part of your product lifecycle.
Connecting Standards to Your Security Obligations in Annex I
The Cyber Resilience Act’s legal language in Annex I needs to be translated into concrete engineering tasks. How do you actually implement the essential security requirements in your products? The key is mapping those legal obligations to specific, verifiable technical standards.
This mapping exercise is one of the most important steps in preparing for compliance. While official CRA harmonised standards are still under development, you can—and should—start now by using well-established existing frameworks as proxies. This proactive approach lets you perform a meaningful gap analysis, showing exactly where your current security practices meet expectations and where they fall short.
To effectively connect standards to your security obligations in Annex I, you’ll need a comprehensive cyber risk management framework that integrates established guidelines like the NIST frameworks and ISO 27001.
Mapping Annex I Requirements to Existing Standards
The essential requirements in Annex I are your guiding principles. They are broken down into two main parts: one focused on the product’s security properties and the other on vulnerability handling processes. Let’s look at how existing standards provide tangible solutions for these obligations.
Take the requirement that products must be “delivered without any known exploitable vulnerabilities.” This directly points to the need for a robust vulnerability management process during development. A practical example would be integrating a Software Composition Analysis (SCA) tool into your CI/CD pipeline to automatically scan for known vulnerabilities in open-source libraries before a build is released.
A standard isn’t just a document; it’s a pre-built solution to a legal problem. It provides a common language and a clear set of actions that both your engineers and auditors can understand and verify.
The standardisation process provides the bridge between EU policy and a manufacturer’s ability to demonstrate compliance effectively.
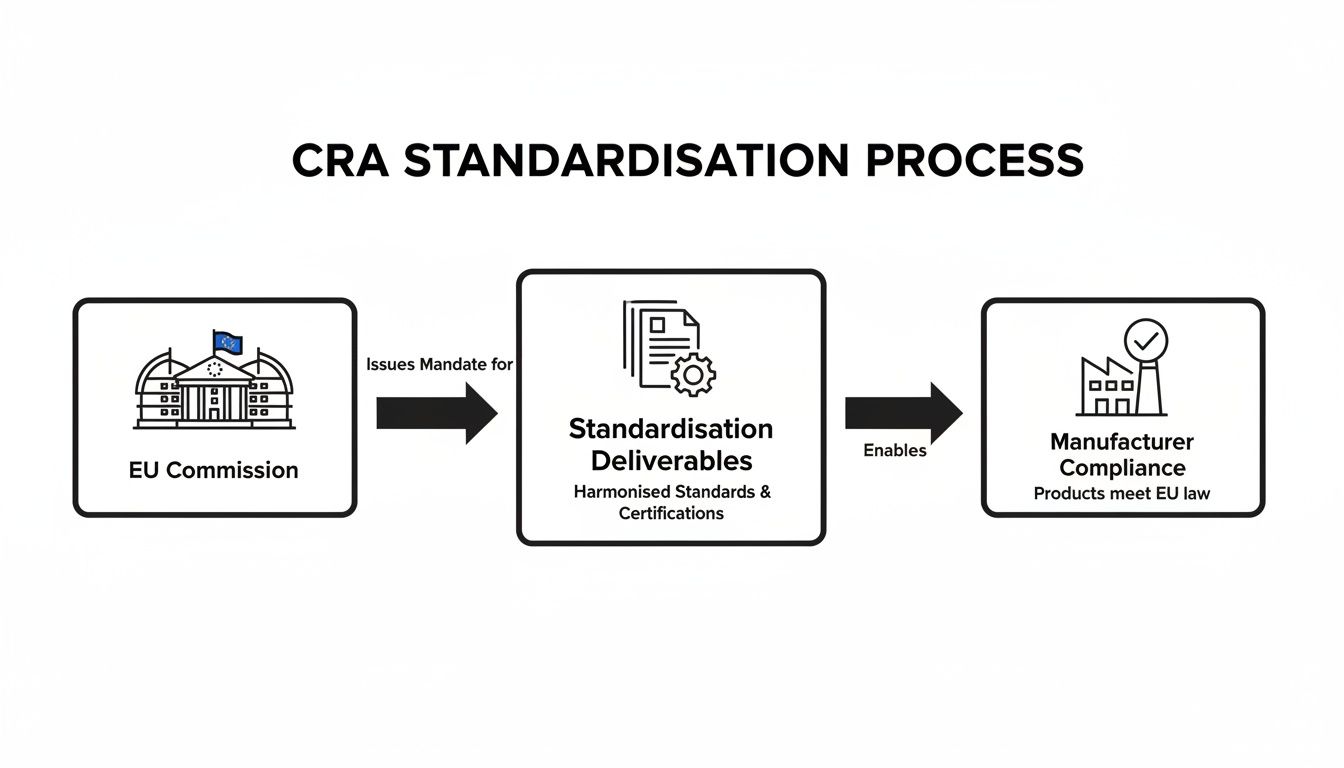
This process, from the EU Commission’s request to the final harmonised standards, is what gives you a clear path to proving your product is secure.
A Practical Example with a Smart Thermostat
Let’s apply this mapping to a real-world product: a connected smart thermostat. The manufacturer must address several key Annex I requirements to place it on the EU market.
Here’s how they could use existing standards as a blueprint:
Requirement: Secure by Default Configuration (Annex I, Part 1)
- The Problem: The thermostat has to ship with settings that minimise its attack surface out of the box. That means no default passwords like “admin” and all unnecessary ports closed.
- Standard-Based Solution: The team can look to ETSI EN 303 645, a leading consumer IoT security standard. It explicitly requires unique per-device credentials and forbids universal default passwords, providing a clear, testable solution.
Requirement: Integrity Protection (Annex I, Part 1)
- The Problem: The device’s firmware and configuration data must be protected from unauthorised modification. This is critical for preventing attackers from pushing malicious updates.
- Standard-Based Solution: The manufacturer can implement secure boot and signed firmware updates by following the principles in IEC 62443-4-2. This industrial standard outlines technical requirements for ensuring software integrity, which can be adapted perfectly for a smart thermostat. This ensures only officially signed and verified firmware can be installed.
Requirement: Coordinated Vulnerability Disclosure (Annex I, Part 2)
- The Problem: The company needs a clear, public process for receiving vulnerability reports from security researchers and a documented plan for fixing them.
- Standard-Based Solution: They can model their vulnerability disclosure policy on ISO/IEC 29147, which provides a complete framework for how organisations should handle vulnerability disclosure. This includes setting up a clear point of contact (e.g., a “security@company.com” email and a dedicated web form), defining timelines for acknowledging reports, and coordinating the release of security patches.
By using these existing standards, the thermostat manufacturer isn’t waiting around for the final CRA harmonised standards to be published. They are actively building a compliant product based on globally recognised best practices.
When the official standards are eventually released, they will almost certainly be aligned with these existing frameworks, making the final compliance check a much smaller lift. This proactive mapping turns vague legal obligations into an actionable engineering roadmap.
How to Use Standards in Your Conformity Assessment
Using CRA harmonised standards in your conformity assessment isn’t just good practice; it’s the most effective way to build an ironclad compliance case. Think of these standards less as technical guides and more as powerful legal instruments. Referencing them in your technical documentation is the clearest path to demonstrating due diligence and achieving the all-important “presumption of conformity.”
This process translates abstract legal obligations into a concrete, auditable checklist. To navigate your conformity assessment effectively, you have to understand the principles of managing audit evidence. When you adopt a harmonised standard, you’re essentially using a pre-approved solution that regulators already recognise, which simplifies the entire audit conversation.
A Practical Example: A Smart Lock Manufacturer
Let’s make this real. Imagine you’re a manufacturer of a ‘Class I’ smart lock. As a Class I product, it’s considered higher-risk and requires a more rigorous conformity assessment. Your goal is to prove the lock meets all the relevant essential requirements from Annex I of the Cyber Resilience Act.
Your journey starts by identifying the right harmonised standards. For a smart lock, you’d be worried about secure authentication, access control, protection against physical tampering, and secure communication with the user’s phone.
The compliance team’s job is to map these risks to specific standards.
- For secure authentication: They might find a standard that specifies multi-factor authentication protocols and how to defend against brute-force attacks (e.g., locking an account after 5 failed attempts).
- For secure communication: They would look for a standard that mandates TLS 1.3 with strong cipher suites for all data sent between the lock and its app.
- For vulnerability handling: A horizontal standard on vulnerability disclosure and management would give them a ready-made framework for meeting their post-market obligations.
By applying these standards during design and development, you aren’t just making the product more secure. You’re systematically building your compliance evidence, piece by piece.
Using harmonised standards transforms your conformity assessment from a defensive exercise of justifying your design choices into a proactive demonstration of alignment with EU-endorsed best practices. It fundamentally changes the conversation with auditors and regulators.
Using Standards in Your Technical Documentation
Your technical documentation is where you prove your work. Referencing the standards you’ve applied is non-negotiable, as it provides objective evidence that you’ve met specific requirements in Annex I. The table below shows how you can integrate these references directly into your technical file, as structured by Annex VII.
| Documentation Section (per Annex VII) | What to Include | Practical Example |
|---|---|---|
| Product Description & Architecture | A list of the harmonised standards that influenced the overall design and security architecture. | "The product architecture was developed in alignment with EN 303 645 to ensure baseline IoT security. Secure communication channels are implemented as per section 5.3-5 of the standard, using TLS 1.3 for all external communications." |
| Risk Assessment Documentation | A mapping showing how specific risks identified in your assessment are mitigated by controls defined in a standard. | "Risk ID #042 (Unauthorised remote unlocking) is mitigated by implementing multi-factor authentication, as specified in ETSI TS 103 736, clause 6.2. The control effectiveness is considered high due to full compliance with the standard." |
| Vulnerability Handling Procedures | Reference the horizontal standard you follow for your coordinated vulnerability disclosure and management policy. | "Our vulnerability handling process, documented in document VH-POL-001, is based on the framework provided by ISO/IEC 29147:2020 (Vulnerability Disclosure). We adhere to the timelines and communication protocols outlined in section 7 of the standard." |
| Test Reports & Validation | Evidence that your product was tested against the requirements of a specific standard and passed. | "Penetration test report #PT-2025-08-01 includes results for test cases derived from OWASP ASVS v4.0.3, which we apply in conjunction with harmonised standards. All identified medium-risk and higher findings related to authentication (section V2) have been remediated and verified." |
By embedding these references throughout your documentation, you create a clear, traceable line from a legal requirement to a technical implementation, all backed by an EU-recognised standard. This makes your technical file far more robust and easier for a regulator or Notified Body to review.
Documenting Compliance in the EU Declaration of Conformity
Once your product is developed and tested in line with these standards, the final, critical step is to declare it. You must explicitly list every single harmonised standard you’ve applied in your EU Declaration of Conformity.
This declaration is a formal, legally binding statement that your product complies with all relevant EU laws. Listing the standards acts as a powerful summary of all the evidence contained in your detailed technical file. When a market surveillance authority sees recognised standard numbers on this document, it gives them immediate confidence that you’ve followed an approved path.
For more on the different pathways, check out our complete guide on the CRA conformity assessment process.
How Standards Help Different Assessment Modules
The real power of harmonised standards becomes obvious when you look at the different conformity assessment modules. The CRA lays out several routes depending on your product’s risk classification.
Module A (Internal Production Control): For lower-risk products, manufacturers can self-assess. In this case, referencing harmonised standards in your technical file provides a strong, structured basis for your self-declaration. It makes your claims far more robust and defensible if they are ever questioned.
Modules B+C or H (Third-Party Assessment): For critical products like our Class I smart lock, a Notified Body gets involved. Here, harmonised standards are indispensable. Your technical file, filled with references to these standards, becomes the primary evidence you submit. It simplifies the audit, cuts down on ambiguity, and can significantly speed up the certification process.
Ultimately, by relying on CRA harmonised standards, the smart lock manufacturer doesn’t just build a more secure product. They create a clear, defensible path through the complexities of conformity assessment, reducing regulatory friction and ensuring confident access to the EU market.
The High Cost of Non-Compliance
Failing to comply with the Cyber Resilience Act is much more than a simple legal oversight. It’s a serious business risk with cascading consequences that can cripple your operations. Ignoring your CRA obligations can lead to severe financial penalties, total exclusion from the EU market, and reputational damage that erodes customer trust for years to come.
Thinking of CRA compliance as just another expense is a dangerous mistake. It is a critical investment in your company’s risk management and brand protection. The penalties are deliberately designed to be steep enough to make non-compliance a completely unsustainable business strategy.
The Financial Penalties for Non-Compliance
The financial penalties for failing to meet CRA requirements are significant. The law is enforced by national authorities across EU member states, who have the power to issue substantial administrative fines ranging from €5 million to €15 million, depending on how severe the violation is.
The most serious infringements carry the heaviest penalties. Things like failing to meet the essential security requirements in Annex I or ignoring the manufacturer obligations in Articles 10 and 11 can cost you dearly. For example, a company with €100 million in annual turnover could face a €2.5 million fine for failing to report a severe vulnerability. Fines can reach up to €15 million or 2.5% of your company’s total worldwide annual turnover for the previous financial year, whichever is greater. You can find more detail on the EU’s penalty framework on datainnovation.org.
These fines aren’t just theoretical threats. They are structured to have a real, painful impact, even on the largest global corporations, ensuring every organisation takes its product cybersecurity duties seriously.
Market Access Restrictions and Recalls
Beyond the direct financial hit, National Market Surveillance Authorities have serious powers to control what gets sold in the EU. These bodies are the on-the-ground enforcers of the CRA, and their actions can bring your business to a grinding halt almost overnight.
If a product is found to be non-compliant, these authorities can:
- Order a Product Withdrawal: Forcing you to pull the product from the entire EU supply chain.
- Mandate a Product Recall: Requiring you to retrieve products already sold to customers—a logistically nightmarish and expensive process.
- Ban a Product from the Market: Prohibiting your product from being sold anywhere in the EU until you can prove it’s fully compliant.
A market recall is far more than a logistical headache. It’s a public announcement that your product is unsafe, which can permanently shatter customer loyalty and your brand’s reputation.
The power to enforce these measures makes compliance with the CRA not just a good idea, but a non-negotiable prerequisite for market entry and survival. For a deeper look into this topic, you can read our detailed guide on CRA penalties and enforcement actions.
A Practical Scenario: The Non-Compliant Smart Toy
Let’s walk through a practical scenario to see how this plays out. Imagine a company launches “ConnectaBear,” an internet-connected teddy bear, in the EU. To get to market faster, the team cuts corners, failing to implement a secure update mechanism or properly secure the data sent from the toy’s microphone.
A security researcher quickly discovers the toy is vulnerable to a simple remote attack, allowing anyone to listen in on children’s private conversations. The researcher reports this to the manufacturer, but the company fails to respond or issue a patch quickly enough, violating the CRA’s vulnerability handling rules.
The researcher then notifies the national surveillance authority in Germany. What happens next is a devastating chain reaction for the company:
- Immediate Investigation: The authority investigates and quickly confirms the non-compliance.
- Forced Market Withdrawal: An order is issued to immediately stop all sales of ConnectaBear across all 27 EU member states.
- Crippling Fines: The company is hit with a multi-million euro fine for failing to meet the essential security requirements of Annex I.
- Reputational Collapse: News of the “spying teddy bear” goes viral. The brand becomes synonymous with unsafe products and a total betrayal of consumer trust.
The financial cost of the fines and the recall is immense, but the reputational damage is even worse. Rebuilding that lost trust could take years, if it’s even possible. This powerful example highlights a core truth: proactive compliance is infinitely cheaper than reactive crisis management.
Your Action Plan for CRA Readiness
It’s time to move from theory to action. While the final CRA harmonised standards are still on the horizon, waiting for them to be published is not a winning strategy. You can—and absolutely should—start building your compliance framework now, using existing best practices as your guide.
This section lays out a concrete roadmap for your organisation. The goal is to act immediately and weave security deep into your company culture. Treat compliance as a core part of your product lifecycle, not a box-ticking exercise to be rushed at the end.
Perform a Proactive Gap Analysis
First things first: you need to know where you stand. The only way to do that is with a thorough gap analysis, comparing your products against the essential security requirements in CRA Annex I.
Since the final standards don’t exist yet, you’ll need to use established frameworks as reliable proxies. Think of them as the next best thing.
For instance, benchmark your product’s security against:
- ETSI EN 303 645 for a solid baseline on consumer IoT security. A practical first step is to check if your product avoids hardcoded default passwords—a key provision in this standard.
- The IEC 62443 series if you operate in industrial control systems or operational technology. You could start by assessing your secure boot implementation against the requirements in IEC 62443-4-2.
This analysis will quickly highlight the most obvious gaps in your security posture, whether it’s a missing secure-by-default configuration or weak data integrity controls. Documenting everything gives you a clear, prioritised backlog of engineering work to tackle long before the compliance deadlines hit.
Document Your Security and Vulnerability Processes
The CRA puts a massive emphasis on secure development and ongoing vulnerability management. Your job is to establish and, most importantly, document these processes right away. This isn’t just about having the right procedures; it’s about being able to prove them to an auditor.
Start by formalising your:
- Secure Development Lifecycle (SDLC): Write down exactly how security fits into every stage of your product’s journey—from initial design and coding through to testing and deployment. Standards like IEC 62443-4-1 are a great reference here.
- Vulnerability Management and Disclosure Policy: Create a clear, public policy based on proven frameworks like ISO/IEC 29147 and ISO/IEC 30111. This policy must define how you handle incoming vulnerability reports, how you triage them, and how you coordinate patches with your users.
These documents will become the backbone of your technical file, offering powerful proof that you take lifecycle security seriously.
Proactive preparation is about building your compliance story piece by piece. When the final CRA harmonised standards are published, a well-documented SDLC and vulnerability management plan will mean you are already 90% of the way there.
Structure Your Technical Documentation Now
Don’t wait until the last minute to start pulling together your technical documentation. The CRA’s Annex VII gives you a clear blueprint of the information you’ll need to provide. Start structuring this file today, even if some sections are just placeholders for now.
Set up a central repository (e.g., in Confluence or a shared drive) and begin filling it with:
- Product architecture diagrams.
- The results of your initial risk assessment.
- The SDLC and vulnerability handling policies we just talked about.
- A preliminary Software Bill of Materials (SBOM).
Starting this early avoids the inevitable last-minute scramble. It also helps build a “document-as-you-go” habit within your engineering teams, making the final audit process infinitely smoother.
A Practical Example: The CRA Task Force
A mid-sized manufacturer of smart lighting systems realised that sitting on their hands was not an option. They formed a cross-functional ‘CRA Task Force’, pulling in people from engineering, legal, product management, and IT.
Their first sprint focused on exactly the steps outlined above. They ran a gap analysis using ETSI EN 303 645 as their benchmark, started documenting their previously informal vulnerability response process, and built a digital skeleton of their Annex VII technical file.
By taking these tangible actions, they transformed an abstract regulatory threat into a manageable project with clear goals. Now, they are well-positioned for full compliance when the deadlines arrive.
Frequently Asked Questions About CRA Harmonised Standards
The topic of harmonised standards often raises practical questions for manufacturers. Here are direct answers to some of the most common queries we see regarding CRA harmonised standards and their role in your compliance strategy.
Are Harmonised Standards Mandatory to Use?
No, using harmonised standards is completely voluntary. However, they are designed to provide a significant legal advantage known as the “presumption of conformity.”
This means that if you correctly apply a relevant harmonised standard, market surveillance authorities will presume your product automatically meets the corresponding CRA requirements covered by that standard. It’s a recognised shortcut to demonstrating compliance.
If you choose not to use them, the burden of proof is entirely on you. You must independently document and justify how your alternative technical solutions achieve an equivalent level of security—a far more intensive and legally precarious path.
What if There Is No Harmonised Standard for My Product?
This will be a common scenario, especially in the beginning. The initial development of type C (vertical) standards is focused on high-risk product categories, leaving many products without a specific standard. For example, a manufacturer of a simple connected coffee maker might not find a dedicated standard.
Even without a dedicated harmonised standard, you are still fully obligated to meet all the essential cybersecurity requirements in Annex I. Your compliance must be built on a thorough, product-specific risk assessment.
In these cases, you can reference existing, non-harmonised standards like ETSI EN 303 645 or the IEC 62443 series as evidence of best practice and due diligence in your technical file.
When Will the Final Harmonised Standards Be Published?
The European Commission has laid out an ambitious, phased timeline for publication. Manufacturers should not wait for these final documents before acting.
Key horizontal standards, especially those covering processes like vulnerability handling, are expected by August 2026.
The first set of vertical standards for specific high-risk products is scheduled for October 2026. A broader horizontal standard for general product cybersecurity requirements is slated for October 2027. Your best strategy is to start preparing now, using existing best practices and standards as your guideposts.