The EU’s Cyber Resilience Act (CRA) is set to reshape digital product security, introducing strict new rules for manufacturers placing products on the European market. A central part of this legislation is the classification of certain products as ‘critical’ under Annex IV, which subjects them to more rigorous cybersecurity obligations due to their potential impact on public safety and essential services.
Determining whether your product falls into one of these high-risk categories is the first and most important step toward compliance. This is not just a paperwork exercise; it dictates the level of security scrutiny, conformity assessment, and post-market surveillance your products will face. Misclassification could lead to non-compliance, market withdrawal, and significant financial penalties.
This article provides a definitive breakdown of the key product categories and security practices that fall under the expanded scope of critical products, including those in Class I and Class II. We will examine what each category entails, why it is considered critical, and the specific obligations you must meet. For each point, you will find practical examples and actionable steps to help your organisation prepare for the CRA’s fast-approaching deadlines. This guide is designed to give manufacturers, compliance managers, and product security teams a clear, itemised path to understanding the CRA Annex IV critical products list and ensuring their products remain compliant and competitive within the EU.
1. Connected IoT Devices and Embedded Systems
This broad category encompasses devices with network connectivity that collect, transmit, or process data, often operating autonomously in sensitive environments. The Cyber Resilience Act (CRA) identifies these products as critical because a single compromised device, such as a smart meter or an industrial controller, can have cascading effects, potentially disrupting essential services like energy grids, water supplies, or healthcare. Their inclusion in the CRA Annex IV critical products list signifies their systemic importance and the heightened security expectations placed upon their manufacturers.
Why are they critical?
The criticality stems from their function and placement within larger systems. A smart home security system (e.g., Bosch Smart Home or Philips Hue Secure) processes sensitive personal data and controls physical access to a home. An Industrial IoT (IIoT) controller from a vendor like Siemens or ABB manages machinery in a factory, where a malfunction could halt production or cause physical harm. Similarly, connected medical devices and the infrastructure for smart meters (e.g., from Landis+Gyr) are fundamental to public health and utilities, making their security a matter of public safety.
Actionable Next Steps for Manufacturers
To prepare for conformity, manufacturers must adopt a security-first approach throughout the product lifecycle. This involves more than just secure coding; it requires documented processes and transparent operations.
Key Obligations & Practical Actions:
- Software Bill of Materials (SBOM): Begin by inventorying all firmware and software components, including open-source libraries and proprietary code. Practical example: Your smart thermostat’s SBOM would list its operating system (e.g., FreeRTOS), network libraries (e.g., lwIP), and any third-party APIs it calls.
- Secure Update Mechanisms: Document how security updates will be delivered. Practical example: A manufacturer of connected cars might use an over-the-air (OTA) update system that downloads patches in the background and applies them when the vehicle is parked, ensuring critical safety systems are always current.
- Vulnerability Management Plan: Before placing a product on the market, establish a clear and public vulnerability disclosure policy. Practical example: A company selling smart locks would publish a
security.txtfile on their website, providing a clear email contact for researchers to report potential security flaws. - Defined Support Period: The CRA mandates security support for the expected product lifetime or a minimum of five years. For long-lifespan devices like industrial controllers, plan for a support window closer to 10 years to provide necessary security patches long after the initial sale. Practical example: An industrial robot manufacturer must commit to providing security updates for at least five years, even if the model is discontinued, and clearly state this support period in their documentation.
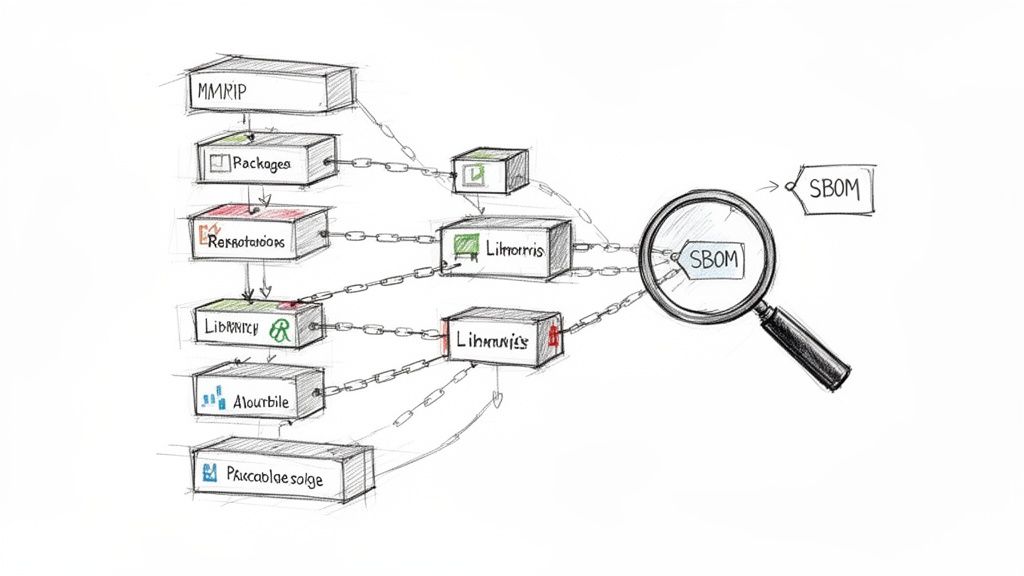
2. Software Supply Chain and Open Source Components
This category focuses on the software products and libraries integrated into digital products, including open-source components, third-party Software Development Kits (SDKs), and proprietary code. The Cyber Resilience Act (CRA) views software supply chain security as critical because a single vulnerability in an underlying component can propagate to countless end products, creating widespread risk. The inclusion of these components in the CRA Annex IV critical products list underscores that software dependencies are as important to secure as the final product itself.
Why are they critical?
The criticality of software components stems from their pervasive and often hidden nature within modern applications. High-profile incidents like the Log4Shell vulnerability in the Apache Log4j library demonstrated how a flaw in one popular logging utility could expose millions of applications to remote code execution. Similarly, the SolarWinds supply chain attack, which compromised over 18,000 organisations, showed how malicious code inserted into a trusted software update can have devastating consequences. The complex dependency trees in ecosystems like npm, PyPI, or containerised applications using Kubernetes make it difficult to track every component, making them a prime target for attackers.
Actionable Next Steps for Manufacturers
To achieve compliance, manufacturers must gain deep visibility into their software dependencies and actively manage them throughout the product lifecycle. This requires moving from a reactive stance to a proactive, security-first approach to component management.
Key Obligations & Practical Actions:
- Automated SBOM Generation: Integrate the creation of a Software Bill of Materials (SBOM) directly into your CI/CD build pipeline. Practical example: Use a tool like CycloneDX or SPDX Generator to create a machine-readable SBOM file every time your application is built, ensuring it is always current.
- Third-Party Risk Assessment: Establish a formal process for evaluating any new open-source or commercial dependency before it is integrated. Practical example: Before using a new JavaScript library from npm, analyse its download statistics, issue tracker activity, and whether it has a history of security vulnerabilities to gauge its health.
- Vulnerability Scanning Gates: Implement automated software composition analysis (SCA) tools, such as Snyk or Black Duck, as quality gates in your development workflow. Practical example: Configure your Jenkins or GitHub Actions pipeline to fail the build if an SCA scan detects a dependency with a CVSS score of 9.0 or higher.
- Dependency Update Roadmap: Maintain an internal roadmap for updating third-party components. Practical example: A software team could create a quarterly plan to update all high-priority libraries to their latest stable versions, preventing the accumulation of “security debt.”
3. Cybersecurity Incident Handling and Vulnerability Disclosure
This category focuses not on a physical product but on the crucial processes and infrastructure for managing cybersecurity vulnerabilities. It covers how manufacturers detect, receive reports on, assess, and remediate security flaws in their products. The Cyber Resilience Act deems these processes critical because organised, timely vulnerability handling is essential to prevent widespread exploitation of security gaps. Its inclusion in the CRA Annex IV critical products list means the systems and workflows for managing vulnerabilities are themselves subject to strict scrutiny.
Why are they critical?
The criticality of these processes lies in their direct impact on public safety and trust. A disorganised or delayed response to a reported vulnerability can leave thousands or even millions of devices exposed to attack. For example, the coordinated disclosure process managed by the Microsoft Security Response Center (MSRC) ensures that when a flaw is found in Windows, a patch is developed and tested before attackers can widely exploit it. Similarly, programs run by Apple and the advisories issued by CISA depend on structured, predictable workflows to protect users at scale. A breakdown in this chain is as dangerous as a flaw in the product itself.
Actionable Next Steps for Manufacturers
To meet CRA obligations, manufacturers must formalise their vulnerability management from a reactive practice into a documented, auditable, and transparent operation. This requires clear policies, dedicated tools, and defined responsibilities. As part of maintaining a secure product lifecycle, effective incident management is crucial. You can learn more about how to establish robust processes by exploring incident management best practices for guidance on building resilient workflows.
Key Obligations & Practical Actions:
- Public Vulnerability Disclosure Policy: Publish a clear policy document on your website. Practical example: A policy might state: “We aim to acknowledge receipt of all vulnerability reports within 48 hours and provide an initial assessment within 5 business days.”
- Establish
security.txt: Implement asecurity.txtfile at the root of your primary domain. Practical example: The file forexample.comwould be located athttps://example.com/.well-known/security.txtand contain contact details likeContact: mailto:security@example.com. - Define Severity and Timelines: Create internal service-level objectives (SLOs) for patching based on severity. Practical example: Your internal policy could state that vulnerabilities with a “Critical” CVSS score (9.0-10.0) must be patched within 15 days of confirmation.
- Document Incident Response Workflows: Use tools to map out your entire process from vulnerability intake to patch deployment and public disclosure. Practical example: Use a flowchart in Confluence or a Kanban board in Jira to visualise the stages a reported vulnerability goes through:
New->Triaging->Fix in Progress->Patch Deployed->Closed. This documentation is key evidence for conformity assessments and demonstrates that you have a mature process for CRA vulnerability handling. - Track Key Metrics: Monitor and record metrics such as time-to-acknowledge, time-to-patch, and patch adoption rates. Practical example: A quarterly security report could show that the average time to patch critical vulnerabilities was reduced from 30 days to 12 days, demonstrating process improvement.
4. Secure Product Update Mechanisms and Patch Management
This category covers the technical infrastructure that enables the secure delivery and installation of software updates, including bug fixes and security patches. The Cyber Resilience Act (CRA) designates these update mechanisms as critical because they are the primary pathway for remediating vulnerabilities after a product is on the market. Their inclusion in the CRA Annex IV critical products list highlights that a compromised update system can be used to push malicious code to an entire fleet of devices, turning a security tool into a weapon.
Why are they critical?
The criticality of update mechanisms stems from their direct access to the core software of a product. A flaw in this system could allow an attacker to bypass security measures and take full control of devices. For instance, the robust over-the-air (OTA) update architecture used by Tesla is essential for deploying safety-critical vehicle software; if compromised, it could affect thousands of cars simultaneously. Similarly, the staged rollout process of Microsoft’s Windows Update for Business and the phased releases of Android Security updates are designed to manage risk, but the underlying mechanisms themselves must be secure to prevent widespread system compromises. Infrastructure services like AWS IoT Device Management and Azure Device Update are also critical as they manage updates for countless enterprise and consumer products.
Actionable Next Steps for Manufacturers
To achieve conformity, manufacturers must design their update mechanisms with security as a core architectural principle, not as an afterthought. This requires documented procedures and robust technical controls to ensure the integrity and authenticity of every update.
Key Obligations & Practical Actions:
- Integrity and Authenticity: Ensure all updates are cryptographically signed. Practical example: The firmware update file for a Wi-Fi router should be signed with the manufacturer’s private key. The router will then use the corresponding public key to verify the signature before installation, rejecting any tampered files.
- Secure Delivery: Document the entire update delivery process. Practical example: All update files should be downloaded over a secure, encrypted channel like HTTPS with TLS 1.3 to prevent man-in-the-middle attacks.
- Resilience and Rollback: Test and document rollback procedures to recover from a failed update without leaving the device in an insecure or non-functional state. Practical example: A smart TV should keep a copy of the previous stable firmware version so it can automatically revert if an update fails to install correctly, preventing it from becoming “bricked.”
- Plan for Offline Devices: For products without direct internet access, create secure procedures for updates via physical media (e.g., USB) or managed networks. Practical example: An industrial machine on an air-gapped network could be updated by a technician using a company-issued, encrypted USB drive that is verified by the machine before use. As part of your documentation, you can find further details about CRA update requirements to ensure your processes are compliant.
- Minimise Bandwidth: Where possible, implement delta updates that only transmit the changes between software versions. Practical example: Instead of sending a full 500MB firmware image, a delta update for a security camera might only be 5MB, containing just the patched binaries.
5. Security Testing, Vulnerability Scanning, and Penetration Testing
This category covers the formal processes and tools used to proactively identify, analyse, and mitigate security vulnerabilities before a product reaches the market. It includes methods like static and dynamic application security testing (SAST/DAST), software composition analysis (SCA), and manual penetration testing. The Cyber Resilience Act classifies these testing solutions as critical because their effectiveness directly determines whether vulnerabilities in other software and hardware products are discovered and fixed or are left exposed to potential exploits. Their inclusion in the CRA Annex IV critical products list underscores their fundamental role in securing the entire digital supply chain.
Why are they critical?
The criticality of these tools lies in their function as a gatekeeper for software quality and security. A flaw in a vulnerability scanner could lead to false negatives, giving manufacturers a misleading sense of security while their products remain vulnerable. For example, if a SAST tool used by a smart lock manufacturer fails to detect a known remote code execution flaw, that vulnerability will ship directly to consumers’ homes. Frameworks like the OWASP Top 10 are built on the assumption that testing tools work correctly. The German BSI C5 audit process and NIST’s Software Assurance (SwA) practices depend on reliable testing outcomes to certify products for sensitive government use, making the integrity of the testing process itself a matter of public and national security.
Actionable Next Steps for Manufacturers
Manufacturers of these testing tools must demonstrate exceptional rigour in their own development and validation processes. Proving that your tool reliably finds what it claims to find is paramount.
Key Obligations & Practical Actions:
- Documented Testing Efficacy: Maintain detailed evidence of your tool’s effectiveness. Practical example: A DAST scanner provider should maintain a test suite of vulnerable applications (like OWASP Juice Shop) and produce reports showing that its tool correctly identifies specific flaws like SQL Injection or Cross-Site Scripting.
- Secure Development Lifecycle (SDL): Implement and document a robust SDL for the testing tool itself. Practical example: The development team for a SAST tool should conduct regular threat modeling sessions to identify and mitigate potential attacks against the tool, such as evasion techniques that could cause it to miss vulnerabilities.
- Clear Vulnerability Thresholds: Your tool must be able to categorise findings based on severity (e.g., Critical, High, Medium, Low) using a recognised standard like CVSS. Practical example: The tool’s dashboard should allow a user to configure a rule: “Fail the CI/CD build if any new ‘Critical’ vulnerability is detected in a dependency.”
- External Audits and Penetration Testing: For tools intended to secure critical products, engaging independent third parties for regular security assessments is essential. Practical example: A vendor of a penetration testing platform should hire an external firm annually to attempt to hack their own product and publish a summary of the findings to demonstrate transparency. You can explore options like penetration testing as a service to meet these ongoing requirements.
6. Post-Market Surveillance and Security Monitoring
This category refers to the continuous processes manufacturers must establish to monitor products after they have been placed on the market. It covers the active detection of security incidents, analysis of user-reported issues, and tracking of emerging threats and vulnerabilities. The Cyber Resilience Act (CRA) mandates this as a critical function because vulnerabilities are inevitably discovered after a product’s release. Effective post-market surveillance, therefore, is not just a reactive measure but a core part of a product’s ongoing security posture, ensuring that risks are managed throughout its entire lifecycle.
Why is it critical?
The criticality of post-market surveillance stems from the dynamic nature of cybersecurity threats. A product secure at launch can become vulnerable overnight due to a newly discovered flaw in a third-party library or an innovative attack technique. Without a structured monitoring system, manufacturers are blind to these risks, leaving users exposed. For products on the CRA Annex IV critical products list, a failure in post-market response could lead to widespread system disruption. Examples like Microsoft’s Security Update Guide, which tracks patches across its ecosystem, and Google Play Protect’s constant scanning for malicious apps, demonstrate the scale and necessity of these operations for maintaining trust and safety.
Actionable Next Steps for Manufacturers
Manufacturers must move beyond a “ship and forget” mindset and build a robust, documented surveillance and response framework. This involves creating clear channels for communication and defined internal procedures.
Key Obligations & Practical Actions:
- Establish a Public Incident Reporting Channel: Create a straightforward way for security researchers and users to report vulnerabilities. Practical example: A company could create a dedicated “Report a Vulnerability” page on its website with a clear form, ensuring submissions are routed directly to its security team’s ticketing system.
- Integrate with Threat Intelligence Feeds: Proactively monitor for threats by integrating your security operations with public and private threat intelligence feeds. Practical example: Set up automated alerts that notify your security team whenever a new CVE is published for an open-source component listed in your product’s SBOM.
- Document Incident Response Workflows: Create a formal plan that details how your organisation will receive, assess, triage, and remediate reported incidents. Practical example: A documented workflow might specify that upon receiving a critical report, the on-call security engineer must acknowledge it within 4 hours and convene a triage meeting with the relevant development team within 24 hours.
- Maintain Records for Compliance: The CRA requires that records of all post-market security incidents and the actions taken in response are maintained for at least 10 years. Practical example: Use a system like Jira or a dedicated incident management platform to log every step of the response, creating an auditable trail from initial report to patch deployment and public disclosure.
7. Technical Documentation, Security Evidence, and Compliance Artifacts
While not a physical product itself, this category represents the complete body of evidence that manufacturers must create and maintain to prove a product’s security and conformity with the Cyber Resilience Act. It includes all technical files, test results, security architecture diagrams, and procedures required by Annexes II and VII of the CRA. This documentation serves as the primary means for regulatory authorities to inspect and verify compliance, making its thoroughness and accuracy a critical component of market access.
Why are they critical?
The criticality of this documentation lies in its role as the foundation of trust and accountability. Without detailed, auditable records, claims of security are unverifiable. For products on the CRA Annex IV critical products list, where a security failure can have systemic consequences, this evidence is non-negotiable. For instance, the technical file for a high-assurance product, similar to a Common Criteria evaluation report, provides authorities with the necessary insight to assess its resilience against sophisticated attacks. Likewise, documentation for medical devices, mirroring ISO 13485 standards, is essential for ensuring patient safety and data integrity.
Actionable Next Steps for Manufacturers
Manufacturers must treat documentation not as a final-step administrative task, but as an integral deliverable created throughout the development lifecycle. This “documentation-as-you-go” approach ensures accuracy and reduces last-minute rushes.
Key Obligations & Practical Actions:
- Structure the Technical File: Begin by creating a structured template for your technical files that aligns with CRA Annex II and VII. Practical example: Your template could be a folder structure in a shared drive or a wiki space with predefined pages for “Threat Model,” “SBOM,” “Penetration Test Reports,” and “Secure Development Policy.” To learn more about building this evidence, you can review details on creating a CRA compliance evidence pack.
- Version Control All Artifacts: Implement strict version control for all security documentation. Practical example: Store all documentation in a Git repository alongside your code, so that when a new product version is released, the corresponding version of the security documentation is tagged with it.
- Use Consistent Terminology: Standardise the language used across all documents. Practical example: Create an internal glossary that defines terms like “critical vulnerability” (e.g., CVSS 9.0+) or “timely manner” (e.g., within 72 hours) to ensure everyone from developers to legal teams is aligned.
- Prepare for Inspection: Store technical files securely with role-based access controls, but ensure they can be presented promptly upon request from a national authority. Practical example: Conduct a “mock audit” where a team member is tasked with assembling and presenting the complete technical file for a specific product version within 24 hours to test your readiness.
8. Supply Chain Risk Assessment and Third-Party Management
This category addresses the processes for evaluating and managing security risks originating from suppliers, contractors, and third-party service providers. The Cyber Resilience Act (CRA) recognises that modern digital products are rarely built in isolation. A vulnerability in an upstream component-be it a hardware manufacturer, a cloud provider, or a software library-directly compromises the security of the final product. Including these processes in the CRA Annex IV critical products list highlights that supply chain security is not optional but a fundamental aspect of a product’s overall cyber resilience.
Why are they critical?
The criticality of supply chain management stems from the interconnected nature of product development. A single weak link can undermine the entire security posture of a product. For instance, the 2023 3CX supply chain attack occurred when a compromised third-party software component led to the distribution of malware through their legitimate desktop application. Similarly, hardware trojans maliciously inserted during manufacturing, like those theorised in relation to some networking equipment, represent a severe and hard-to-detect threat. The security of a product is therefore only as strong as the security of its least secure supplier, from semiconductor manufacturing at firms like TSMC to the cloud infrastructure provided by AWS or Azure.
Actionable Next Steps for Manufacturers
To achieve conformity, manufacturers must formalise their approach to third-party risk management, moving from informal trust to documented verification. This involves creating systematic procedures for assessing, managing, and monitoring every external dependency. Beyond direct compliance, effective CRA Annex IV adherence requires robust vendor management best practices. Understanding how to navigate various relationships and agreements is key to mitigating risks throughout your product’s lifecycle.
Key Obligations & Practical Actions:
- Supplier Security Questionnaires: Develop a standardised security questionnaire aligned with CRA requirements to assess the security posture of all potential and current suppliers. Practical example: A questionnaire for a cloud provider could ask, “Do you have a current SOC 2 Type II report?” and “What is your stated SLA for notifying customers of a security breach?”
- Contractual Security Clauses: Embed specific security obligations into all supplier contracts. Practical example: A contract with a software development contractor should include a clause requiring them to run static code analysis on all delivered code and provide the scan reports as a condition of payment.
- Verification of Certifications: Do not just accept a supplier’s claims. Request and verify relevant security certifications such as ISO 27001, SOC 2 Type II, or Common Criteria evaluations as evidence of their security commitment. Practical example: When a supplier provides an ISO 27001 certificate, check the certificate’s validity and scope on the issuing accreditation body’s website.
- Ongoing Monitoring and Audits: Establish a cadence for re-assessing critical suppliers, at a minimum annually. Practical example: For a critical chip supplier, conduct an annual on-site audit of their manufacturing facility’s security controls to verify they are being enforced as contractually agreed.
CRA Annex IV: 8-Point Critical Products Comparison
| Item | Implementation complexity | Resource requirements | Expected outcomes | Ideal use cases | Key advantages |
|---|---|---|---|---|---|
| Connected IoT Devices and Embedded Systems | High — hardware + firmware + network integration, legacy constraints | Embedded development, OTA infrastructure, long-term support and supply-chain tracking | Secure lifecycle, CRA compliance, reduced exploitation in sensitive environments | Smart meters, industrial controllers, connected medical devices, edge devices | Clear CRA applicability, defined update obligations, maturing supply-chain docs |
| Software Supply Chain and Open Source Components | Medium–High — broad dependency surface and transitive risks | SBOM tooling, SCA scanners, legal/license review, dependency management | Improved transparency, faster vulnerability mitigation, reproducible builds | Software platforms, containerized apps, products with many third‑party libs | Tooling support for SBOMs, automated vulnerability feeds, reduced audit burden |
| Cybersecurity Incident Handling and Vulnerability Disclosure | Medium — procedural complexity and coordination demands | Incident response team, triage processes, communication channels, bug bounty/platform integration | Timely remediation, coordinated disclosures, reduced exploitation windows | All connected products and critical services requiring coordinated fixes | Regulatory mandate under CRA, standard severity metrics, builds customer trust |
| Secure Product Update Mechanisms and Patch Management | High — secure delivery, signing, rollback, staged rollouts | Update servers/CDN, cryptographic signing, testing/rollback infrastructure | Rapid, authenticated patching, minimized downtime and widespread compromise | IoT devices, vehicles, firmware-heavy products requiring remote fixes | Enables swift remediation, integrity guarantees, staged deployment control |
| Security Testing, Vulnerability Scanning, and Penetration Testing | Medium — tooling plus specialist expertise required | SAST/DAST/SCA tools, CI/CD integration, external pentesters for validation | Earlier vulnerability detection, reduced remediation costs, compliance evidence | Pre-release software, CI/CD pipelines, high‑risk attack surfaces | Shifts security left, standardized reporting, lowers production risk |
| Post-Market Surveillance and Security Monitoring | Medium — continuous operational effort and analysis | Telemetry systems, monitoring teams, threat intelligence feeds, ticketing | Real-world vulnerability detection, ongoing risk reduction, informed updates | Widely deployed products, services with large user bases, critical infrastructure | Detects escaped vulnerabilities, enables rapid response, regulatory demonstration |
| Technical Documentation, Security Evidence, and Compliance Artifacts | Medium — extensive documentation and lifecycle maintenance | Documentation templates, version control, evidence collection processes | Regulatory readiness, transparent evidence for audits and customers | Products subject to CRA audits, Critical/Default Class technical files | Standardized templates (Annex II/VII), reduces compliance uncertainty, legal protection |
| Supply Chain Risk Assessment and Third-Party Management | Medium–High — coordination across suppliers and subcontractors | Vendor assessments, contract clauses, certification checks, audit capability | Reduced upstream risk, contractual recourse, improved supplier hygiene | Complex hardware/software stacks, outsourced manufacturing, cloud dependencies | Risk-based supplier controls, certification verification, contractual levers for security |
From Checklist to Action Plan: Your Next Steps for CRA Compliance
Moving from awareness of the Cyber Resilience Act to a state of readiness is the most significant challenge facing technology manufacturers today. This article has served as a detailed guide, breaking down the critical obligations associated with the CRA Annex IV critical products list. We have explored the essential pillars of compliance, from managing connected IoT devices and securing the software supply chain to establishing robust incident handling and post-market surveillance.
The key insight is clear: compliance is not a destination but a continuous process. The CRA demands a fundamental cultural shift towards security by design and by default. Treating this as a mere checklist to be completed before the deadline is a recipe for failure. Instead, it must be integrated into the very fabric of your product lifecycle, from the initial concept to end-of-life support.
Key Takeaways and Immediate Actions
Understanding the theory is one thing; putting it into practice is another. Your journey from here should be structured and deliberate. Here are the most important takeaways and the immediate actions you should prioritise:
Product Classification is Your Starting Point: The first and most crucial step is to determine if your products fall under the general CRA obligations or the more stringent requirements of Annex III (Important Products) or Annex IV (Critical Products). An incorrect classification can lead to either wasted resources or, far worse, non-compliance and market exclusion.
- Action: Conduct a thorough, documented assessment of your entire product portfolio. Involve legal, engineering, and product teams to analyse product functionalities against the criteria defined in the CRA, paying special attention to the high-risk categories detailed in this article.
Documentation is Your Evidence: Under the CRA, if it isn’t documented, it didn’t happen. From the Software Bill of Materials (SBOM) and threat modelling exercises to vulnerability disclosure policies and conformity assessment records, comprehensive documentation is non-negotiable. This evidence is your primary means of demonstrating due diligence to authorities.
- Action: Establish a central repository for all compliance-related artefacts. Create templates and standardised processes for generating, reviewing, and updating technical documentation throughout the product’s lifecycle.
Cross-Functional Collaboration is Essential: Cybersecurity is no longer the sole responsibility of the security team. The CRA’s requirements touch every part of the organisation, including R&D, procurement, legal, and customer support. Fostering a shared understanding and responsibility is critical for success.
- Action: Form a dedicated CRA compliance task force with representatives from all relevant departments. Schedule regular meetings to track progress, address roadblocks, and ensure alignment across the business.
Beyond Compliance: The Strategic Advantage
While the immediate focus is on meeting regulatory deadlines, it is vital to recognise the long-term strategic value of this effort. Embracing the principles of the CRA positions your organisation as a leader in product security. It builds trust with customers, creates a powerful market differentiator, and ultimately leads to more resilient and reliable products. The investment in robust security practices today will pay dividends in customer loyalty and market share tomorrow.
The road to full compliance with the CRA, especially for those on the CRA Annex IV critical products list, will be demanding. It requires meticulous planning, dedicated resources, and a deep commitment from leadership. By breaking down the challenge into manageable steps and focusing on the core areas we’ve discussed, you can build a sustainable compliance programme. The goal is not just to satisfy regulators but to create a safer digital ecosystem for everyone.
Navigating the complexities of the CRA Annex IV critical products list and its documentation requirements can feel overwhelming. Regulus provides a centralised platform to manage your compliance journey, offering structured guidance, evidence collection tools, and clear reporting. Move from regulatory uncertainty to a clear action plan by visiting Regulus to see how we help you build, manage, and demonstrate compliance.