One of the most critical—and often misunderstood—concepts in the EU’s Cyber Resilience Act (CRA) is the ‘substantial modification’. Getting this wrong can turn what seems like a simple update into a full-blown compliance nightmare, forcing you to treat your product as brand new and start the entire conformity assessment from scratch.
Decoding the CRA Substantial Modification Definition
Think of it like renovating a house. Painting a room or fixing a faucet is just routine maintenance; you don’t need to call the building inspector. But if you decide to add an extension or knock down a structural wall, you’ve fundamentally changed the building. That kind of work demands new plans, new permits, and new inspections.
The same logic applies to digital products under the CRA. A security patch or a minor bug fix is just routine upkeep. But if an update alters the product’s core purpose, introduces new risks, or weakens its security posture, it crosses the line into a substantial modification. For manufacturers, understanding precisely where that line is drawn is a major compliance challenge.
The Legal Foundation
The CRA establishes this compliance trigger in Article 3(30). A substantial modification happens when a change made after the product is on the market either impacts its compliance with the essential cybersecurity requirements in Annex I or alters its original intended purpose.
The consequences are significant. Anyone making such a change effectively becomes the manufacturer, inheriting all the associated obligations. This means new documentation, a fresh security assessment, and updated conformity procedures.
Practical Example: An importer takes a batch of smart home hubs and, before selling them, installs custom firmware that allows the hubs to control industrial equipment. This is a substantial modification. The importer is now considered the “manufacturer” under the CRA and is responsible for a full new conformity assessment, even though they didn’t build the original device.
Drawing the Line Between Updates and Modifications
The good news is that not every change forces you to restart your compliance journey. The key is distinguishing between routine, non-substantial updates and fundamental, substantial modifications.
To make this distinction clearer, the table below compares different types of changes and how they are typically classified under the CRA.
Substantial Modification vs. Routine Update Under the CRA
This table provides a clear comparison of changes that are considered substantial modifications versus those classified as routine, non-substantial updates, helping manufacturers quickly assess their product changes.
| Type of Change | Substantial Modification (Triggers Full Re-assessment) | Non-Substantial Update (Part of Standard Maintenance) |
|---|---|---|
| Functionality | Adding a major new feature that was not part of the original design, like enabling online payments in a previously offline application. | Fixing bugs, improving performance efficiency, or making minor UI/UX adjustments that don't alter core behaviour. |
| Intended Purpose | Re-purposing a smart home thermostat through a software update to control commercial HVAC systems in large buildings. | Releasing a software patch that improves the thermostat’s energy efficiency algorithms within its existing home-use context. |
| Security Architecture | Removing or fundamentally weakening a core security control, such as replacing multi-factor authentication with a simpler login method. | Patching a known security vulnerability (e.g., a CVE) without changing the underlying security architecture or functionality. |
| Data Handling | An update that begins to collect and process new categories of personal or sensitive data not covered in the original assessment. | Optimising existing data processing workflows for better speed or efficiency, without changing the type of data collected. |
This principle of re-evaluating risk based on significant change is becoming a common theme in technology regulation. For context, you can see similar concepts emerging in the California AI law, where modifications to AI systems can also trigger new obligations.
Ultimately, correctly identifying a substantial modification is more than a box-ticking exercise. It’s about maintaining a clear, defensible, and continuous compliance strategy throughout your product’s lifecycle. For more details on the broader regulatory expectations, see our guide on the European Commission’s CRA implementation guidance.
The Two Main Triggers for a Substantial Modification
When you’re trying to figure out if a change to your product qualifies as a substantial modification under the Cyber Resilience Act, it really boils down to two key questions. Getting the CRA substantial modification definition right means understanding these triggers inside and out, as they’re the litmus test for deciding if an update is just routine maintenance or something that resets your compliance clock.
An update crosses the line into a substantial modification if it does one of two things:
- It alters the product’s original intended purpose.
- It changes the product in a way that negatively affects its compliance with the CRA’s essential security requirements.
If your update trips either of these wires, you’ve almost certainly made a substantial modification. Let’s break down exactly what each of these means with some real-world examples.
Trigger 1: Changing the Intended Purpose
The intended purpose is the bedrock of your product’s original risk assessment and compliance strategy. It defines what your product is meant to do, who it’s for, and the environment it’s designed to operate in. As soon as you push an update that expands this scope, you’ve fundamentally changed the product’s risk profile.
Practical Example: A smart camera is originally marketed for indoor home monitoring. Its intended purpose is clear: helping a family keep an eye on their living room. A firmware update is released that adds features for outdoor, all-weather surveillance and integrates with a commercial security firm’s monitoring platform.
This is a substantial modification. The change expands the original “use, context, and conditions of use,” turning a simple home gadget into a commercial-grade security tool. This isn’t just a new feature; it’s a completely new job for the product. The risks tied to a commercial security system—like data privacy in public spaces or resilience against sophisticated, targeted attacks—are miles apart from those of a basic indoor camera. That shift in purpose makes the original security assessment obsolete.
Trigger 2: Affecting Security Compliance
The second trigger is any change that weakens the product’s ability to meet the essential cybersecurity requirements laid out in Annex I of the CRA. These requirements are the technical core of the regulation, covering everything from secure-by-design principles to vulnerability management.
A change becomes substantial if it degrades the product’s security posture or introduces new, unassessed risks.
Practical Example: A developer of a connected industrial sensor releases an update. To boost data processing speed, the update disables Transport Layer Security (TLS) encryption for data sent to the cloud, reverting to an unencrypted protocol.
This move has an immediate and direct impact on compliance. By stripping away a critical security control (encryption in transit), the developer has left data exposed to interception. This compromises one of the CRA’s core security principles, making the change a substantial modification. A new, comprehensive conformity assessment would be mandatory. You can find out what that involves in our guide on how to perform a CRA risk assessment.
Distinguishing these triggers from routine work has been a major point of discussion for the industry. It’s now clear that standard security patches, bug fixes, and minor functional tweaks like UI adjustments do not count. However, any change that introduces features handling sensitive data, alters security configurations, or adds new functions in a way that increases cybersecurity risk will almost always cross the substantial modification threshold.
Real-World Examples of Substantial Modifications

The theory behind a substantial modification is one thing, but spotting it in the wild during a hectic development cycle is another. That grey area between a routine patch and a change that forces a full re-assessment is where many product teams will get caught out.
To really understand where the CRA substantial modification definition draws the line, we need to move from abstract rules to concrete scenarios. Let’s look at what this means for software, firmware, and hardware, linking each example back to the core triggers: changing the intended purpose or degrading the product’s ability to meet security requirements.
Software Modification Adding a Sensitive Feature
Let’s start with a common software scenario. A company has a simple messaging app for internal teams, designed and assessed for exchanging basic text on a trusted corporate network. The initial risk assessment was straightforward, focusing on a limited, low-risk use case.
Then, marketing decides the app needs a new file-sharing feature. The update lets users upload documents and share them directly with external business partners.
This isn’t just a feature bump; it’s a clear substantial modification. The reasoning is twofold:
- Change in Intended Purpose: The app has morphed from an internal chat tool into an external collaboration platform. This new function was completely outside the scope of the original conformity assessment.
- Change in Data Handling & Risk Profile: The product now handles potentially sensitive documents and transmits them outside the trusted network. This introduces a whole new class of risks—data exfiltration, unauthorised access by third parties—that the original security model never accounted for.
Because the product’s risk profile has fundamentally changed, the original assessment is obsolete. A new, full conformity assessment is required to address the security implications of this new functionality.
Practical Example: By adding a feature that processes new, more sensitive data types (e.g., financial reports, legal contracts) and expands the product’s use case to external collaboration, the developer has crossed the substantial modification threshold. The product’s core function and associated risks have been fundamentally altered.
Firmware Modification Enabling New Connectivity
Now for a classic firmware example. A manufacturer makes industrial sensors used in factories to monitor machine temperatures. Their security model is simple because the product is designed for one thing: connecting to a private, air-gapped industrial network via an Ethernet cable. It’s never supposed to touch the public internet.
Later, the company pushes a firmware update that activates a dormant Wi-Fi chip inside the device. This seemingly minor change allows the sensor to connect directly to the internet for remote monitoring.
This is a textbook substantial modification. The original intended purpose was local monitoring in a physically secure, isolated environment.
- Change in Context of Use: The update drags the product from a controlled private network into the hostile, open environment of the public internet.
- Impact on Security Compliance: This instantly creates a massive new attack surface. The security controls that were perfectly adequate for an isolated device are now dangerously insufficient for one exposed to global threats. This directly impacts compliance with the CRA’s essential security requirements.
From a cybersecurity standpoint, this update has created an entirely new product. The manufacturer must now perform a full conformity re-assessment to prove it can withstand the threats of its new, internet-facing role.
Hardware Modification Swapping a Critical Component
Finally, let’s look at a hardware change that trips the wire. A company builds a popular smart lock for homes. A key part of its security architecture, and a central feature in its CRA technical file, is a certified secure element (SE) chip that stores cryptographic keys.
To cut costs, the product team decides to swap out the high-quality SE for a cheaper, general-purpose microcontroller that handles cryptography in software. To the end-user, the lock looks and works exactly the same.
Under the surface, however, this is a major substantial modification.
The intended purpose—locking a door—hasn’t changed at all. But the product’s ability to meet the CRA’s essential security requirements has been critically weakened. The original SE provided hardware-level protection against physical tampering and sophisticated side-channel attacks. The new, cheaper component offers no such guarantees, making the all-important cryptographic keys far more vulnerable.
This change invalidates the security claims made in the original conformity assessment. The manufacturer must go back to the beginning and re-certify the product with its new, less secure internal architecture.
Consequences of Making a Substantial Modification
So, you’ve made a change to your product. The big question is: does it count as a substantial modification under the Cyber Resilience Act? If the answer is yes, this isn’t just a minor administrative task—it’s a full compliance reset.
Making a substantial modification sets off a chain reaction of duties. It effectively treats your updated product as if it were brand new, forcing you to re-validate its security from the ground up.
The moment a change gets this classification, the person or company that made it takes on all the legal responsibilities of the original manufacturer. This is a critical point. Even if you’re an importer, a distributor, or a third-party integrator, making that change puts you squarely in the manufacturer’s shoes, along with every single obligation that comes with the title.
The Compliance Domino Effect
The most immediate consequence is that the product must undergo a completely new conformity assessment. The original assessment, along with all its supporting evidence and documentation, is no longer valid for the modified product. You have to start the entire process over again to prove the product meets the CRA’s essential cybersecurity requirements.
This isn’t just a paperwork exercise. It means a deep re-evaluation of the product’s security architecture, its risk profile, and how it handles data. Following this new assessment, you must create and sign a new EU Declaration of Conformity for the modified version. Our detailed guide on the CRA Declaration of Conformity explains the specific requirements for this document.
Overhauling Your Technical Documentation
Alongside the new assessment, your technical documentation needs a complete overhaul. You can’t just add an addendum; you must update the entire file to reflect the product’s new state. This includes:
- Revising the product description to include its new intended purpose or features.
- Updating the risk assessment to account for any new threats and vulnerabilities introduced by the modification.
- Documenting the new security architecture, including any new components or changed configurations.
- Providing evidence from the new conformity assessment to support your compliance claims.
This reset ensures that market surveillance authorities have a complete and accurate picture of the product as it currently exists on the market, not as it was originally designed.
Practical Example: The entity performing a substantial modification inherits the full legal weight of a manufacturer under the CRA. For instance, if a car mechanic flashes the engine control unit (ECU) of a car with software that fundamentally changes its performance and emissions controls, that mechanic may be deemed the manufacturer of the modified ECU, bearing all CRA obligations for that change. This underscores why correctly classifying a change is one of the most critical decisions a company can make.
The Impact on Hardware and Supply Chains
This principle extends deep into the supply chain, creating complex challenges. For hardware manufacturers, substantial modification rules apply not only to firmware and software but also to hardware revisions.
Practical Example: A manufacturer of network routers faces a chip shortage and decides to replace the original network interface controller (NIC) with a different, uncertified one from a new supplier. Even if it seems functionally equivalent, this hardware swap is a substantial modification because the security properties of the new chip have not been assessed, potentially introducing new vulnerabilities. This triggers a full reassessment and can seriously complicate compliance across distributed EU supply chains.
Ultimately, a substantial modification is a high-stakes event. It demands a significant investment of time and resources to re-establish compliance and carries serious legal responsibility. This makes the initial assessment of any product change a crucial step in managing your regulatory risk under the CRA.
A Simple Checklist for Assessing Product Changes
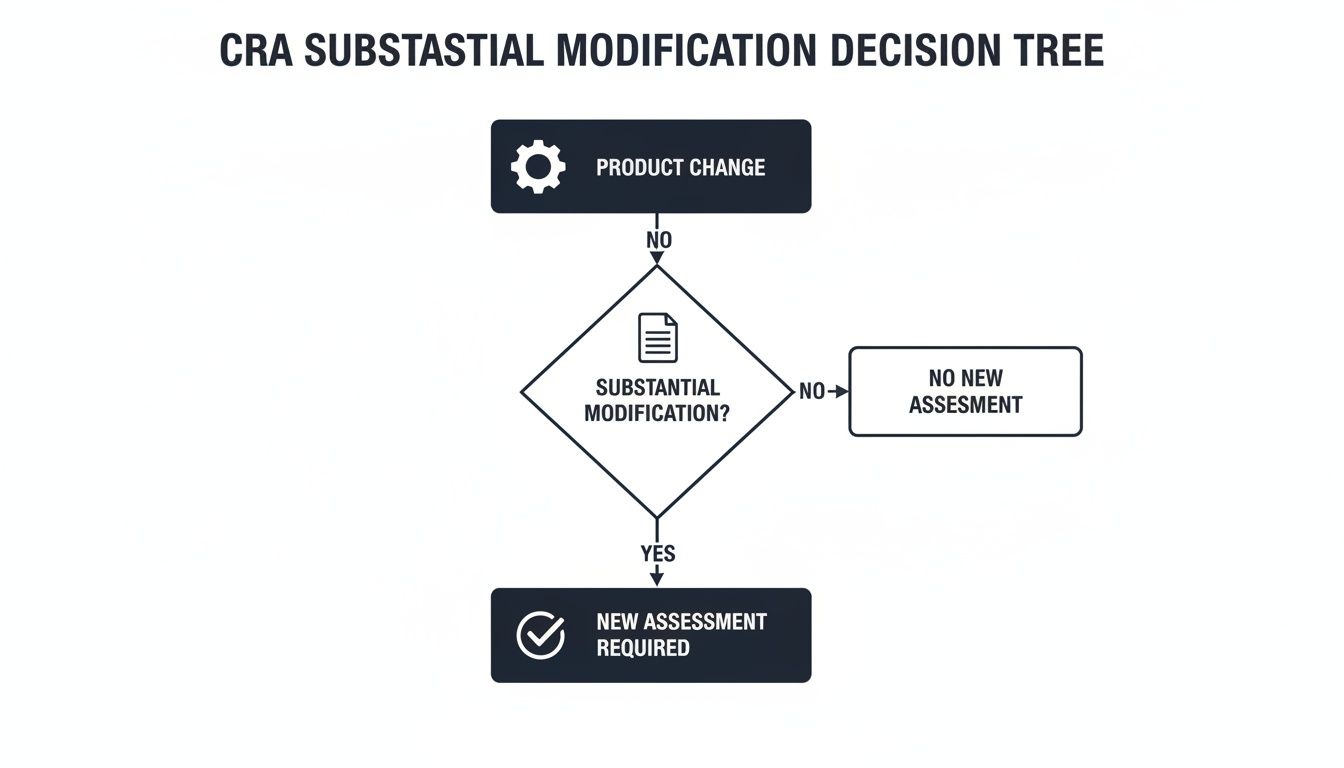
The decision tree above gives you the high-level workflow. Every change you make to a product has to be scrutinised to see if it’s substantial, which in turn dictates whether you need a new conformity assessment. This visual flow highlights why a structured evaluation process is so critical for every single update.
Of course, moving from a flowchart to your daily workflow is what really matters for consistent compliance. To figure out if a planned update crosses into substantial territory, your team needs a simple, repeatable process. This checklist offers a series of direct questions to guide your internal assessment for any proposed change.
Answering “yes” to any of these questions is a strong signal that you are dealing with a substantial modification. That means you’ll most likely need to perform a new conformity assessment and take on all the manufacturer’s obligations for the modified product.
Question 1: Does the Change Alter the Original Intended Purpose?
The intended purpose is the bedrock of your original CRA compliance. Any change that expands this scope demands careful review. You need to ask if the update allows the product to be used in a new environment, for a completely different task, or by a new type of user.
Practical Example: A ‘yes’ here is a major red flag. Imagine updating a consumer-grade smart plug with firmware that lets it manage high-load industrial machinery. This changes its intended purpose from simple home convenience to factory automation, fundamentally altering the product’s risk profile and making your original assessment invalid.
Question 2: Does It Introduce New Ways of Handling Data?
Data is the lifeblood of cybersecurity. You absolutely must ask if the change alters how the product collects, processes, or transmits data—especially personal or sensitive information. Does it start gathering a new category of data that wasn’t covered in your original assessment?
Practical Example: A fitness tracking app gets an update to collect detailed GPS location history to suggest new running routes. Previously, it only tracked steps and heart rate. That’s a clear ‘yes’. The app now handles sensitive geolocation data, creating new privacy and security risks that demand a fresh assessment to stay compliant with the CRA.
Question 3: Does It Weaken or Remove a Security Feature?
Sometimes, changes are made to boost performance or improve usability, but they come at the expense of security. You have to scrutinise any update that disables, bypasses, or weakens an existing security control, such as encryption, access controls, or secure boot mechanisms.
Practical Example: To simplify user login, a software update for a business application replaces mandatory two-factor authentication (2FA) with a simple username/password system. This is a substantial modification because it removes a critical security control, directly weakening the product’s security posture. A good guide on mastering information security risk assessment can help you evaluate these risks systematically.
Question 4: Does It Add a New Third-Party Component?
Modern products are built on incredibly complex supply chains. Ask whether your update integrates a new third-party software library, a hardware component, or an API. If it does, you are effectively inheriting the security posture of that component.
Practical Example: A video-conferencing application adds a new AI-powered transcription feature by integrating an open-source library from an unknown developer. If this library has not been properly vetted for security vulnerabilities, its inclusion could introduce significant new risks into the application, potentially qualifying the update as a substantial modification.
A ‘yes’ means you must perform due diligence on the new component’s security. By creating a structured process around these questions, you build a defensible and repeatable workflow. For a more exhaustive set of checks, you might be interested in our complete CRA compliance checklist to guide your team.
How to Streamline Your CRA Compliance Process
Trying to manage your Cyber Resilience Act compliance using spreadsheets and manual trackers is a recipe for trouble. It’s not just inefficient; it’s risky. Deciding whether a change is a routine update or a substantial modification demands a consistent, documented process—something that’s incredibly difficult to maintain by hand. This is where a dedicated compliance platform stops being a luxury and becomes a core part of your strategy.
A platform like Regulus is built to manage this exact kind of complexity. Its primary job is to help you create a clear, official baseline for each product. By documenting the product’s original intended purpose and security features in one central place, you build a solid foundation to measure all future changes against.
Establishing a Clear Baseline
The first step toward simplifying compliance is to nail down what your product is supposed to do. Without a clearly defined intended purpose, every change turns into a subjective argument. A compliance platform provides built-in documentation templates and evidence management tools to formalise this baseline.
This process gives your team clarity, cuts down on human error, and creates a robust audit trail for market authorities.
The platform screenshot below shows how requirements can be mapped and tracked, giving you a clear view of your compliance status at a glance.
This dashboard centralises all CRA obligations, making it easy to see which requirements are met and which still need attention.
Automating the Assessment of Changes
Once your baseline is set, the platform can help flag proposed changes that are likely to be considered substantial. As organisations prepare for the December 11, 2027, deadline, they are building systematic ways to categorise every product change. A platform like Regulus assists by generating tailored requirement matrices that help differentiate permissible updates from substantial modifications needing a full reassessment. You can discover more insights about this and other aspects of the Cyber Resilience Act on cycode.com.
This structured approach turns the CRA substantial modification definition from an abstract legal concept into a practical, data-driven workflow. Instead of relying on guesswork, your team can assess changes against a pre-defined set of criteria.
- Requirements Matrix: Instantly see how a proposed change affects your product’s compliance with Annex I requirements.
- Documentation Templates: Use ready-made templates to document your assessment, justifying why a change is or is not substantial.
- Evidence Management: Link every decision back to concrete evidence, creating an audit trail that will stand up to scrutiny.
By adopting a tool like this, you shift from risky, ad-hoc decisions to a systematic and defensible process. This doesn’t just prepare you for market authority inspections; it gives you the confidence and efficiency needed to navigate the complexities of CRA compliance.
Common Questions About Substantial Modifications
Understanding the Cyber Resilience Act often comes down to a few critical definitions, and none is more important than ‘substantial modification’. Getting this wrong can turn a simple update into a full-blown compliance nightmare.
Here, we answer the common questions that product managers, compliance officers, and engineering leads grapple with when deciding if a change triggers a new conformity assessment.
Are Security Patches That Fix Vulnerabilities a Substantial Modification?
Generally, no. A patch that fixes a known vulnerability without changing the product’s core function or security architecture is just routine maintenance. In fact, the CRA requires you to do this as part of your post-market duties.
Practical Example: You discover a buffer overflow vulnerability (like CVE-2023-1234) in your smart thermostat’s firmware. Releasing a patch that corrects the flawed code to prevent the overflow is a non-substantial update. It simply restores the product’s security.
However, if fixing the vulnerability required you to remove the entire Wi-Fi module and force users to connect via Ethernet only, that would likely be a substantial modification because it fundamentally changes how the product operates.
Who Is Responsible if a Third Party Makes the Modification?
The responsibility falls squarely on whoever makes the change. The CRA is crystal clear on this: any person or company that performs a substantial modification is treated as the manufacturer of that newly-changed product.
Practical Example: An importer buys generic security cameras and installs their own custom AI software that adds facial recognition capabilities before selling them. The importer is now legally the “manufacturer” of this modified product. They must conduct a new conformity assessment, create all technical documentation, and issue a new Declaration of Conformity. The original camera maker is only responsible for the camera as they sold it, without the AI software.
Does Changing the User Interface Count as a Substantial Modification?
A purely cosmetic UI change—like updating colours, icon styles, or button layouts—is almost never a substantial modification. These changes don’t touch the product’s security posture or its intended purpose, so they don’t trigger a reassessment.
The story changes completely if the UI redesign adds new functionality. For example, if a new interface in a banking app adds a form to upload identity documents for verification, that is a substantial modification. It’s not a simple facelift; it introduces a new, high-risk data handling process that was not part of the original assessment.
How Should We Document Our Decision That a Change Is Not Substantial?
Meticulous record-keeping is your best defence. For every single product change, you need to document your assessment—especially when you conclude it is not substantial. This creates a defensible audit trail that shows regulators you’re performing due diligence.
Your technical file should contain a clear record of:
- The Change Itself: A straightforward description of the update or modification (e.g., “Software version 2.1: Updated button colors and patched CVE-2024-5678”).
- Your Analysis: An explanation of how you evaluated the change against the CRA’s two main triggers (e.g., “The change does not alter the intended purpose of home climate control. The patch only corrects a known vulnerability and does not weaken other security controls.”).
- The Justification: A written conclusion explaining precisely why the change was classified as a non-substantial update (e.g., “Conclusion: Update 2.1 is non-substantial as it is a minor UI tweak and a standard security fix.”).
This internal documentation proves you have a structured process and are actively managing your compliance obligations, not just hoping for the best.
Confidently assessing modifications and navigating the complexities of the CRA is far easier with the right tools. Regulus provides a structured platform to document your product’s intended purpose, manage technical files, and create a clear, auditable trail for every decision. Explore how Regulus can bring clarity to your compliance workflow and reduce risk.



